Remove YAC (Uninstall Guide) - Sep 2017 updated
YAC Removal Guide
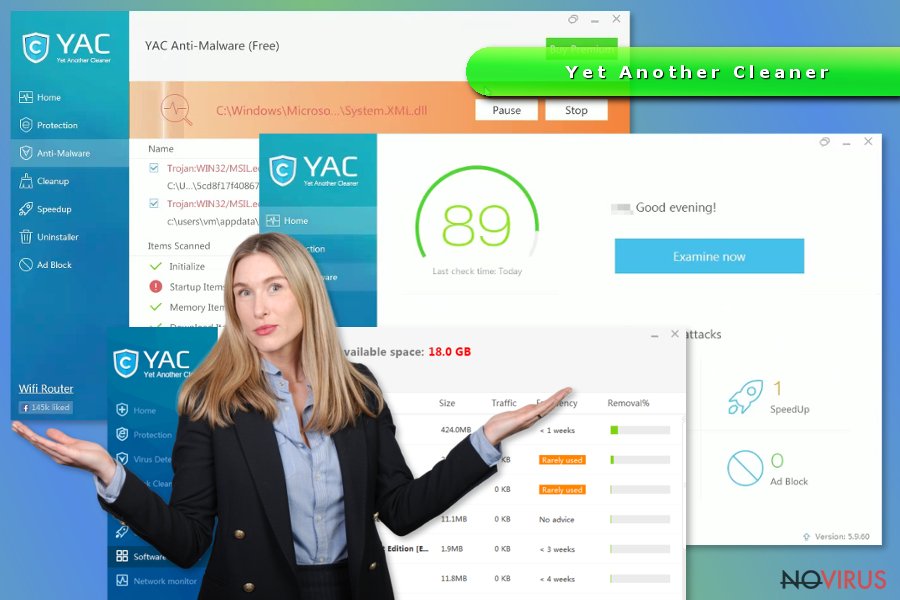
Description of YAC virus
YAC should not be used for your computer’s protection

YAC (Yet Another Cleaner) is a questionable security software and PC optimization tool. In the Terms of Use, developers, Elex do Brasil Participações Ltda Technology Inc, claim that this program is affiliated with popular security companies, such as Enigma Software and Malwarebytes:
Affiliation with anti-spyware and anti-malware companies: Malwarebytes (Malwarebytes Antimalware), PC Tools (STOPzilla), Enigma Software (SpyHunter 4), SUPERantispyware (Superantispyware), SurfRight B.V. (Hitman Pro).
However, these security vendors barely have something in common with YAC. What is worse, Malwarebytes reported that their software’s interface and detection database might have been borrowed by Yet Another Cleaner. Therefore, this fact should prove that this security program is not reliable.
Furthermore, due to the shady distribution method, the software was named as a YAC virus. But technically speaking, it is not a computer virus. Security experts agree that it’s a potentially unwanted program (PUP) that might:
- get installed in the computer with the help of free programs;
- download other PUPs, including MyPC backup, search.yac.mx or isafe yac;
- cause various browsing-related problems.
However, the biggest problem here is that YAC may not perform its primary feature properly. Thus, if you want to protect your computer from malware, trojans and other cyber threats, you should uninstall this suspicious tool and obtain a reputable software.
Though, it may not be easy to uninstall YAC. The problems might occur if it arrived in the software package. Many users reported that they were unable to find it in the Control Panel or remove it manually. The source of such problem is unknown. However, it can be fixed with powerful antivirus.
Therefore, if you have to remove YAC from the device, you can try to uninstall it manually first. We have provided detailed instructions in the third part of the article. However, if these attempts fail, you have to invest in professional malware removal program.
For YAC removal and further computer’s protection, we recommend choosing FortectIntego. We can assure that this security software will clean all malicious components from your computer and protects your device from similar cyber threats in the future.
Downloads from the official website is not the only way how this security tool might get into computer
Users can download Yet Another Cleaner from the official websites, as well as various third-party file-sharing websites. However, direct downloads are not the only distribution channel. Developers also widely use bundling strategy.
Bundling technique allows attaching the program as an optional download in software packages. Therefore, you can find this suspicious security software offered to install together with media players, PDF converters or other free programs.
However, in order to see and reject installation of these third-party apps, you have to choose the right installation settings – ‘Advanced’ or ‘Custom.’ Keep in mind that ‘Quick’ or ‘Standard’ setups do not have this feature. Thus, you should never use it.
Though, once you opt for ‘Advanced’ installation, you have to read EULA, Privacy Policy and make sure that you did not leave any pre-selected apps or agreements to change your search engine.
Uninstall YAC from the computer following these instructions
If you have installed this program unintentionally, it’s time to get rid of it. You can remove YAC from Windows computer following these steps:
Windows 8 / 8.1 / 10
- Access Control Panel and choose Uninstall a Program option.
- In the list of the programs find Yet Another Cleaner, PC Backup, YAC Search, iSafe or other suspicious programs.
- Choose ‘Uninstall’ option.
- Click OK to save the changes.
Windows 7 / Vista / XP
- Go to Control Panel from Start menu.
- Access Programs and Features (Windows XP users should go to Add/Remove Programs).
- Once the list of installed programs appears, look for Yet Another Cleaner, PC Backup, YAC Search, iSafe or other suspicious programs.
- Click ‘Uninstall’ button and hit OK to save the changes.
However, you can also perform automatic YAC removal with security software. You have to install FortectIntego, Malwarebytes or your preferred malware removal program and run a full system scan with an updated tool.
How to prevent from getting system tools
Securely connect to your website wherever you are
Sometimes you may need to log in to a content management system or server more often, especially if you are actively working on a blog, website, or different project that needs constant maintenance or that requires frequent content updates or other changes. Avoiding this problem can be easy if you choose a dedicated/fixed IP address. It's a static IP address that only belongs to a specific device and does not change when you are in different locations.
VPN service providers such as Private Internet Access can help you with these settings. This tool can help you control your online reputation and successfully manage your projects wherever you are. It is important to prevent different IP addresses from connecting to your website. With a dedicated/fixed IP address, VPN service, and secure access to a content management system, your project will remain secure.
Recover files damaged by a dangerous malware attack
Despite the fact that there are various circumstances that can cause data to be lost on a system, including accidental deletion, the most common reason people lose photos, documents, videos, and other important data is the infection of malware.
Some malicious programs can delete files and prevent the software from running smoothly. However, there is a greater threat from the dangerous viruses that can encrypt documents, system files, and images. Ransomware-type viruses focus on encrypting data and restricting users’ access to files, so you can permanently lose personal data when you download such a virus to your computer.
The ability to unlock encrypted files is very limited, but some programs have a data recovery feature. In some cases, the Data Recovery Pro program can help recover at least some of the data that has been locked by a virus or other cyber infection.
