Remove “Your Chrome is severely damaged by 13 Malware!” scam (fake) - Free Removal Guide
“Your Chrome is severely damaged by 13 Malware!” scam Removal Guide
Description of “Your Chrome is severely damaged by 13 Malware!” scam
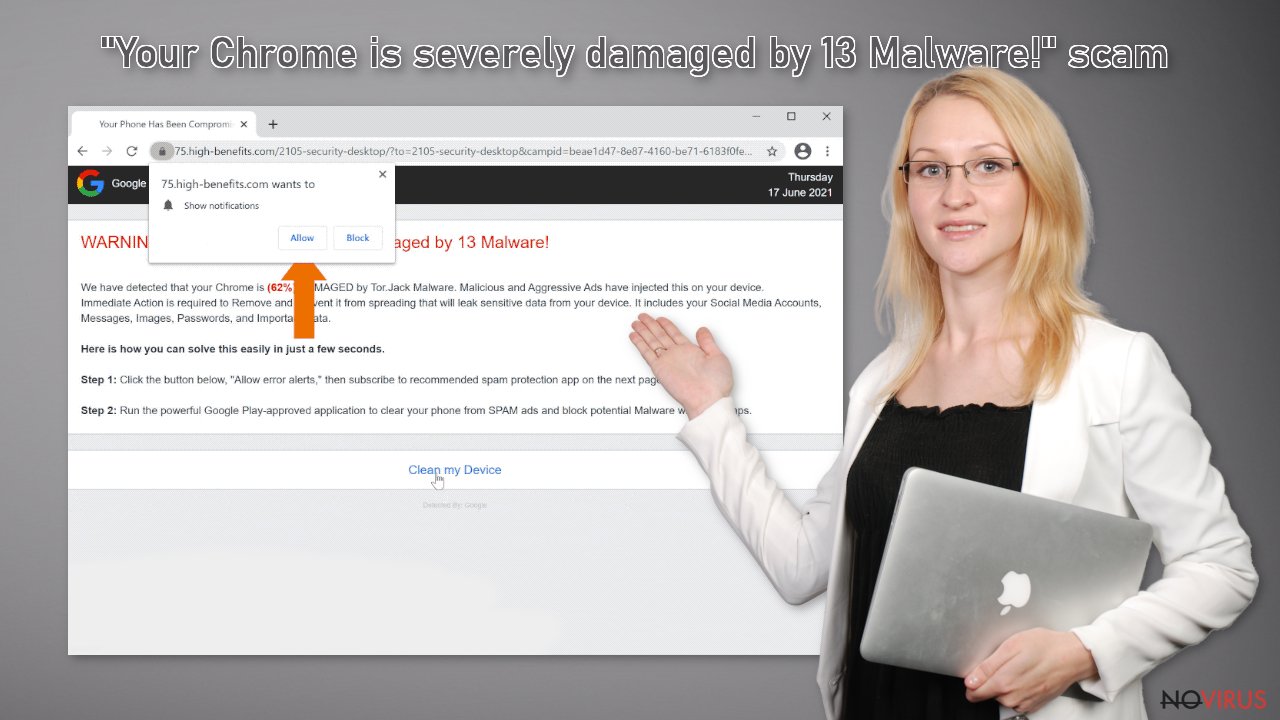
“Your Chrome is severely damaged by 13 Malware!” is a scam that uses the Google brand to look more trustworthy
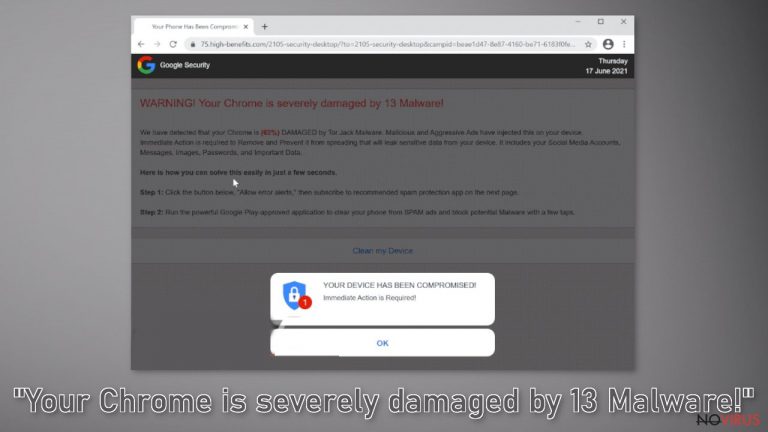
“Your Chrome is severely damaged by 13 Malware!” is a scam designed to look like a security warning from Google to deceive more users. In fact, a well-known brand has nothing to do with this deceptive campaign. It was created by scammers to take advantage of less IT savvy users. This page displays a fake alert trying to convince users that their computer is infected with multiple malware. This way, users rush to press a button and cause problems for their device.
The scam is specifically designed for Chrome users, so the message may seem more reliable to many. However, while a virus alert isn’t true, users may pose a real threat to their device by taking any action on this fraudulent website.
The page may start sending unwanted, extremely annoying pop-up ads that appear even when you close your browser. People can also be tricked and tempted to provide personal information, download potentially unwanted programs (PUPs) and even serious viruses that can damage the device or personal files. Scammers can infect your devices with adware, trojans, ransomware and other problems, so it's best not to risk and not rely on such a page.
Sadly, the Internet is full of scams like “Your Chrome is severely damaged by 13 Malware!”. For example, you probably heard about “Windows Defender Security Center” or “You need to update your browser to view the content.” They are rarely found in search results.
| NAME | Your Chrome is severely damaged by 13 Malware! |
| TYPE | Online scam; adware |
| SYMPTOMS | A fake message appears asking users to subscribe to obscure services, download fake programs because their system is allegedly infected with a virus |
| DISTRIBUTION | Shady websites, rogue advertising networks, freeware installations |
| DANGERS | Users can infect their devices with potentially unwanted programs and access dangerous pages |
| ELIMINATION | Uninstall the plug-in through your browser settings; it is recommended that you perform a scan using reliable anti-malware tools |
| FURTHER STEPS | Use a powerful device maintenance tool, such as FortectIntego, to remove the remaining damage and optimize your computer |
It spreads similar to other scams
Most people get caught by fake notifications when they are browsing other suspicious websites. Pages that engage in illegal activities are unregulated and contain a lot of fraudulent ads and secret redirects. Illegal streaming platforms, torrent sites, and file-sharing platforms display fake “Download” and “Play” buttons that can direct users to pages created by scammers.
It is important to visit only those pages that you know and trust. Never click the “Allow” button without fully understanding what permissions you are granting. There are also many legitimate streaming services to choose from, such as Netflix or Hulu. Such pages require only a small subscription fee, and users can use all the content they offer as much as they want. A small fee is far better than a constant risk.
Also, there is a possibility that the Chrome scam appeared without any user intervention. This can happen if your computer is infected with adware. It can increase the amount of commercial content, such as pop-ups, banners, and redirects. Follow the removal guide below to get rid of any intruders.
You can easily stop annoying pop-ups and hijackers
It has been reported that the “Your Chrome is severely damaged by 13 Malware!” scam is causing pop-up messages. Scammers can use rogue ad networks that place ads that lead to dangerous websites. We recommend disabling pop-ups immediately. Do not use such ads or click on embedded links. Because instant pop-ups are subscription-based, you'll need to turn them off yourself:
Eliminate extensions and applications from Google Chrome (desktop):
- Go to Menu on Google Chrome and choose Settings.
- Scroll down to Advanced.
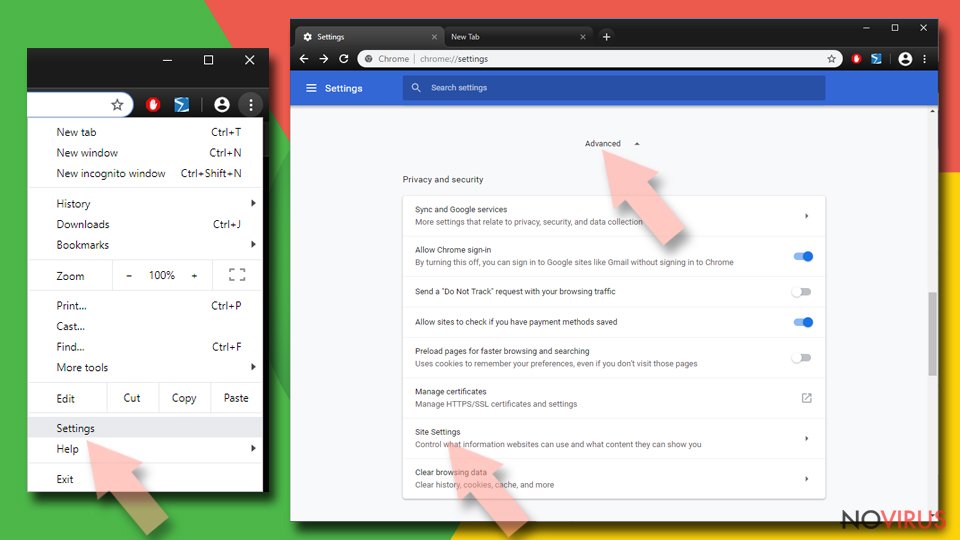
- Locate the Privacy and Security section.
- Choose Site Settings and go to Notifications.
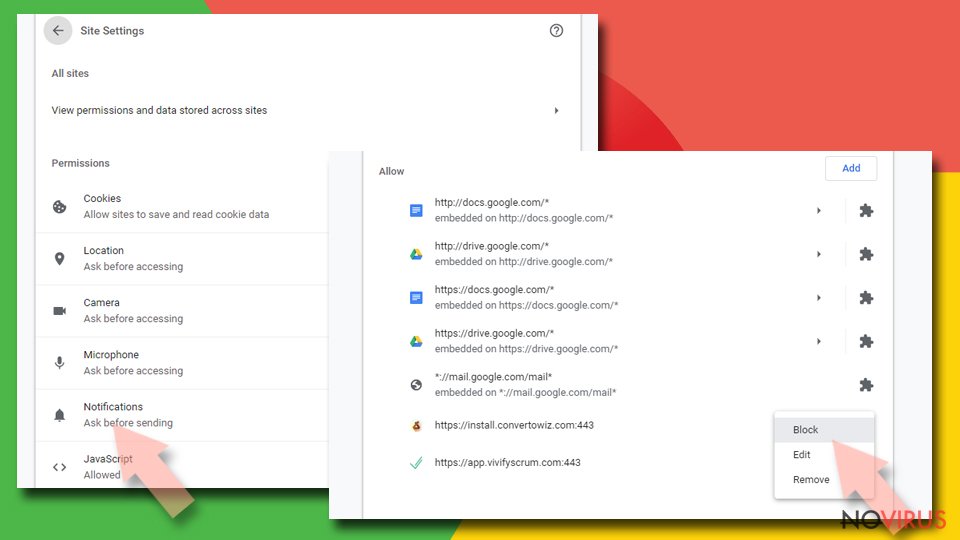
- Unwanted URLs can be found in Allow section if it annoys you.
- Click the three vertical dots next to the site and pick Block to remove unwanted notifications from Google Chrome.
Stop notifications from Google Chrome on Android:
- Open Google Chrome browser and tap on three vertical dots.
- Select Notifications.
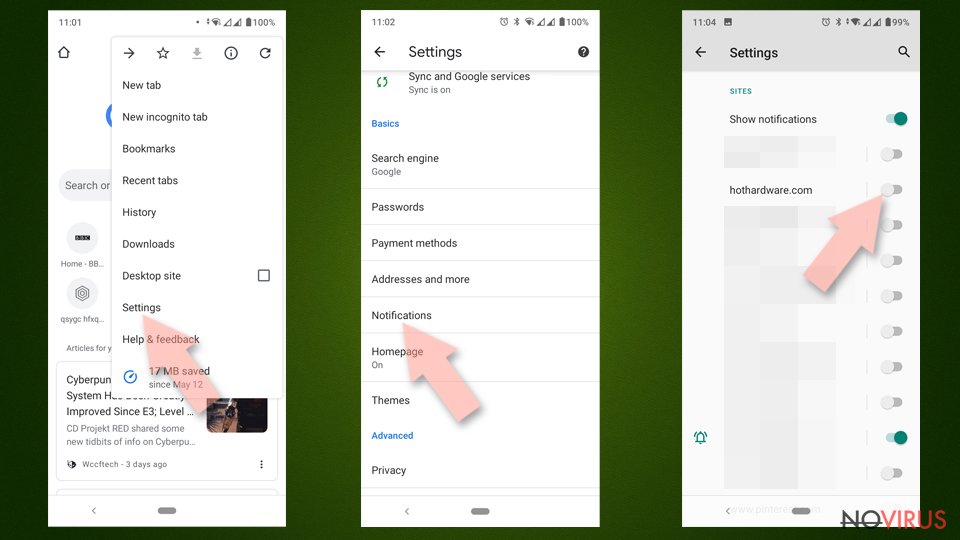
- Find Sites section.
- Locate the suspicious sites and toggle the button to the left to Off.
The scam site may have installed a browser extension. This can lead to specific suspicious symptoms, such as changes to your browser settings, including your homepage, new tab address, and search engine. You can remove browser add-ons by going to settings. Find the list of extensions installed in your browser and remove them one by one to see if you notice any changes. If you don't know how to do this, you can find the answer in the instructions below:
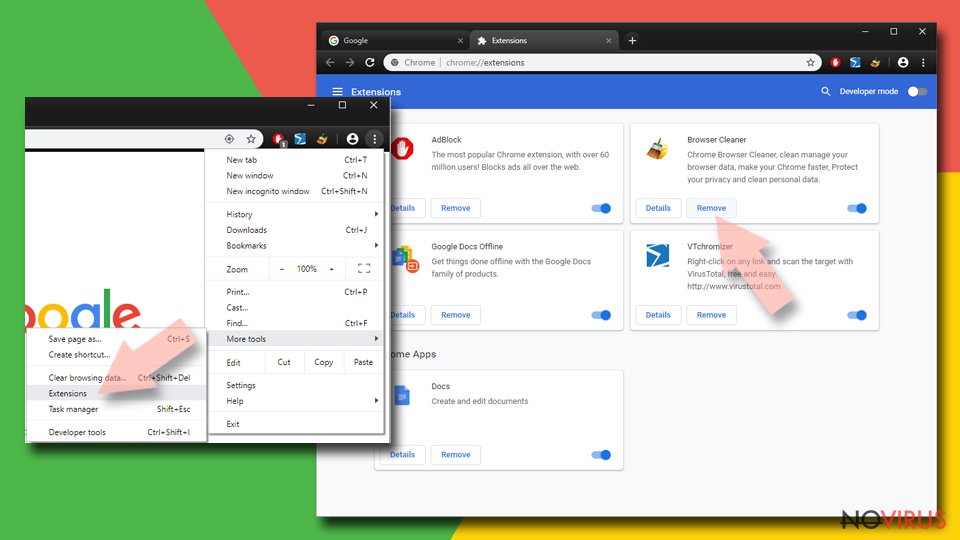
Find and remove suspicious extensions from Google Chrome:
- In Google Chrome, open the Menu by clicking three vertical dots at the top-right corner.
- Select More tools > Extensions.
- Once the window opens, you will see all the installed extensions.
- Find any suspicious add-ons related to any PUP.
- Uninstall them by clicking Remove.
Remember to clear your cookies and remove all PUPs
Websites and web applications can track user activity and collect personal data using cookies, such as IP address, geographic location, pages they visit, links they click, and goods they buy online. Many websites use this information to personalize the user experience, but it can also be used for profit.
This means that your data may be accessible to ad networks or other third parties. Security experts recommend cleaning your browsers regularly. You can use a dedicated maintenance tool, such as FortectIntego, that can automatically get rid of cookies and cache. This powerful program can also fix various system errors, corrupted files, and registry problems, which is especially useful when infected with a virus.
If you've taken all of the previous steps but still notice unwanted symptoms, the adware may be hidden on your device. It usually enters the system from free application distribution platforms. Such platforms often include additional applications in the installation package without explicitly disclosing this.
It is best to use official online stores and developer websites when you want to install new software. You should also always choose Custom or Advanced installation methods, read the Privacy Policy and Terms of Use. The key is to check the list of files and check the boxes next to unrelated programs that you don't want to install.
An app that causes unwanted changes to your device can have any name or icon, as scammers often disguise them as “handy” tools. If you're not sure what to do and don't want to risk deleting the wrong files, we suggest using SpyHunter 5Combo Cleaner or Malwarebytes security tools to scan your device, remove infections, and prevent future infections by alerting you to potentially unwanted software. guessing to make any changes.
If you still want to fix the problem manually, here are the instructions for Windows and Mac devices:
Windows 10/8:
- Type Control Panel into Windows search and once the result shows up hit Enter.
- Under Programs, choose Uninstall a program.
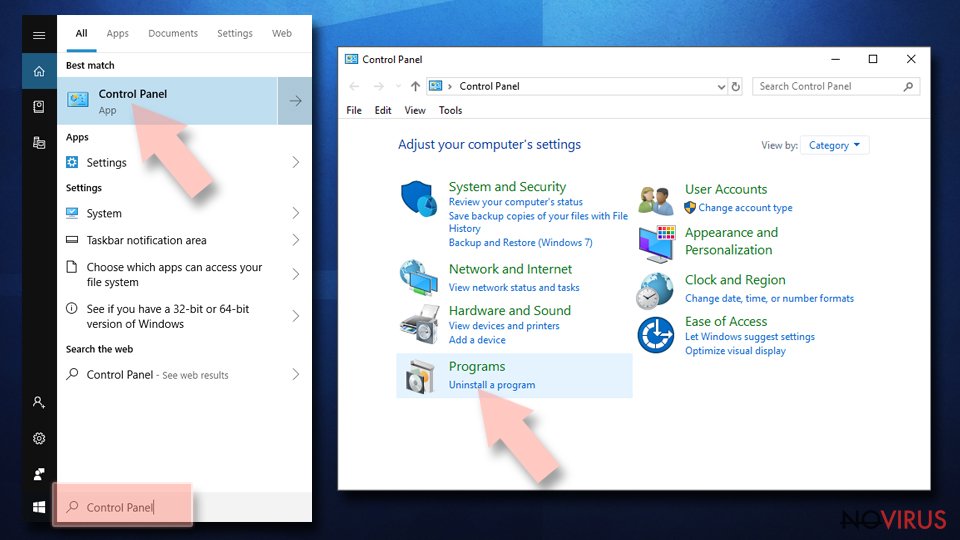
- Find components related to suspicious programs.
- Right-click on the application and select Uninstall.
- Click Yes when User Account Control shows up.
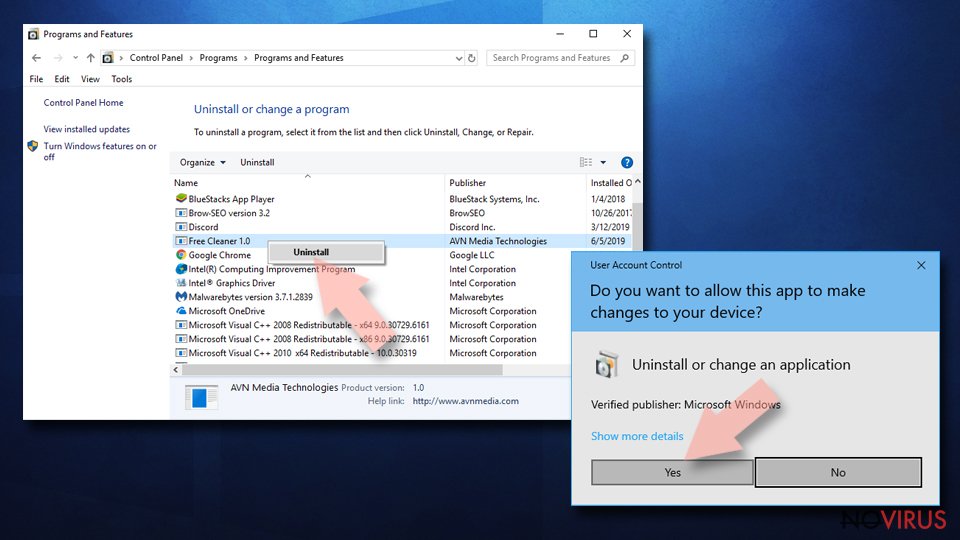
- Wait for the process of uninstallation to be done and click OK.
Windows 7/XP instructions:
- Click on Windows Start and go to Control Panel on the right pane.
- Choose Add/Remove Programs.
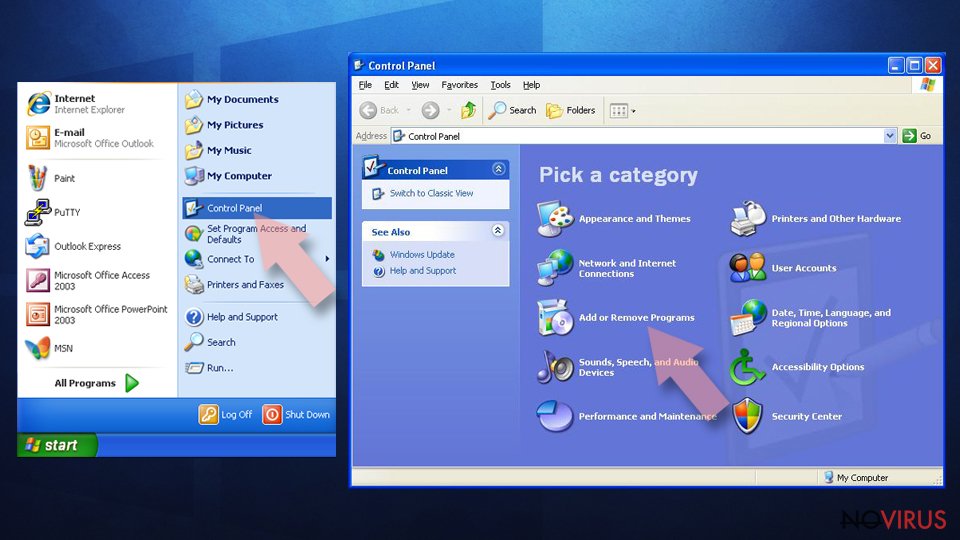
- Select Uninstall a program under Programs in Control Panel.
- Click once on the unwanted application.
- Click Uninstall/Change at the top.
- Confirm with Yes.
- Click OK and finish the removal.
MacOS:
- From the menu bar, select Go > Applications.
- In the Applications folder, look for all related entries.
- Click on the app and drag it to Trash (or right-click and pick Move to Trash)
To fully remove an unwanted app, you need to access Application Support, LaunchAgents, and LaunchDaemons folders and delete relevant files:
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- In the Application Support folder, look for any dubious entries and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and terminate all the related .plist files.
How to prevent from getting adware
Securely connect to your website wherever you are
Sometimes you may need to log in to a content management system or server more often, especially if you are actively working on a blog, website, or different project that needs constant maintenance or that requires frequent content updates or other changes. Avoiding this problem can be easy if you choose a dedicated/fixed IP address. It's a static IP address that only belongs to a specific device and does not change when you are in different locations.
VPN service providers such as Private Internet Access can help you with these settings. This tool can help you control your online reputation and successfully manage your projects wherever you are. It is important to prevent different IP addresses from connecting to your website. With a dedicated/fixed IP address, VPN service, and secure access to a content management system, your project will remain secure.
Reduce the threat of viruses by backing up your data
Due to their own careless behavior, computer users can suffer various losses caused by cyber infections. Viruses can affect the functionality of the software or directly corrupt data on your system by encrypting it. These problems can disrupt the system and cause you to lose personal data permanently. There is no such threat if you have the latest backups, as you can easily recover lost data and get back to work.
It is recommended to update the backups in parallel each time the system is modified. This way, you will be able to access the latest saved data after an unexpected virus attack or system failure. By having the latest copies of important documents and projects, you will avoid serious inconveniences. File backups are especially useful if malware attacks your system unexpectedly. We recommend using the Data Recovery Pro program to restore the system.
