Uninstall Zfdv virus (virus) - Quick Decryption Solution
Zfdv virus Removal Guide
Description of Zfdv ransomware
Zfdv ransomware is an infection that spreads quickly on the system and locks user files
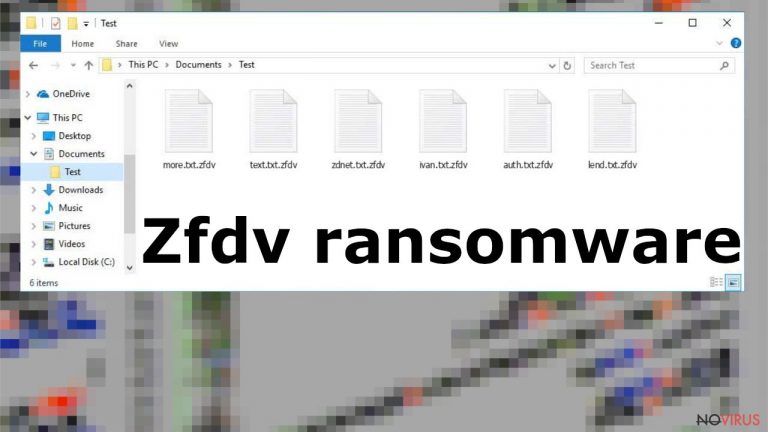
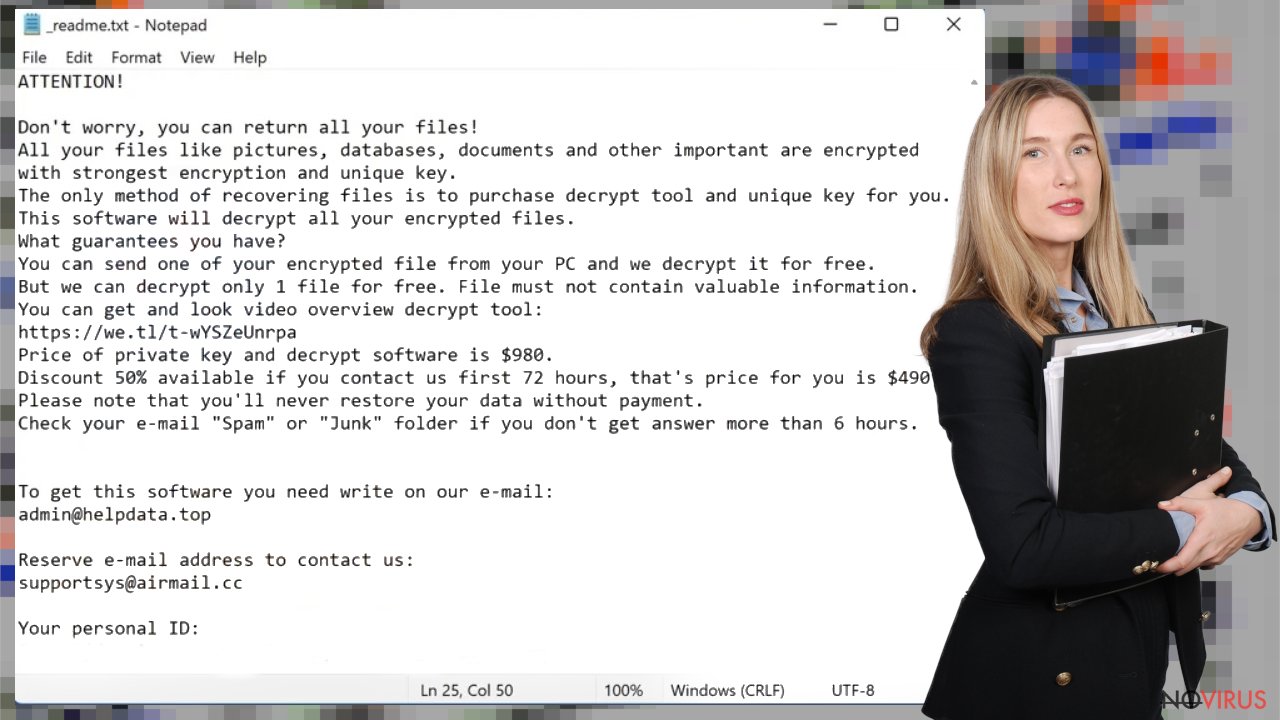
The Zfdv file virus is a type of ransomware infection that uses sophisticated encryption to cause direct damage to the files on your computer, prompting victims to pay the required ransom. This claim is made using the _readme.txt ransom note. This is the message from cybercriminals who created the virus to easily profit from users who no longer have access to their personal files that are critical to them.
Criminals encrypt commonly used files and data that can be valuable to the victim. Zfdv ransomware virus encrypts documents, images, audio files, etc. In addition, this infection can alter or corrupt some system data to ensure its successful operation, resulting in reduced computer performance, various errors, and other crashes.
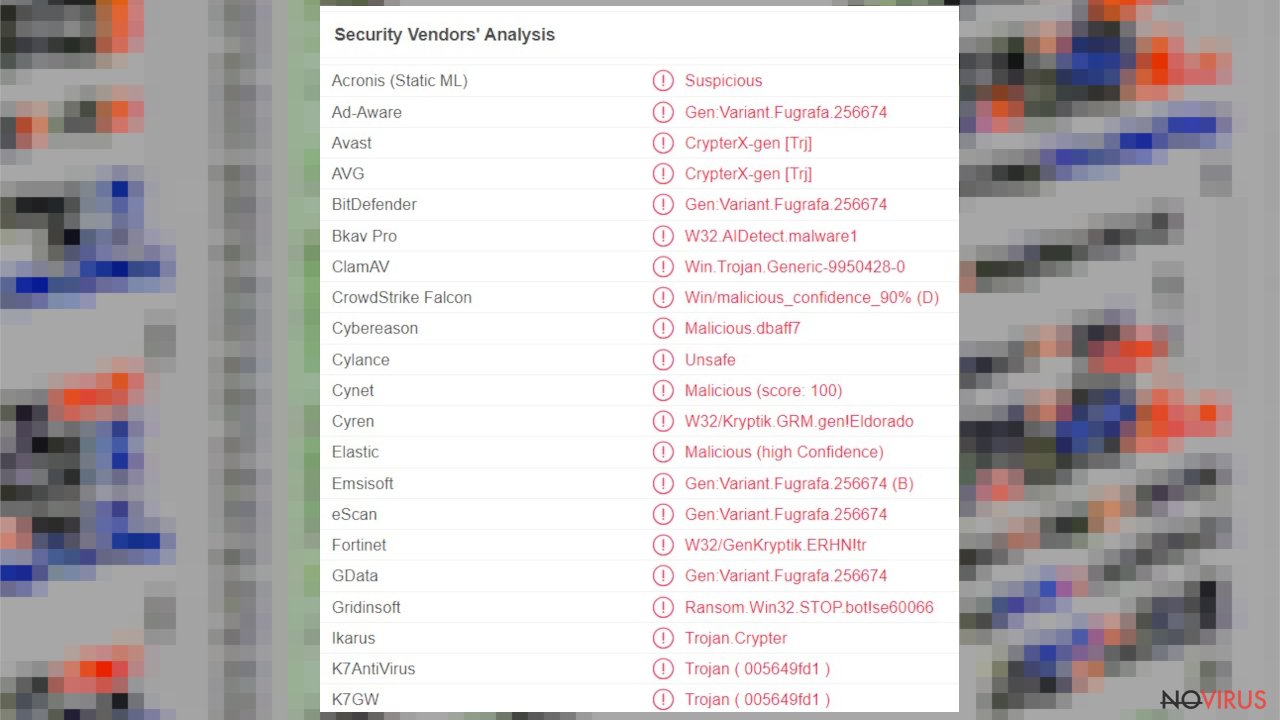
Zfdv virus can harm your computer system by performing additional malicious processes and installing other infections that control the performance of your computer. Trojans and other malware entering the system can further damage an already problematic device. So it is important to understand that locking personal files alone is not the only problem caused by a ransomware virus.
The Zfdv file virus is not a new threat as it comes from a family of infections known since 2018. This is the latest version of specific ransomware that cannot be decrypted. The developers of Ransomware change some of the threat features and code, but the ransom note and the message in the text file remain the same. While this is one of the most devastating infection types out there, you should not immediately panic and definitely not instantly hand your money to cybercriminals. In this article, we will explain the correct way of handling the situation – delete the virus, attempt to restore files in alternative ways, and repair damaged system components.
| Name | Zfdv ransomware |
|---|---|
| Type | Cryptovirus, file-locker virus |
| Family | Djvu ransomware |
| Marker | .zfdv |
| Distribution | This infection is spread through pirated software or game packages, spam emails attachments |
| Contact information | admin@helpdata.top, supportsys@airmail.cc |
| Ransom amount | Cybercriminals demand to pay $ 490. After 72 hours, that amount doubles to $ 980 |
| Ransom note | _readme.txt |
| Elimination | This threat can be eliminated with a reliable antivirus program |
| Repair | With a program like FortectIntego, you can automatically fix corrupted system files |
Cybercriminals are trying to persuade people to pay the required ransom by promising to send a decryption tool for the money. They even offer to decrypt any trial file for free, as this will gain the trust of the victims. However, even if you pay the full required $ 980 in bitcoins, there is still no guarantee that the people who created this virus will actually send the decryption tool and it will really work. Unfortunately, cybercriminals often disappear as soon as they receive money, and .zfdv files remain locked. Or worse, they demand even more money after receiving the first payment.
Cyber security professionals are constantly alerting people about this threat. Once your files are encrypted, they can no longer be opened or used. The only way to recover encrypted data is to use a specific key or password held by cybercriminals. However, there is no guarantee that even after paying the ransom, the developers of the Zfdv ransomware virus will send the necessary tools, so it is not worth the risk and it is better not to contact them at all.
Ransomware is a serious virus that can quickly spread through your computer system and seriously affect your device. Unfortunately, this is because users often behave irresponsibly. For example, users download suspicious email attachments or click on a suspicious link, install pirated versions of programs, etc.
How to remove this threat
Zfdv ransomware virus damages the device, so the infection removal process is very important and necessary. You cannot restore files on a system that is still running this virus. This is risky and quite dangerous, as a ransomware program can encrypt newly added files even after the initial encryption.
To remove such a threat, you will need a security program that can detect Zfdv ransomware and other related or accidental threats. We suggest trying SpyHunter 5Combo Cleaner or Malwarebytes. When you run the AV program, you can scan your system and find any infected files. After successfully completing the scan and getting rid of the virus, you can re-scan the system to make sure that there are no residues left.
Sometimes these threats are spread through trojans and other infections, so deleting the virus with an antivirus program helps to remove not only the Zfdv file virus but also other threats. Do not pay the required ransom and do not even think about contacting the cyber criminals who caused this infection.
System repair and file recovery options
Zfdv ransomware can do a lot of damage and affect system files, functions and computer performance. These changes are made in order for the virus to successfully survive on the system and encrypt the files. The ransomware also works on certain features of the device, making it much harder to permanently remove this problem from your computer.
There are various files and programs that are affected by Zfdv ransomware, making it difficult for users to recover damaged files. These issues can severely affect the performance and security of your computer. This is why it is very important to get rid of the virus completely and make sure that all its remains are deleted.
When ransomware and other viruses infect the machine, various processes get affected. Windows registry entries, other directories, and databases of system files can get damaged or corrupted. Affected files can lead to additional system issues. Malware damage to such files triggers problems with performance and stability, and security issues. Windows operating system recovery is needed then.
You should rely on proper tools that are designed to repair such files, and recover smooth performance. FortectIntego is developed with the purpose to fix damaged files, repairing processes, and removing other pieces of malware that get leftover. The program has a few engines and databases where needed Windows files can be found and repaired. This application also wan fix errors related to registry, damaged DLLs, and other system files. You can find links where you can download this PC repair tool, then:
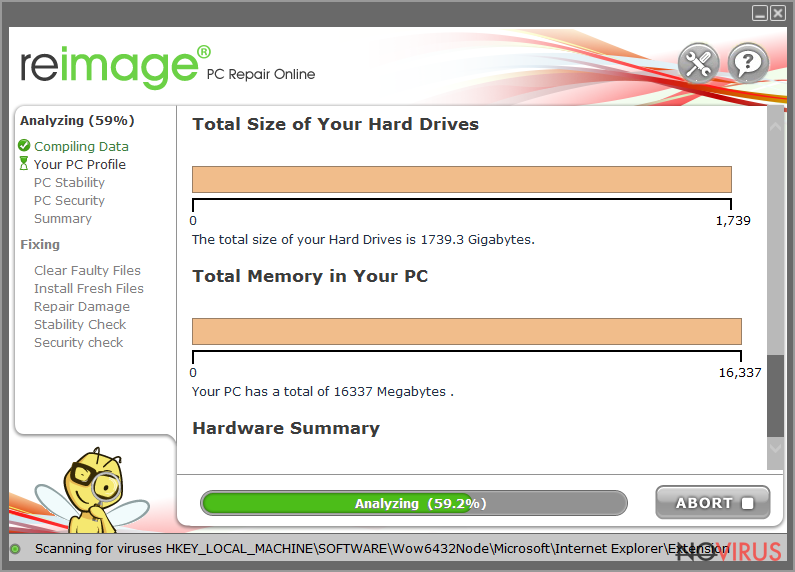
- Download the application by clicking on the link above
- Click on the ReimageRepair.exe

- Choose Yes when the User Account Control (UAC) shows up.
- Press Install and wait for the installation process.
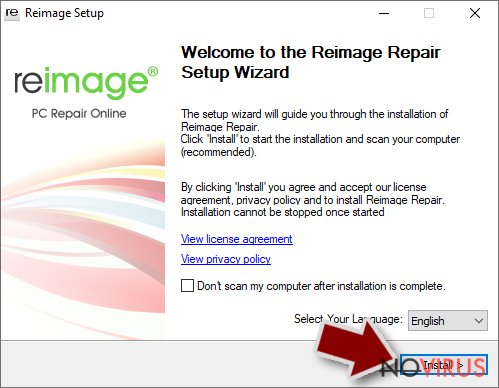
- The analysis of your machine with begin after the installation.
- Check the results listed in the Summary.
- You can choose each of the issues and fix them manually.
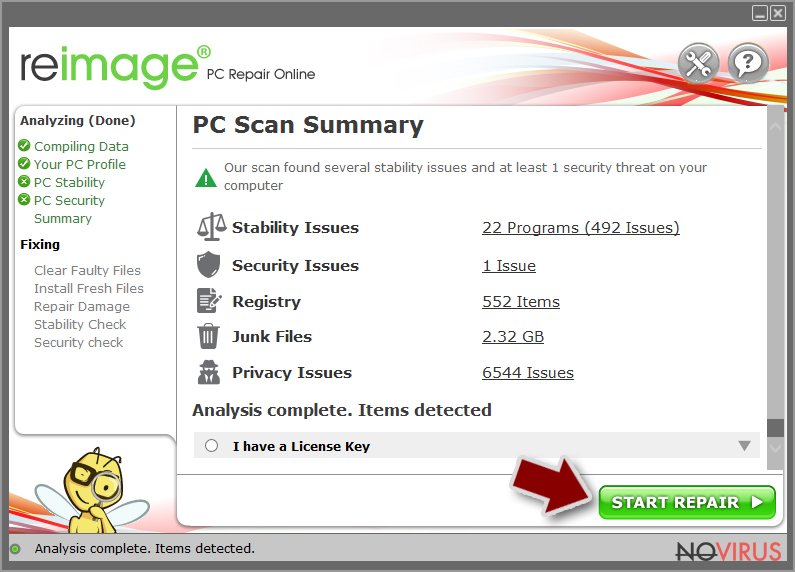
- If you see many problems that you find difficult to fix, we recommend you purchase the license and fix them automatically.
Using this software can save a lot of time for you and improve the performance of the machine. Various issues can get fixed and system errors solved by running a thorough system scan and repair. You can avoid manual file repair that when done incorrectly can trigger more serious damage. Automatic system repair means that you do not need to reinstall the OS or different files.
As we mentioned before, this ransomware is not new. The infection may have different contact emails and use different file markers, but in all other respects, the Zfdv virus is identical to older versions. Unfortunately, this means that the decryption options are limited due to the encryption keys used during the encryption process. However, you can still check one method that helps unlock files in some cases.
There is an option for some of the versions in this Djvu family – a decryption tool that works with offline ids. You should try using Emsisoft decryptor for Djvu/STOP. It is important to mention that this tool will not work for everyone due to malware methods of encrypting files differently.
Even if your case meets this condition, somebody from the victims has to pay criminals, retrieve an offline key, and then share it with security researchers at Emsisoft. As a result, you might not be able to restore the encrypted files immediately. Thus, if the decryptor says your data was locked with an offline ID but cannot be recovered currently, you should try later. You also need to upload a set of files – one encrypted and a healthy one to the company's servers before you proceed.
- Download the app from the official Emsisoft website.
- After pressing Download button, a small pop-up at the bottom, titled decrypt_STOPDjvu.exe should show up – click it.
- If User Account Control (UAC) message shows up, press Yes.
- Agree to License Terms by pressing Yes.
- After Disclaimer shows up, press OK.
- The tool should automatically populate the affected folders, although you can also do it by pressing Add folder at the bottom.
- Press Decrypt.
From here, there are three available outcomes:
- “Decrypted!” will be shown under files that were decrypted successfully – they are now usable again.
- “Error: Unable to decrypt file with ID:” means that the keys for this version of the virus have not yet been retrieved, so you should try later.
- “This ID appears to be an online ID, decryption is impossible” – you are unable to decrypt files with this tool.
Don’t pay cybercriminals and try to remove the virus as soon as possible. SpyHunter 5Combo Cleaner and Malwarebytes can help you get rid of the infection easily and quickly. Only after removing the virus, you can try to recover files that have been encrypted by this threat. System repair tools such as FortectIntego also help ensure that the remnants of the Zfdv file virus no longer damage the device, so that these affected files can be safely restored using backups.
Getting rid of Zfdv virus. Follow these steps
Software for file restoring
Data backups are important, but users tend to skip such an important step. Also, ransomware comes without notice, so many files affected by the threat can be the ones that haven't been backed up yet. paying the demanded ransom is not the solution, so trusting criminals is not the option for file recovery.
File recovery is a difficult thing, but it is possible to retrieve those files that get affected or encrypted, in some cases. It is highly related to the fact that there are many methods to lock files. The encryption algorithm used can determine if decryption is possible. Since there are thousands of ransomware strains, it is impossible to tell if any software will work for you.
We suggest trying the program regardless of which ransomware attacked your computer. Make sure to pay attention to some details before you begin:
- Note that encrypted data on your computer might get permanently damaged by security or data recovery software, you should first make backups of it to save crucial data.
- Make sure to recover your files using this method after you perform a thorough system scan with anti-malware software.
Install file recovery software
- Download Data Recovery Pro.
- Double-click the file to launch it.

- Follow instructions to install the software.
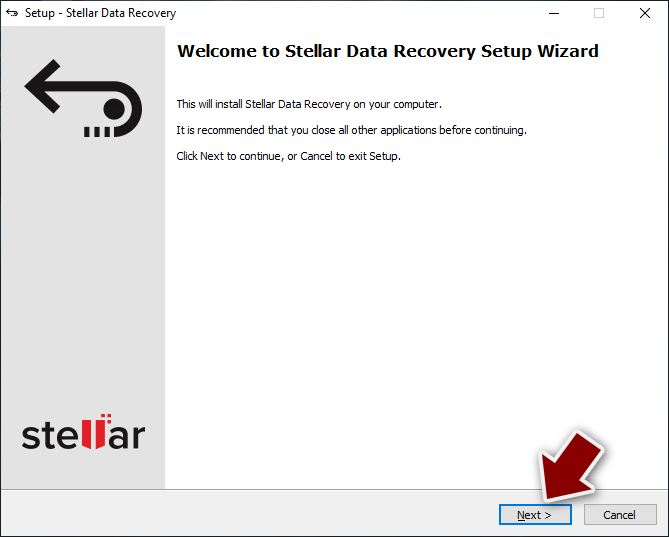
- Press Finish and use the app.
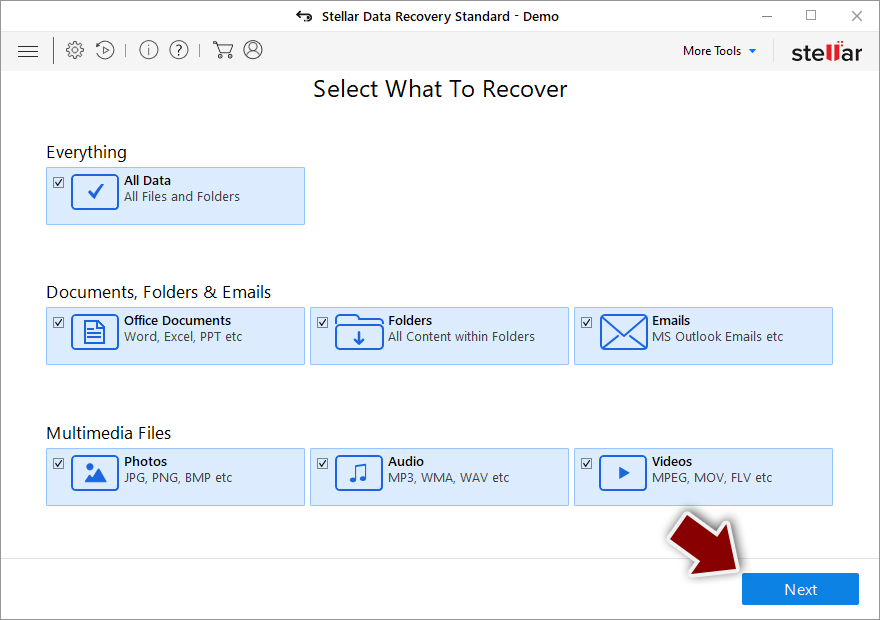
- Select Everything or pick individual folders where you want the files to be recovered from.
- Press Next.
- Enable Deep scan and pick which Disks you want to be scanned.
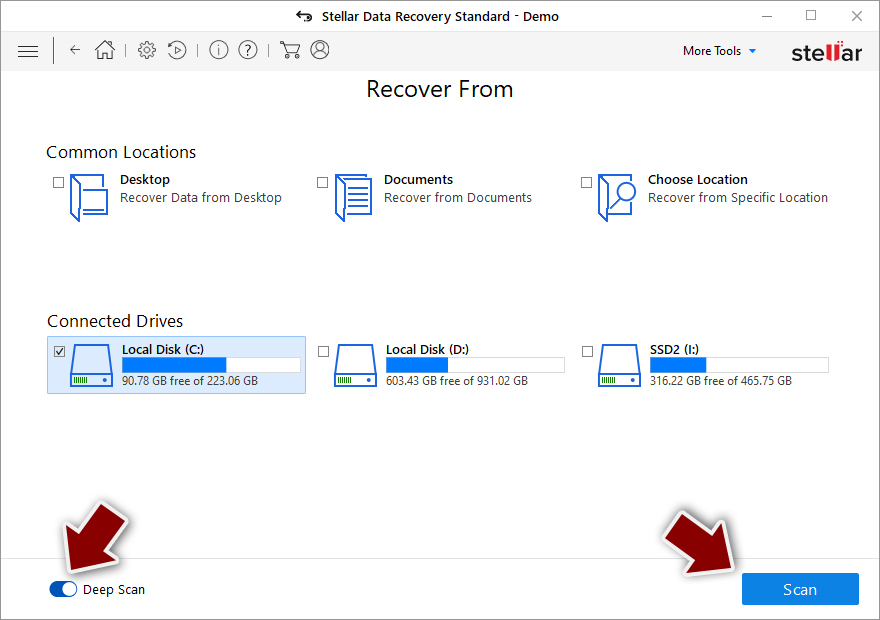
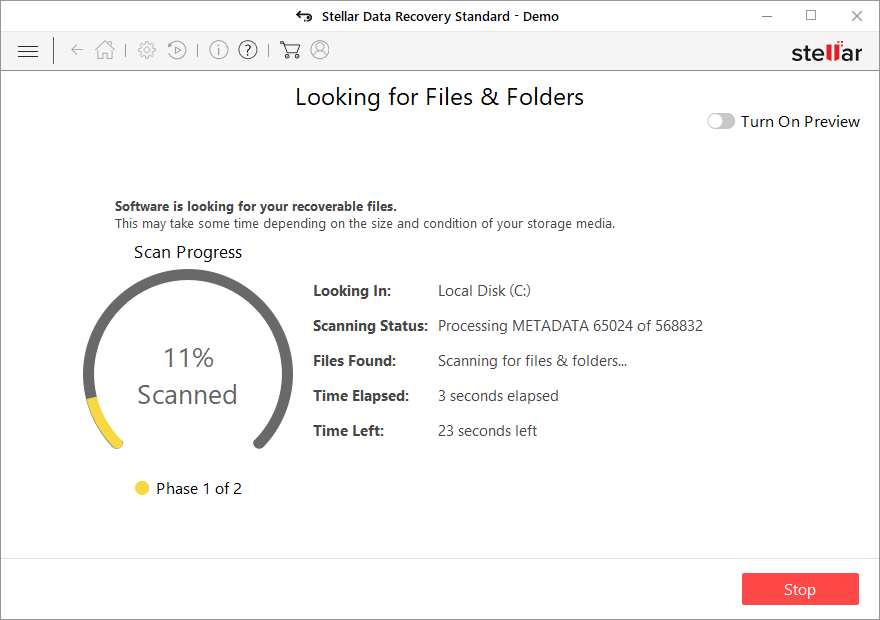
- Press Scan and wait till it is complete.
- You can choose folders/files to recover – don't forget you also have the option to search by the file name!
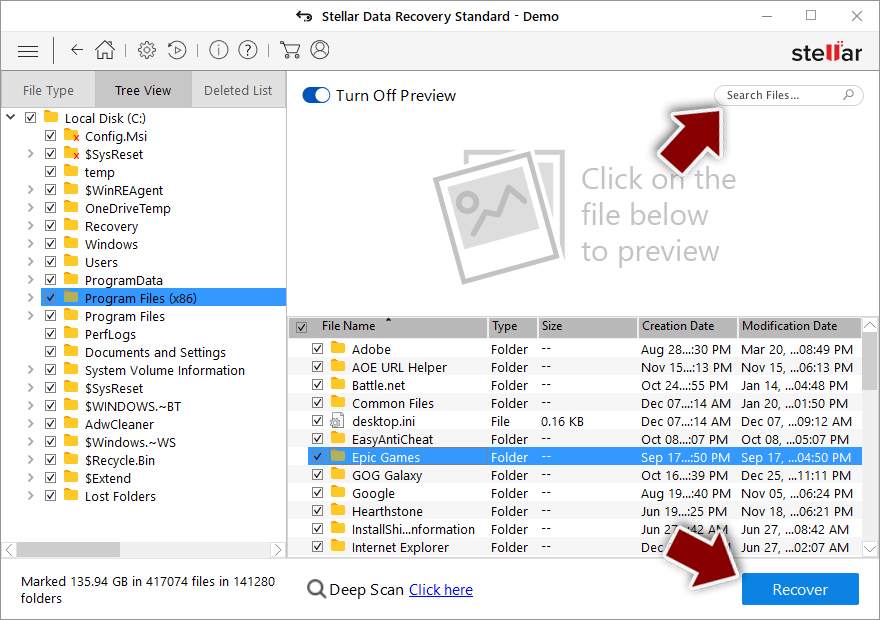
- Press Recover to retrieve your files.
In-depth guide for the Zfdv elimination
Important! →
The elimination guide can appear too difficult if you are not tech-savvy. It requires some knowledge of computer processes since it includes system changes that need to be performed correctly. You need to take steps carefully and follow the guide avoiding any issues created due to improper setting changes. Automatic methods might suit you better if you find the guide too difficult.
Step 1. Launch Safe Mode with Networking
Safe Mode environment offers better results of manual virus removal
Windows 7 / Vista / XP
- Go to Start.
- Choose Shutdown, then Restart, and OK.
- When your computer boots, start pressing the F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) a few times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click the Start button and choose Settings.

- Scroll down to find Update & Security.

- On the left, pick Recovery.
- Scroll to find Advanced Startup section.
- Click Restart now.

- Choose Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.

- Choose 5) Enable Safe Mode with Networking.
Step 2. End questionable processes
You can rely on Windows Task Manager that finds all the random processes in the background. When the intruder is triggering any processes, you can shut them down:
- Press Ctrl + Shift + Esc keys to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes.
- Look for anything suspicious.
- Right-click and select Open file location.

- Go back to the Process tab, right-click and pick End Task.
- Delete the contents of the malicious folder.
Step 3. Check the program in Startup
- Press Ctrl + Shift + Esc on your keyboard again.
- Go to the Startup tab.
- Right-click on the suspicious app and pick Disable.

Step 4. Find and eliminate virus files
Data related to the infection can be hidden in various places. Follow the steps and you can find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive (C: is your main drive by default and is likely to be the one that has malicious files in) you want to clean.
- Scroll through the Files to delete and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
It is strongly recommended to take precautions and secure your computer from malware attacks. To protect your PC from Zfdv and other dangerous viruses, you should install and keep a powerful malware removal tool, for instance, FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes.
How to prevent from getting ransomware
A proper web browser and VPN tool can guarantee better safety
As online spying becomes an increasing problem, people are becoming more interested in how to protect their privacy. One way to increase your online security is to choose the most secure and private web browser. But if you want complete anonymity and security when surfing the web, you need Private Internet Access VPN service. This tool successfully reroutes traffic across different servers, so your IP address and location remain protected. It is also important that this tool is based on a strict no-log policy, so no data is collected and cannot be leaked or made available to first or third parties. If you want to feel safe on the internet, a combination of a secure web browser and a Private Internet Access VPN will help you.
Reduce the threat of viruses by backing up your data
Due to their own careless behavior, computer users can suffer various losses caused by cyber infections. Viruses can affect the functionality of the software or directly corrupt data on your system by encrypting it. These problems can disrupt the system and cause you to lose personal data permanently. There is no such threat if you have the latest backups, as you can easily recover lost data and get back to work.
It is recommended to update the backups in parallel each time the system is modified. This way, you will be able to access the latest saved data after an unexpected virus attack or system failure. By having the latest copies of important documents and projects, you will avoid serious inconveniences. File backups are especially useful if malware attacks your system unexpectedly. We recommend using the Data Recovery Pro program to restore the system.
