How to remove AOL virus
AOL cyber infections are designed to infect users via AOL Instant Messenger (alternatively known as AIM and America OnLine software). Unfortunately, usual AOL virus operates similarly to trojans or computer worms. After invading the operating system, it looks for important data, such as login passwords, credit card numbers, verification codes, and other important details. The ability to record the keystrokes on the infected computers greatly empowers these threats. Taking screenshots is also included in the activities. In short, AOL viruses operate as convenient tools for accessing the targeted device remotely.
Speaking of the distribution preferences, the virtual threats prefer using the trusted channel for the infection techniques – spam and phishing. Additionally, corrupted links facilitate the hijack process. Needless to say that such links may frequently be found in AIM Messenger’s messages. Previously, Windows OS users were the main target for AOL viruses, but now Mac OS owners may not escape this ominous malware. Even though that the very application may have lost its appeal to users, there are fair chances to get assaulted by these viruses. Therefore, such probability encourages the members of virtual reality to reconsider using the application. Otherwise, a proper security tool is a necessity if you decoide to keep it.
Modus operandi of AOL viruses
Comparing the scale of damage inflicted by this type of virtual infections, AOL viruses stand in the top of the virus hierarchy alongside to banking trojans. Besides aiming for the banking data, the malware also causes privacy infringement issues. In relation to this, the obtained data might be employed for hackers’ evil intentions. In other words, it grants the ability to access or terminate certain accounts or hack them. Technical issues and malfunctioning crucial system applications and deteriorated browser performance happen to be the aftermath of the hijack as well. AOL viruses may also operate as the carriers for more damaging viruses. Here are the main activities:
- Private data theft. The virus targets such pieces of information as UINs (Universal Internet Number, employed in ICQ network). After the data is acquired, it is automatically transmitted to remote servers via a concealed Internet connection.
- Spamming. This trojan-hybrid malware also tends to trigger the emergence of countless frustrating pop-ups. Furthermore, DDoS (distributed denial of services) occurrences might become an indicator of the infection.
- Recording personal messages. Since the virus may spread via the AOL application, the malware tracks all your messaging and call history. Due to this, the malware gets more chances to employ it for its malicious purposes.
- Infecting victim’s contacts. Once the virus manages to access your personal chat messages, it activates its capabilities of a computer worm and transmits the infected links to the members of your contact groups.
- Gathering technical information. AOL and ICQ-related information, IP address, geographical location, as well as the technical details about the operating system fall into the category of the compiled data. With it in possession, racketeers may improve their hacking techniques.
- Interfering with the operation of other system applications. It is not surprising that some essential computer functions and applications might cease working after one of AOL viruses infect the system.
- Concealing its presence. To make matter worse, the malware is able to hide its processes in Task Manager. Such diversion helps it to operate in the system longer before getting detected.
How does the virus infect devices?
The AOL hijack is likely to happen if these conditions are present:
AOL program vulnerabilities. This method is most prevalent as infecting the application does not require displaying dialogue boxes, setup guides, and notifications to receive users’ permission. Therefore, failing to update AOL messenger for a longer while may highly boost up the chances of a hijack. Later on, identifying the original and corrupted program becomes a difficult challenge. Therefore, do not forget to look for the updates daily.
Corrupted links in AIM. If this cyber misfortune befell one of your friends or someone from the contact list, be aware that you may receive an infected link. They might be disguised as highly important and urgent messages. Consequently, careless click on the link might result in the infection of AOL virus.
Diverse malware. AOL viruses tend to cooperate with other cyber infections. Besides them being trojan horses or computer worms, they may be supported by backdoors, rootkits, exploit kits and other spyware threats to increase the number of hijacks.
Short review of well-known AOL viruses
Due to the immeasurable capacities of the Internet, enumerating the exact number and kinds of AOL viruses is futile. However, you can take not of these dominant virtual threats:
Omerstroke malware spies and records user’s activities in AIM messenger. Once the infection process is complete, it starts searching for potentially valuable pieces of information, such as login data to accounts. Later on, the acquired data is transmitted to a remote server. Fake system error messages signal the presence of Omerstroke virus.
ICQ Zap. An excessive amount of spam messages indicates ICQ Zap hijack. Later on, the enormous numer of spam notifications cram the application and significantly deteriorate its overall performance.
UIN IP malware prefers occupying operating systems via a trojan. Additionally, some users report that they have been targeted with forged warning notifications, In this case, you may be asked to click on the link which accelerates the infection process. The malware also tends to operate as a proxy server which enables it to record personal text messages and video conversations. As a result, such virus facilitates personal data theft.
AOL malware termination recommendations
Even if AOL threats possess some distinctive peculiarities, the majority of them still operate as common infections. Therefore, prevalent removal methods are applicable to them. When it comes to any severe virtual infection, we recommend employing reputable and acclaimed security applications for full and efficient removal. Specifically, anti-spyware applications are practical termination tools. Our Software section delivers a wide choice of reviews of most effective security programs, with FortectIntego and Malwarebytes being prominent of them.
Note that even the most powerful anti-spyware applications may fail to commit their mission if they are not updated regularly. Time is a significant factor as cyber villains restlessly launch more austere threats each hour. Therefore, it is crucial to keep up with the latest viruses in order to increase the cyber safety.
Latest AOL viruses added to the database
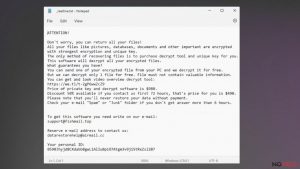
Steps for removing Bozq ransomware
Uninstalling Powz ransomware
Mmpu ransomware removal tutorial
Additional information added on 2016-11-25