How to remove malware viruses
Malware is the term defining a variety of cyber threats. They comprise trojans, worms, rootkits, backdoors, ransomware, and PUPs (potentially unwanted programs). They exploit various strategies to infect users‘ devices. Anti-malware applications are capable of properly confronting cyber infections and ensure their full termination. They ensure prevention as well. Cyber threats are mainly exploited as means to get remote access to the victims‘ computers and steal confidential information. The hackers find elaborate ways how to earn money not only by wheedling out personal data but by convincing users to buy futile and malicious software. Ransomware viruses are especially profitable tools of maximising revenue since they encrypt valuable files. In contrast to these threats, adware-type programs or browser hijackers are fairly harmless. Their manifestation is expressed through pay-per-click advertisements, coupons, and banners. This activity earns the developers money while users have to deal with adware removal. More elaborate versions of malware might avoid the detection of security applications, renew themselves, and even install additionally fishy applications.
When was the first virus recorded?
There are thousands of stories when good intentions lead to disastrous or simply destructive consequences. The first virus perfectly illustrates this statement. Two Pakistani brothers, Basit Farooq Alvi and Amjad Farooq Alvi, are regarded as the fathers of the cyber threat. Little did they know that their intention to teach the felons, who distributed the illegal copies of the software, created by the brothers, would evolve into a mass cyber business. Likewise, first-ever virus, Brain, came into daylight. It plagued IBM computers via floppy disks. The behaviour of this cyber infection was mainly limited to the appearance of frustrating notifications.
As the years passed, more bright computer-literate people decided to make the advantage of cyber infections. In 1991, Michelangelo virus was released. It belonged to the boot –sector cyber threats. March 6th was the day when more than 5 million users could not turn on their computers. The virus was able to infect all floppy disks attached to the device. Thus, this threat gave new inspiration for other hackers. After entering the new millennium, the cyber infections greatly improved. Botnets – networks of machines distributing cyber infections – were created. Soon afterward, insidious trojans, backdoors, and even file-encrypting malware started to appear.
The transmission tendencies
The distribution techniques are not less intriguing as the viruses themselves. We will review the most prevalent malware spreading techniques:
- Illegal or infected domains. This method is perhaps the oldest and most common one. It still retains its popularity among the hackers as they place their malignant ‘products’ in the web pages with pornographic content or file-sharing website. Surprisingly, legitimate web pages do not escape the attention of cyber criminals since they are able to compromise the latter by attaching infected scripts.
- Malevolent spam emails and attached files. This technique mainly encompasses previously mentioned botnets which automatically send thousands of infected attachments to computers. One of the key characteristics of this felony is that such emails are often disguised as tax reports or invoices. Without being aware of danger lying in such attached files, credulous users open them only to find out a virus later on their devices. This technique is especially prevalent among ransomware developers. Locky virus, being one of the well-known samples of this category, also utilizes this strategy.
- Malvertising. Cyber infections target new victims via infected advertisements and links as well. Fraudsters enwrap their viruses as the fake updates of official and well-known legitimate programs. You might even fail to escape cyber infection by downloading a seemingly ordinary mini game or reviewing the commercial offer. It becomes only a matter of time when a virus is downloaded and starts its mischief.
- Other means. There is a variety of other cyber threats, such as trojans, rogue malware, rootkits, backdoors, etc. each of them slightly differs in their operation. However, few users enjoy encountering either of them as they cause irritation if not more severe consequences.
The modus operandi of malware
Depending on the type of malware, its symptoms differ. Some of the most distinctive features include forged security messages and fake warning notifications. If you notice these alerts, then rogue anti-spyware or ransomware threats might be residing in your system. The felony of former programs includes persuading victims that their devices are heavily infected with the cyber threats. Such fake messages are supposed to encourage victims to purchase the full version of futile programs. The latter category, ransomware threats, demands money in exchange for the encrypted files. They utilize complex encryption algorithms to lock the data. Following the process, distinctive extensions are appended to the corrupted data.
Other groups of malicious applications and tools are considered to be browser hijackers and adware. The latter usually generate bothersome pop-ups which disturb daily browsing sessions by emerging here and there. Hijackers aim to direct you to sponsored domains. By misguiding you to the affiliated web pages, the developers earn quite a delicate amount of money depending on the number of clicks and views. These groups are not regarded as severe cyber threats, but they are likely to cause highly disturbing outcomes. Slower PC processing capabilities are the primary signs of malware infection. Such underperformance hardly suggests you which type of the threat occupied the device. Trojans, keyloggers, rogue anti-spyware, ransomware, might be at fault for causing such symptoms. Needless to say that these infections take up huge energy and performance resources. Some of them might even escape the detection of an anti-virus program or interfere with their effectiveness.
Samples of viruses
PC Optimizer Pro. Regarding its features, it falls under the categorization of fake PC optimization tools. Usually, similar programs display a significantly high number of PC issues to convince you to buy the full version. After downloading it, you get bewildered. The full version either ‘magically’ solves the issues or fails to do that.
COM surrogate virus. This virus is a trojan. It other words, it disguises as a legitimate file and infiltrates the system without getting terminated by a security application. Later on, it starts collecting vital information, such as account password and login data to a bank account. They might also facilitate cyber criminals to access your device remotely and cause a system crash.
DNS Unlocker. Though this virus belongs to the group of adware, its presence should not be ignored. Besides flooding the computer screen with disturbing commercial offers, it meddles with the browser settings. In other words, it can easily monitor the traffic of your browsing. The threat is suspected of compiling information about your online activities. Lastly, this data might be misused for marketing purposes.
Is it difficult to terminate malware?
Security applications, such as anti-virus and anti-malware, are the most efficient tools battling the cyber threats. They quickly identify the sort of infection and apply a necessary action to remove it properly. Since modern viruses vary in their degree in complexity security, manual removal might fail. In case the tools did not eliminate the threat completely, perform the following steps:
• Reinstall the security application. Change the file name and start the process again.
• Restart the device and shift to Safe Mode and reinstall the security program. Update it manually.
• Install additional anti-malware tool
• Inquire Novirus tech support team using ‘Ask Us’ function
Latest malware added to the database
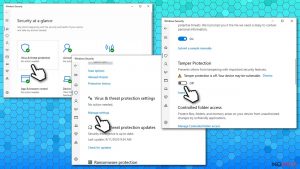
Remove VirTool:Win32/DefenderTamperingRestore
Terminate Win32:BogEnt
IDP.Generic virus removal tutorial
Additional information added on 2016-10-25