Remove Nbryb.com (Uninstall Instructions) - Chrome, Firefox, IE, Edge
Nbryb.com Removal Guide
Description of Nbryb.com
Nbryb.com is the app that uses social-engineering tricks to deceive users into allowing push notifications that lead to tons of ads
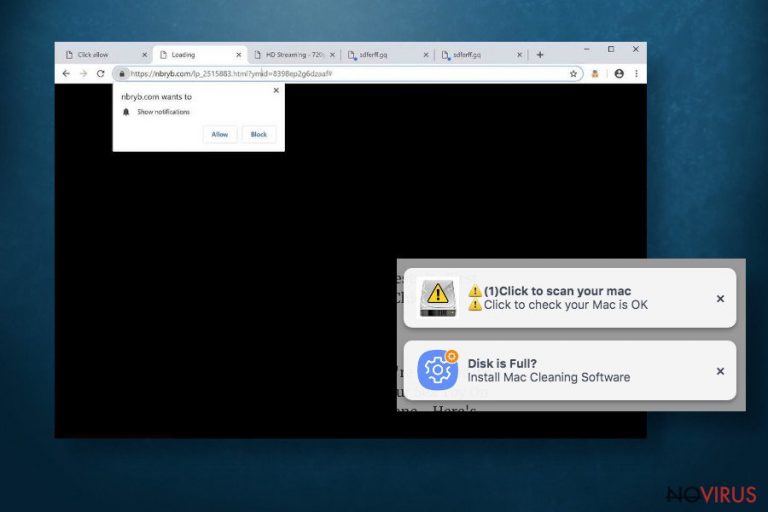
Nbryb.com virus is a deceptive website that tricks people into accepting its browser notifications by stating that the visitor must push the Allow button to watch a video. Once this button is pressed, users will start to see pop-up ads even when their browsers aren't being used.
Although Nbryb.com push notification website isn't dangerous itself, deceptive ads might lead to various malicious pages, commercial websites, promotional domains. When redirected to such sites, the visitor might be tricked into downloading some potentially unwanted programs (PUPs).
These PUPs might lead to more severe malware, like trojan horses or ransomware like NORD, Weui, WannaScream, and others. So everyone is better of not allowing the push notifications from Nbryb.com. It is worth to mention that this virus affects Windows, Mac, Android systems.
| name | Nbryb.com |
|---|---|
| type | Adware, push notification virus |
| affected browsers | Safari, Google Chrome, Mozilla Firefox, Microsoft Edge, etc. on Windows, Macs, and Androids |
| Symptoms | Annoying ads appearing within the browser window, sometimes even on the desktop while the browsers are closed. Constant redirections to other websites like nbryb.com, sdfjjd.nbryb.com, and breakingfeedz.com. |
| risks | Adware is not dangerous itself, but the ads that it's displaying might redirect users to malicious sites where some sort of malware could be downloaded, leading to a loss of personal, financial, or other information |
| Removal | If you've started to notice redirects, that might mean that adware is installed on your device. Remove it with proper anti-malware software to ensure all its pieces are eliminated |
| System fix | Whether adware or not, a system tune-up is in order after Nbryb.com removal. Use the FortectIntego tool to fix any registry issues that the virus could have caused. |
In general, the Nbryb.com site and its push notifications aren't a bad thing. They inform their subscribers of the latest news, time-sensitive discounts, and so on. But these notifications can also be used by cybercriminals. If redirected to their promoted sites, users might end up with all kinds of malware.
If you experience redirections to pages like Nbryb.com, sdfjjd.nbryb.com, and breakingfeedz.com when you're browsing, that might mean that your browser was hijacked. PUPs like browser hijackers often change the home page and new tab preferences, the default search engine, etc.
So think hard before pushing the Allow button on the top-left corner when visiting the Nbryb.com website and allowing it to show you the ill-advised content with their intrusive ads because that could just lead to additional installment of PUPs or even severe malware.

So for your own safety, we recommend you remove Nbryb.com from your computer or smartphone with our easy removal guide. First of for any Android cell phones:
- Access the Play Store and go to My Apps
- Inspect the Installed and Last used section
- Now go to Settings and open Apps
- Remove any suspicious-looking apps that are installed lately, especially ones without icons.
Other Nbryb.com removal guides are at the bottom of this article. If the redirects don't stop after changing the browser settings back to normal, then experts advise reinstalling the browser altogether and performing a full system scan with proper anti-malware software to determine if any PUP or malware got on your system. Afterward, perform a system tune-up with the FortectIntego tool, and you're good to go.
Most common ways of browser hijacker delivery – freeware bundles
Potentially unwanted programs (PUPs) that change browser settings, such as new tab preference, the home page, default search engine, and show intrusive ads, are called browser hijackers. They generate revenue from promoting affiliated websites or their products/services.
The most common way that these PUPs end up on everyday computer user devices is software bundles. Since in this day and age, everybody's in a rush, so when installing some software, we don't have the time to read Terms & Conditions or to select the Advanced/Custom Installation instead of the Quick/Standart one. And that's how browser hijackers, adware, and other PUPs get in your devices.
For your own and the safety of your device, don't rush when you're deciding what program to install on your device. Software bundles might contain numerous software that you don't want. After picking the Advanced or Custom Installation option, look through what would be installed on your computer if you'd have chosen otherwise.
Deselect all pre-ticked boxes of software that you didn't know will be installed on your device and you don't want it. Get only the app that you required in the first place.
Nbryb.com removal guides for different browsers and devices
Nbryb.com virus could be very annoying with continuous pushing of pop-up ads and constant redirections to a new tab with one of nbryb.com, sdfjjd.nbryb.com, breakingfeedz.com, or other affiliated websites popping up. If you're tired of it – let's remove it.
If you want to remove Nbryb.com from your Windows Computer or Mac, then as we mentioned in the first paragraph, you should use a professional and trustworthy anti-malware application that would locate every little particle of this PUP and abolish it.
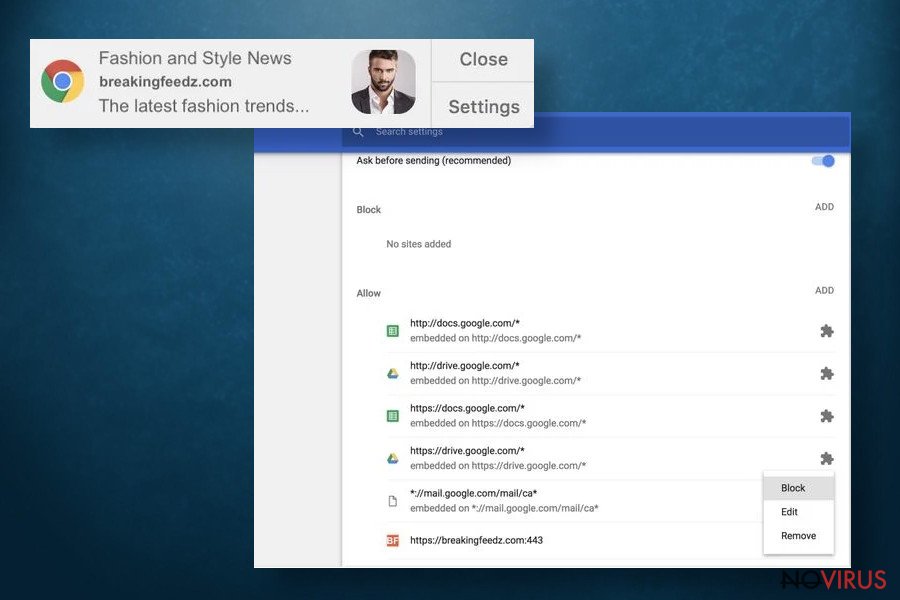
Here's how you unsubscribe Nbryb.com notifications when they're messing up your browsing experience when you're using Google Chrome browser:
- Press on the Settings button when a pop-up window shows up
- Choose block or remove option in the settings of related domains
- Afterward, press on the lock icon next to the website's URL address
- Under permissions, open the drop-down menu and choose always block on this site.
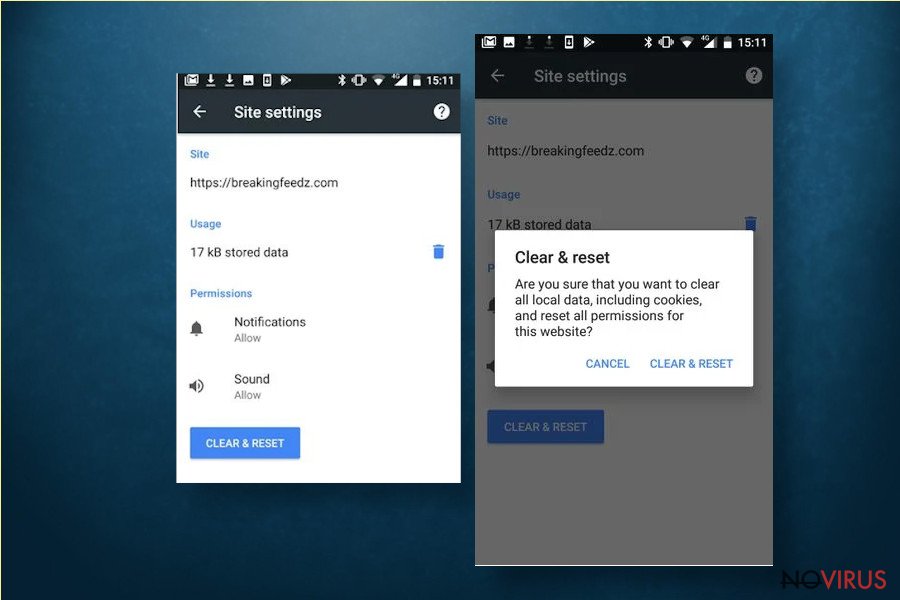
Nbryb.com notifications removal if you're using Android:
- As soon as a pop-up shows up, tap on the Site Settings button.
- Press on the Clear & Reset button.
- Press the Clear & Reset option once more
- Afterward, open the browser and press on the lock icon next to the URL address.
- Locate permission status under Notifications, and open the drop-down menu
- Press the Clear & Reset button once more to confirm the changes.
You may remove virus damage with a help of FortectIntego. SpyHunter 5Combo Cleaner and Malwarebytes are recommended to detect potentially unwanted programs and viruses with all their files and registry entries that are related to them.
Getting rid of Nbryb.com. Follow these steps
Uninstall Nbryb.com in Windows systems
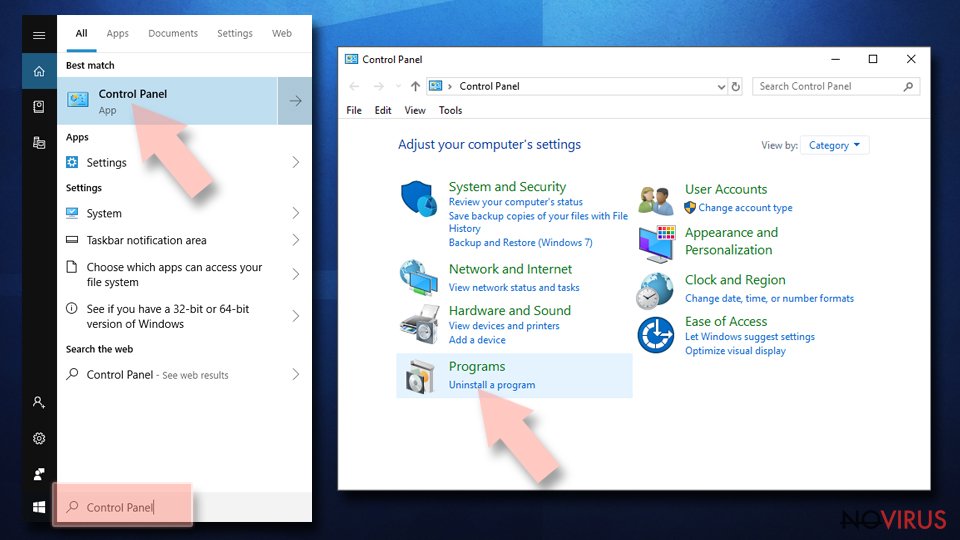
Terminate suspicious programs from Windows 10/8 machines by following these instructions:
- Type Control Panel into Windows search and once the result shows up hit Enter.
- Under Programs, choose Uninstall a program.
- Find components related to suspicious programs.
- Right-click on the application and select Uninstall.
- Click Yes when User Account Control shows up.
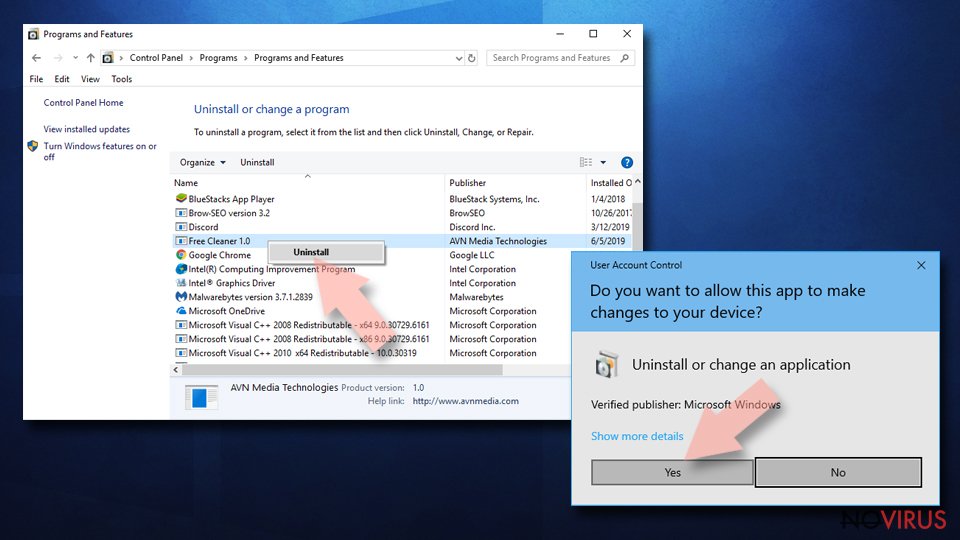
- Wait for the process of uninstallation to be done and click OK.
Windows 7/XP instructions:
- Click on Windows Start and go to Control Panel on the right pane.
- Choose Add/Remove Programs.
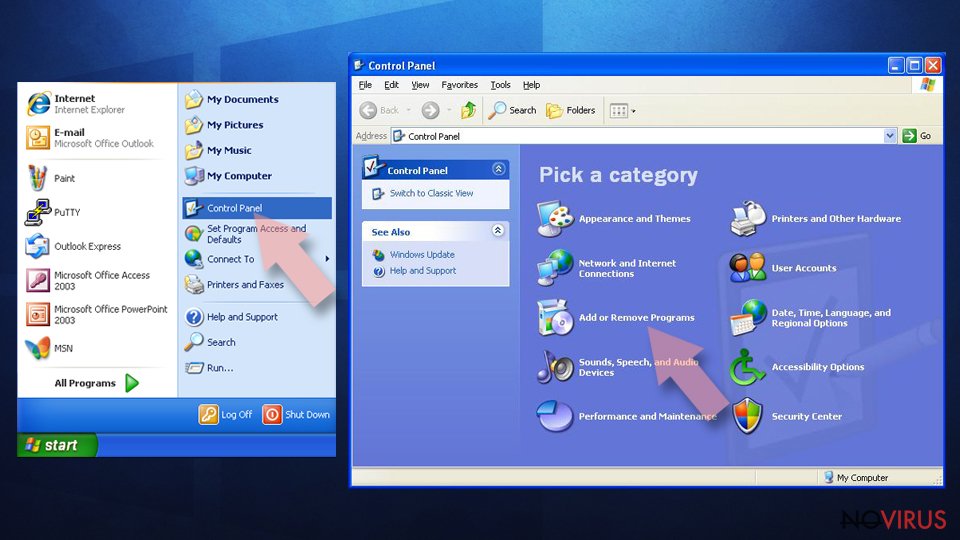
- Select Uninstall a program under Programs in Control Panel.
- Click once on the unwanted application.
- Click Uninstall/Change at the top.
- Confirm with Yes.
- Click OK and finish the removal.
Uninstall Nbryb.com in Mac OS X system
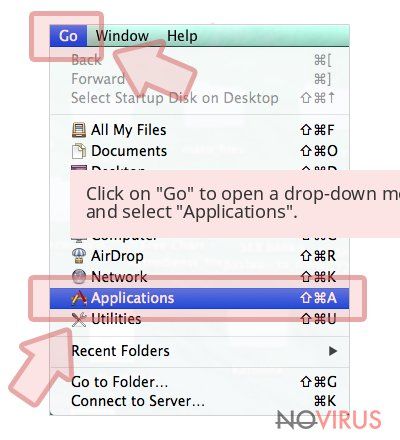
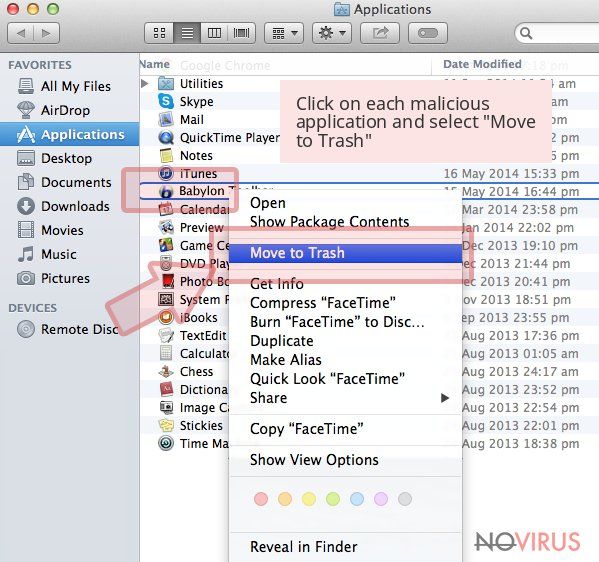
-
Users who use OS X should click on Go button, which can be found at the top left corner of the screen and select Applications.

-
Wait until you see Applications folder and look for Nbryb.com or any other suspicious programs on it. Now right click on every of such entries and select Move to Trash.

Delete Nbryb.com from Microsoft Edge
Delete suspicious extensions from MS Edge:
- Go to the Menu by clicking on the three horizontal dots at the top-right.
- Then pick Extensions.
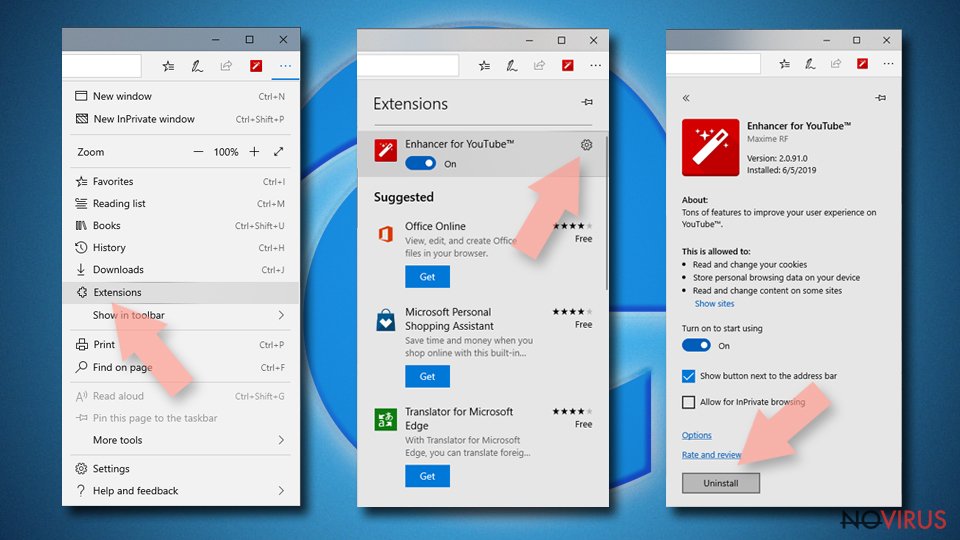
- Choose the unwanted add-ons on the list and click on the Gear icon.
- Click on Uninstall at the bottom.
Clear cookies and other data:
- Click on the Menu and from the context menu select Privacy & security.
- Under Clear browsing data, select Choose what to clear.
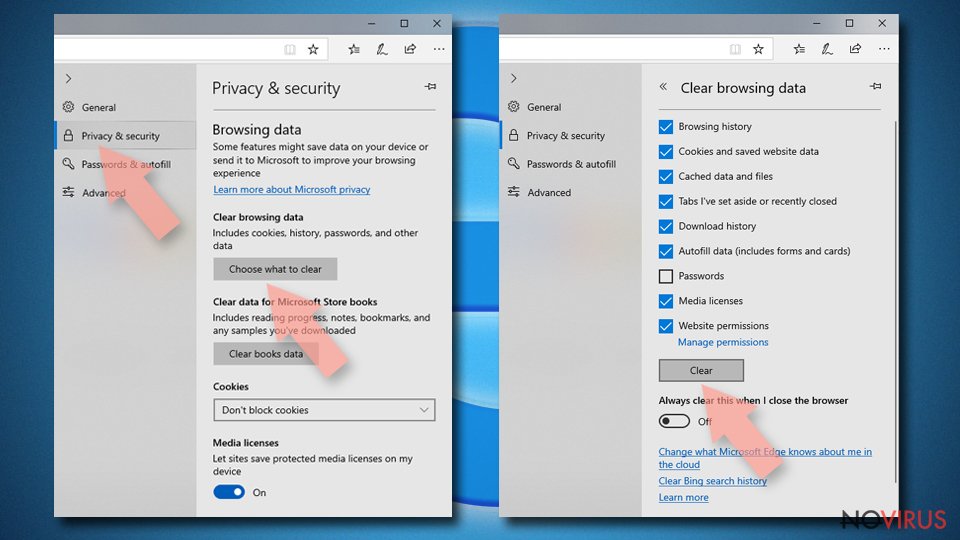
- Choose everything except passwords, and click on Clear.
Alter new tab and homepage settings:
- Click the menu icon and choose Settings.
- Then find On startup section.
- Click Disable if you found any suspicious domain.
Reset MS Edge fully:
- Click on the keyboard Ctrl + Shift + Esc to open Task Manager.
- Choose More details arrow at the bottom.
- Go to Details tab.
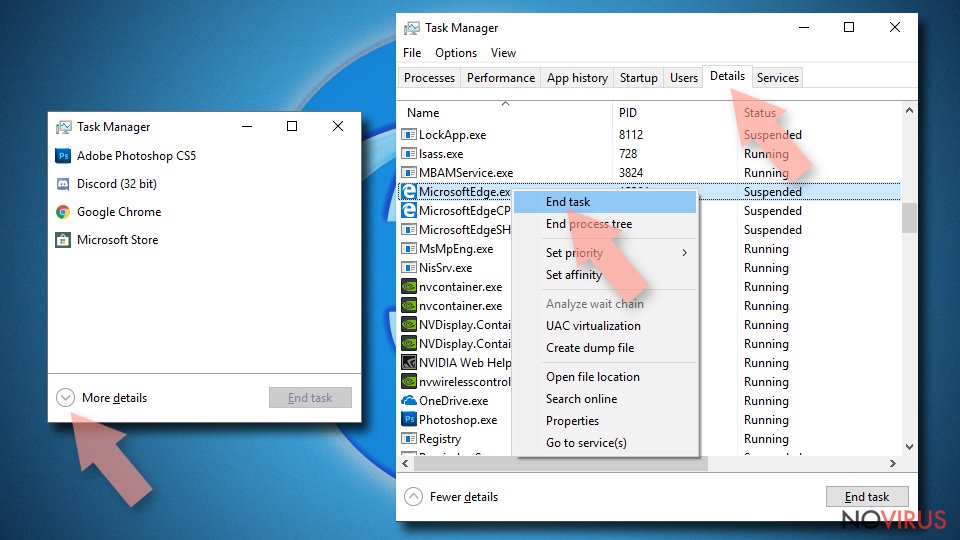
- Now scroll down and locate every entry with Microsoft Edge name in it.
- Right-click on each of them and select End Task to stop MS Edge from running.
When none of the above solves the issue, you might need an advanced Edge reset method, but you need to backup your data before proceeding.
- Find the following folder on the PC: C:\\Users\\%username%\\AppData\\Local\\Packages\\Microsoft.MicrosoftEdge_8wekyb3d8bbwe.
- Press Ctrl + A on your keyboard to select all folders.
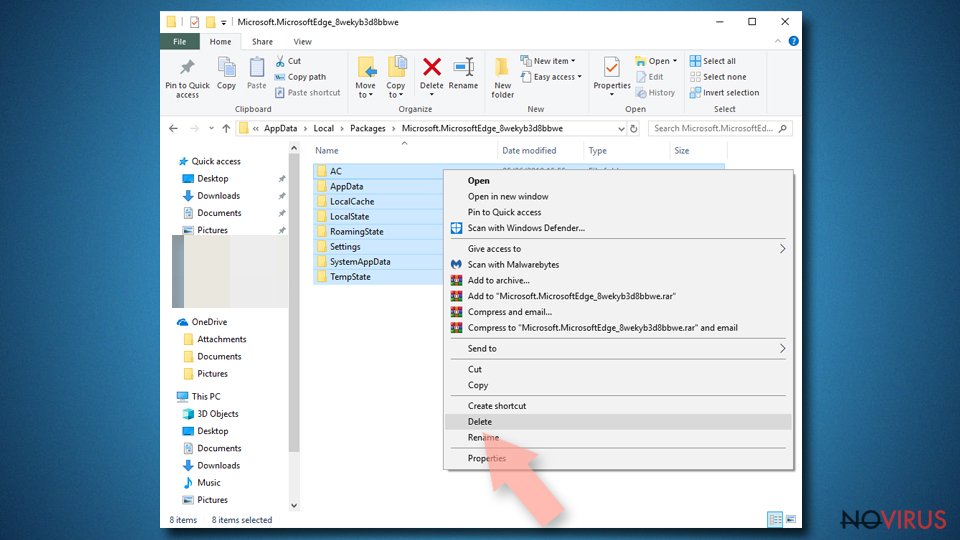
- Right-click on the selection and choose Delete
- Right-click on the Start button and pick Windows PowerShell (Admin).
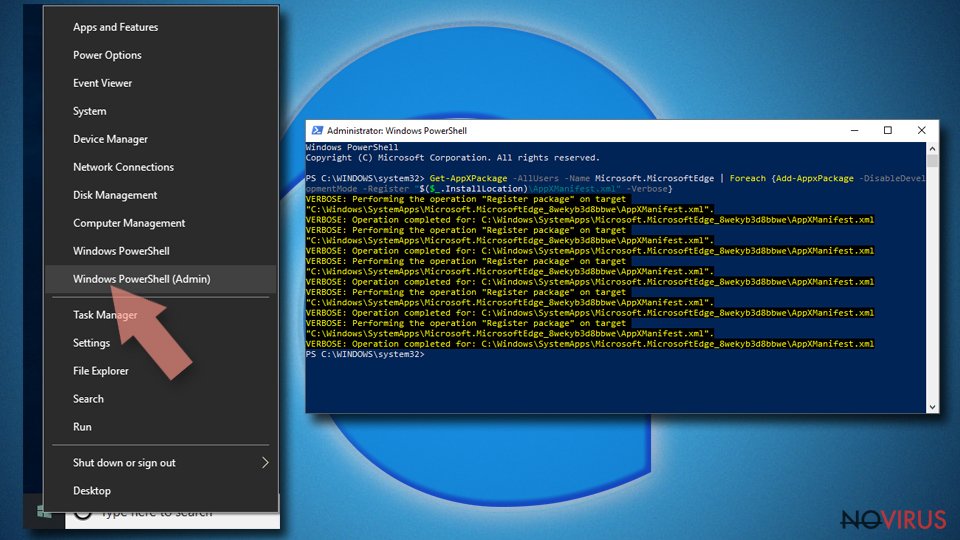
- Copy and paste the following command, and then press Enter:
Get-AppXPackage -AllUsers -Name Microsoft.MicrosoftEdge | Foreach {Add-AppxPackage -DisableDevelopmentMode -Register “$($_.InstallLocation)\\AppXManifest.xml” -Verbose
Instructions for Chromium-based Edge
Delete extensions:
- Open Edge and click Settings.
- Then find Extensions.
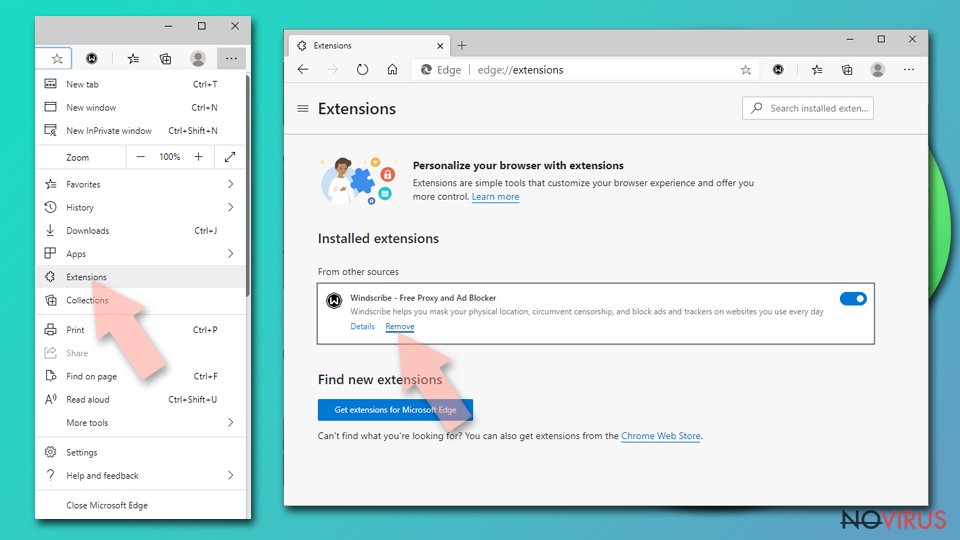
- Delete unwanted extensions with the Remove.
Clear cache and site data:
- Click on Menu and then Settings.
- Find Privacy and services.
- Locate Clear browsing data, then click Choose what to clear.
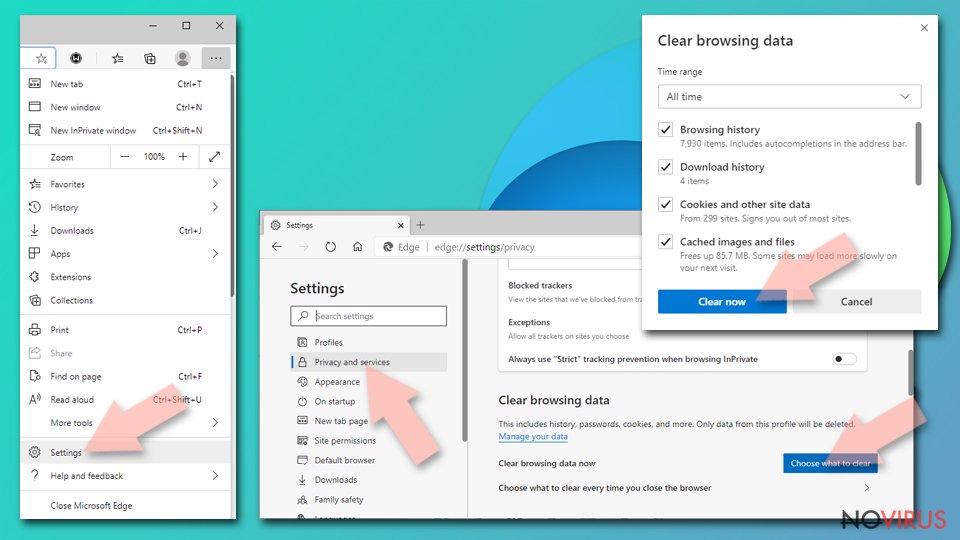
- Time range.
- Click All time.
- Select Clear now.
Reset Chromium-based MS Edge browser fully:
- Go to Settings.
- On the left side, choose Reset settings.
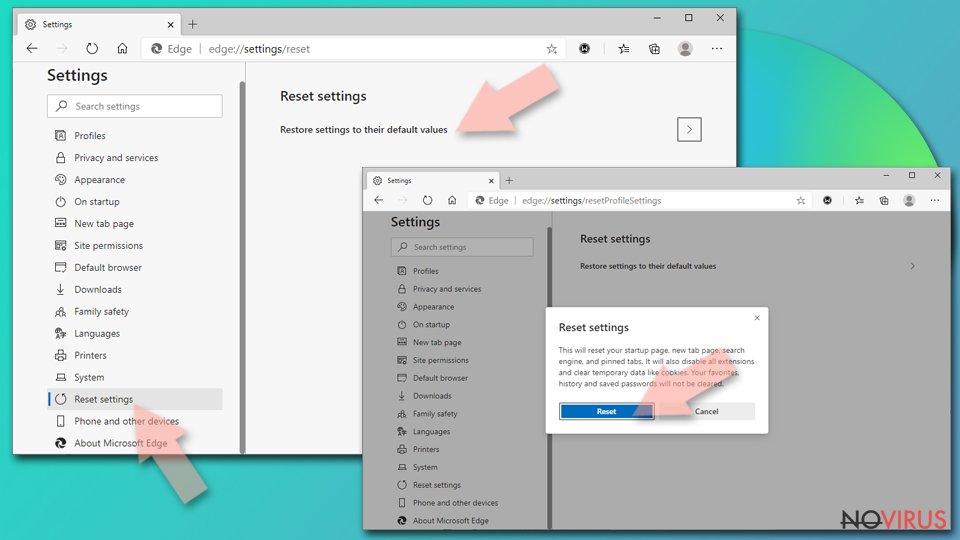
- Select Restore settings to their default values.
- Click Reset.
Delete Nbryb.com from Mozilla Firefox (FF)
Remove suspicious Firefox extensions:
- Open Mozilla Firefox browser and click on the three horizontal lines at the top-right to open the menu.
- Select Add-ons in the context menu.
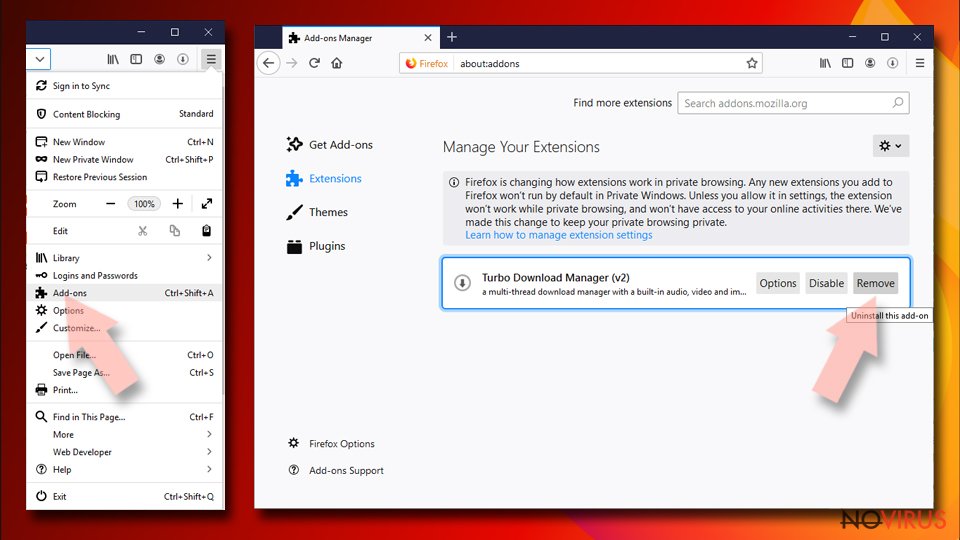
- Choose plugins that are creating issues and select Remove.
Reset the homepage on the browser:
- Click three horizontal lines at the top right corner.
- This time select Options.
- Under Home section, enter your preferred site for the homepage that will open every time you launch Mozilla Firefox.
Clear cookies and site data:
- Click Menu and pick Options.
- Find the Privacy & Security section.
- Scroll down to choose Cookies and Site Data.
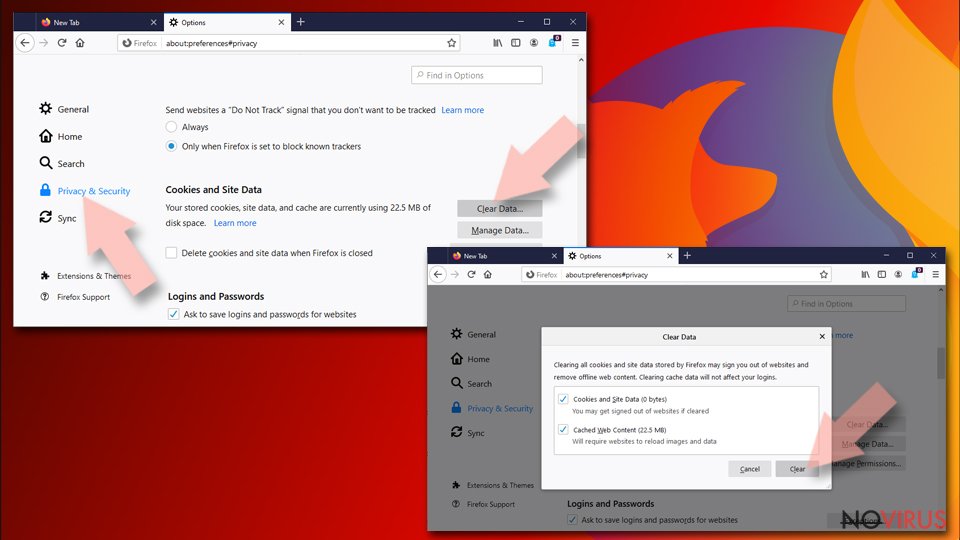
- Click on Clear Data… option.
- Click Cookies and Site Data, Cached Web Content and press Clear.
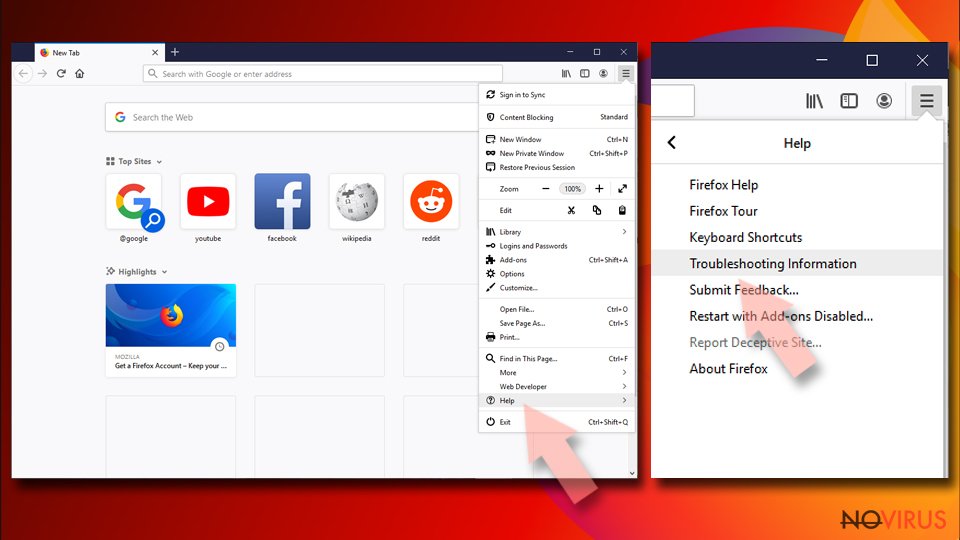
Reset Mozilla Firefox:
If none of the steps above helped you, reset Mozilla Firefox as follows:
- Open Mozilla Firefox and go to the menu.
- Click Help and then choose Troubleshooting Information.
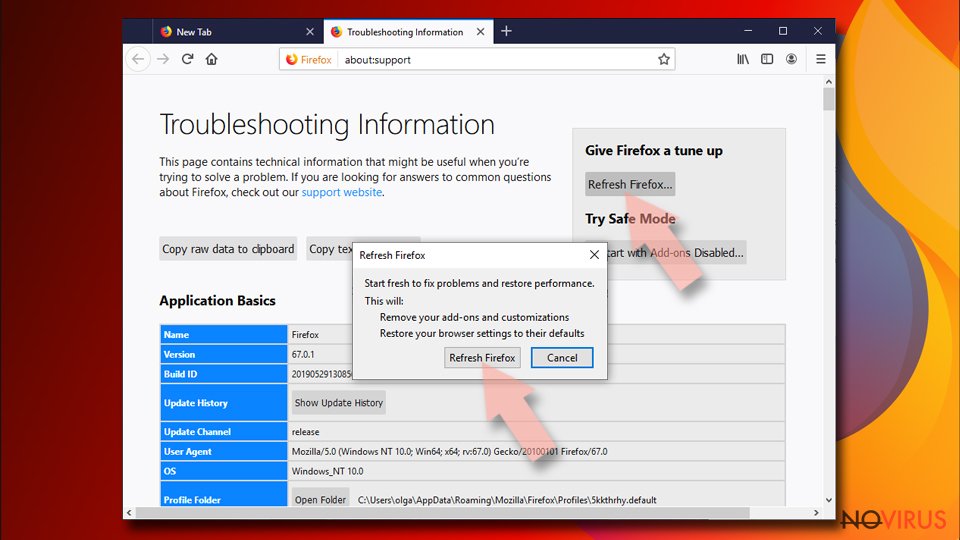
- Locate Give Firefox a tune-up section, click on Refresh Firefox…
- Confirm the action by pressing on Refresh Firefox on the pop-up.
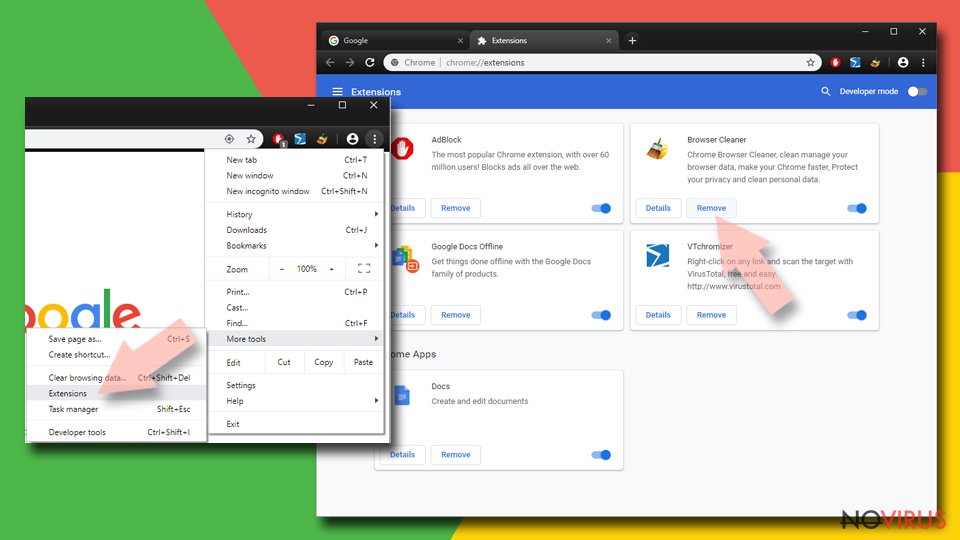
Chrome browser reset
Find and remove suspicious extensions from Google Chrome:
- In Google Chrome, open the Menu by clicking three vertical dots at the top-right corner.
- Select More tools > Extensions.
- Once the window opens, you will see all the installed extensions.
- Find any suspicious add-ons related to any PUP.
- Uninstall them by clicking Remove.
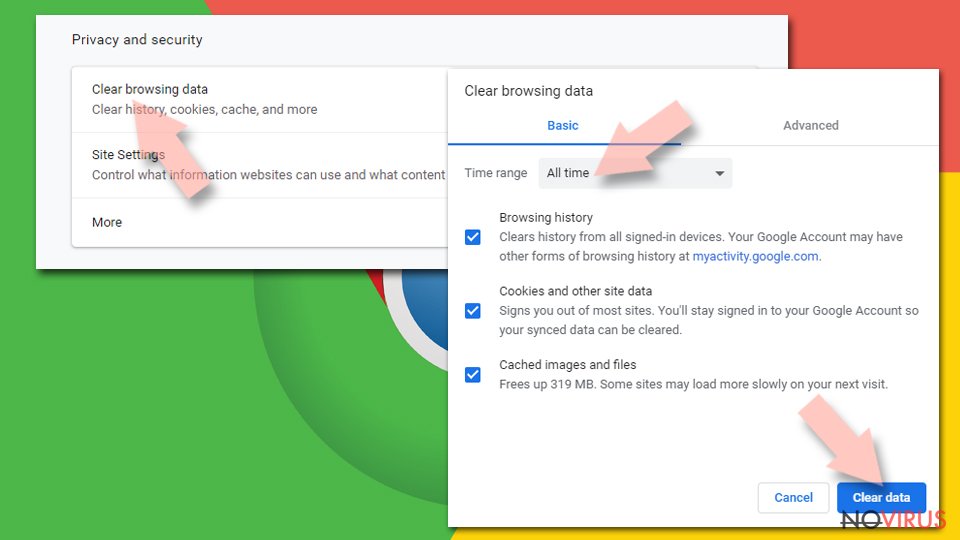
Clear cache and web data from Chrome:
- Click the Menu and select Settings.
- Find Privacy and security section.
- Choose Clear browsing data.
- Select Browsing history.
- Cookies and other site data, also Cached images and files.
- Click Clear data.
Alter settings of the homepage:
- Go to the menu and choose Settings.
- Find odd entries in the On startup section.
- Click on Open a specific or set of pages.
- Then click on three dots and look for the Remove option.
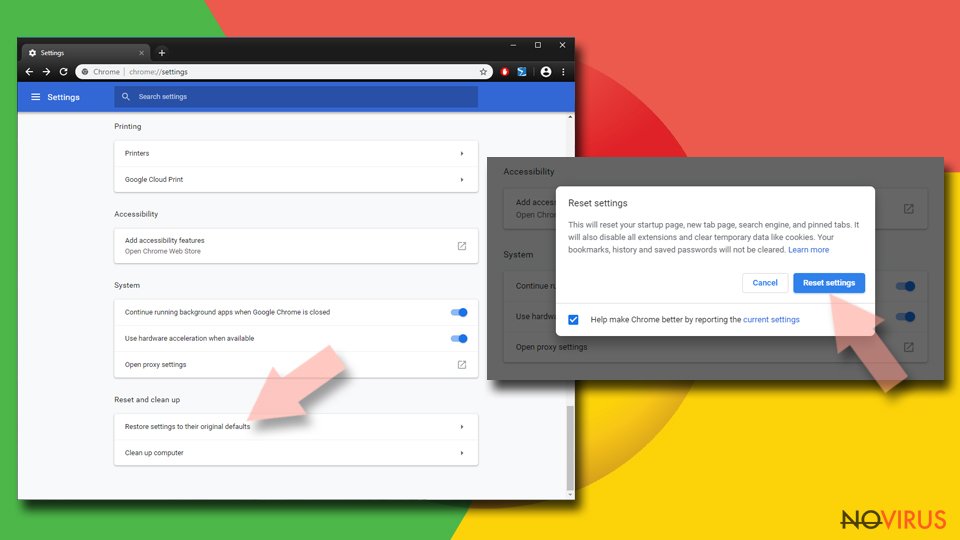
Reset Google Chrome fully:
You might need to reset Google Chrome and properly eliminate all the unwanted components:
- Go to Chrome Settings.
- Once there, scroll down to expand Advanced section.
- Scroll down to choose Reset and clean up.
- Click Restore settings to their original defaults.
- Click Reset settings again.
Delete Nbryb.com from Safari
Get rid of questionable extensions from Safari:
- Click Safari.
- Then go to Preferences…
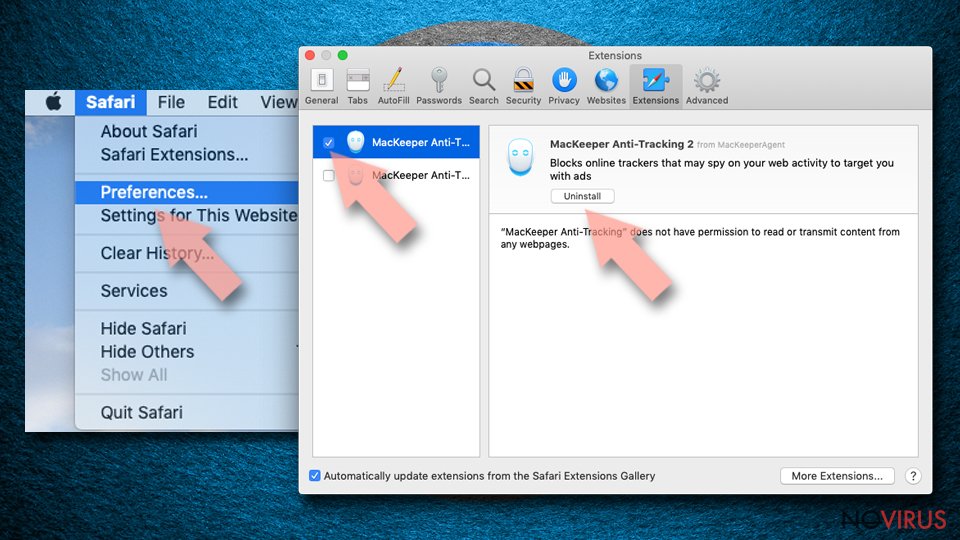
- Choose Extensions on the menu.
- Select the unwanted extension and then pick Uninstall.
Clear cookies from Safari:
- Click Safari.
- Choose Clear History…
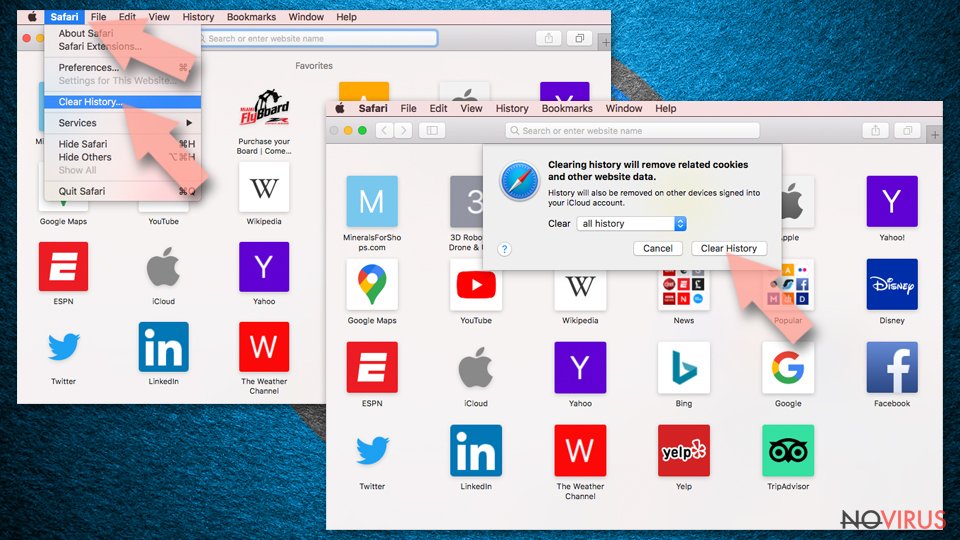
- From the drop-down menu under Clear, find and pick all history.
- Confirm with Clear History.
Reset Safari fully:
- Click Safari and then Preferences…
- Choose the Advanced tab.
- Tick the Show Develop menu in the menu bar.
- From the menu bar, click Develop.
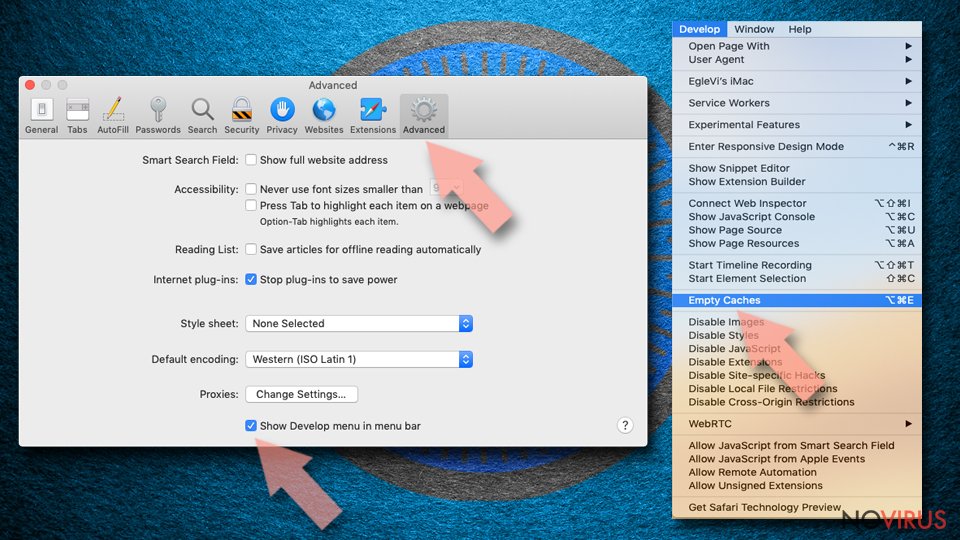
- Then select Empty Caches.
Even if you have completed all the steps above, we still strongly recommend you to scan your computer system with a powerful anti-malware software. It is advisable to do that because an automatic malware removal tool can detect and delete all remains of Nbryb.com, for instance, its registry keys. The anti-malware program can help you to easily detect and eliminate possibly dangerous software and malicious viruses in an easy way. You can use any of our top-rated malware removal programs: FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes.
How to prevent from getting adware
Prevent the government from spying on you
As there is a growing debate in government about collecting users' data and spying on citizens, you should take a closer look at this issue and find out what shady ways of gathering information can be used to collect information about you. You need to browse anonymously if you want to avoid any government-initiated spying and tracking of information.
You can enjoy secure internet browsing and minimize the risk of intrusion into your system if you use Private Internet Access VPN program. This VPN application creates a virtual private network and provides access to the required data without any content restrictions.
Control government and other third party access to your data and ensure safe web browsing. Even if you do not engage in illegal activities and trust your ISP, we recommend being careful about your security. You should take extra precautions and start using a VPN program.
Reduce the threat of viruses by backing up your data
Due to their own careless behavior, computer users can suffer various losses caused by cyber infections. Viruses can affect the functionality of the software or directly corrupt data on your system by encrypting it. These problems can disrupt the system and cause you to lose personal data permanently. There is no such threat if you have the latest backups, as you can easily recover lost data and get back to work.
It is recommended to update the backups in parallel each time the system is modified. This way, you will be able to access the latest saved data after an unexpected virus attack or system failure. By having the latest copies of important documents and projects, you will avoid serious inconveniences. File backups are especially useful if malware attacks your system unexpectedly. We recommend using the Data Recovery Pro program to restore the system.