Uninstall Jaff virus (Uninstall Guide) - May 2017 updated
Jaff virus Removal Guide
Description of Jaff ransomware
Jaff malware strikes again with a more attractive design
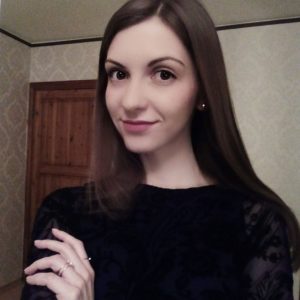
Jaff virus operates as a file-encrypting threat capable of encoding data with the combination of AES and AES ciphers. After the encryption process is finished, the files are marked with .jaff file extensions. The malware does not constrain itself simply by spreading through phishing emails; it targets users by disguising as PDF file attachments. In order for a victim to see the hidden content of the attachment, perpetrators suggest enabling macro settings. Once users allow the command, the malware starts its mission to encode files. It is capable of encrypting more than 424 different file formats. Recent analysis reveals that the felons launched a second malware campaign. The latest versions reflect modifications in its visual design. No drastic changes in the source code were implemented. Now it also appends .wlu file extensions and presents a new design. Previous versions left ReadMe.bmp, ReadMe.txt, ReadMe.html file or Jaff Decryption System notifications with instructions, but the latest edition presents its unique graphic user interface (GUI) – Jaff Decryptor. The former file informs the user about the desperate situation they are in and urges them purchasing 2 bitcoins (≈£3600). The malware has been active in the cyber space for a while already which implies that felons chose successful distribution and hacking strategies. Though this malware certainly should be treated with care, we recommend performing Jaff removal immediately. FortectIntego or Malwarebytes may be of service.
The racketeers of this malware surely made use from such well-known cyber menaces as Locky or Dridex. They have borrowed some ideas and successfully adopted them in their hacking strategy. Thus Jaff malware employs macro settings’ technique to gain more effectiveness. Furthermore, it actively exploits Necurs botnet which sends out malware samples disguised in DOCM files which are wrapped in PDF file attachments. Since the threat is devised for Windows OS, it will automatically open a dialogue box asking to ‘Enable content.’ After granting the permission, hidden VBS script activates the download process of the main payload. Such command also sends inquiries for a remote Command and Control server to inform the perpetrators. Furthermore, within minutes, the encryption process begins. By combining AES and RSA ciphering technique, a unique private key is created. It is directly interrelated with the public key which was used for data encryption. Acquiring private key would guarantee that all of the affected data would be successfully decrypted. However, now there are various programs which help users retrieve their lost and damaged personal files. Those, which employ shadow volume copies, provide higher data decryption guarantees. Nonetheless, Jaff felons thought it over thoroughly and set the command for the malware to delete these copies during the data decryption process.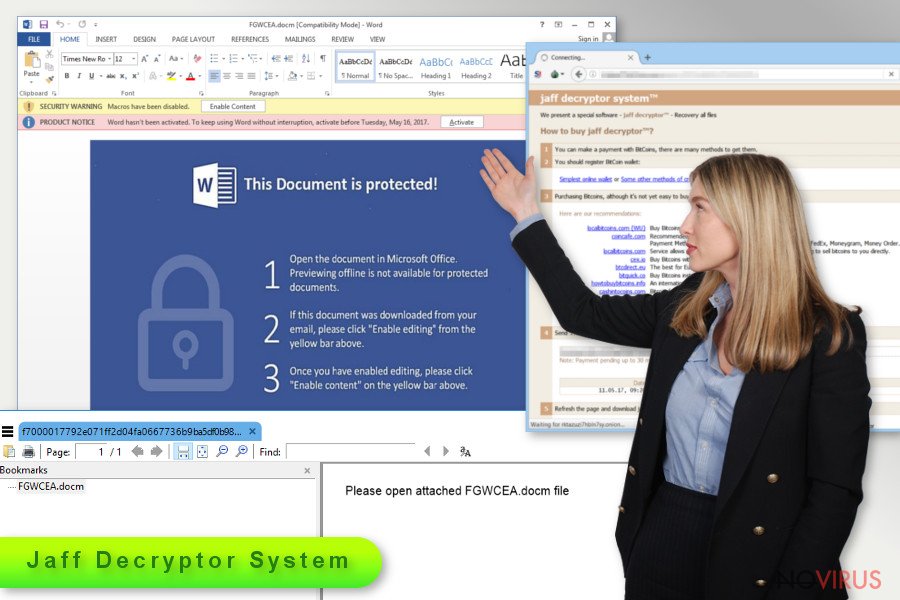
After completing the encryption stage, the ransom notifications are placed in every folder containing encrypted files. Jaff ransomware only evades altering system files. When GUI program opens, it displays victims’ ID and links to payment sites accessible only via Tor browser. Speaking of the payment interface, it instructs users how to purchase bitcoins. The first versions of the malware demanded approximately 1.82 BTC, but now the cyber villains raised the benchmark up to 3600 pounds. Indeed, the malware remains one of the most troublesome cyber issues, but it would be unwise to remit the payment. Driven by hopes to retrieve files and paying ransoms, users only encourage racketeers to continue the illegal business. To sum up, there are enough reasons to remove Jaff rather than follow the demands.
Transmission preferences
The key factor which predetermines the success of the malware is its usage of multiple channels and particularly botnets. In order for Jaff hijack process to complete successfully, Necurs botnet monitors the traffic of this malware. It plays a key role in sending malicious spam emails with corrupted nm.pdf attachments. Recently, the virus has been detected disguising under Copy of Invoice 99483713 or Invoice(58-0710) invoices. Note that the identification numbers differ depending on the recipient. Invoices and tax reports dominate among spam email subject topics. The fraudsters may also employ other techniques to trigger targetted users‘ curiosity and persuade them into opening attachments. Though this method still contains flaws which allow users to evade this cyber misfortune, if users have older versions of Adobe Reader, they risk facilitating the hacking process sooner. In short, older versions enable DOCM content automatically. Personal vigilance plays a significant role in ransomware prevention as in some cases anti-virus tools may fail to detect fraudulent files while only your sense of cautiousness might save from the troublesome outcomes of the malware.
Malspam is not the only way how a file-encrypting threat may occupy a device. Some ransomware developers prefer employing exploit kits, placed in torrent sharing networks, malicious scripts, video links or social network messages, and browser extensions in their malware distribution campaign. In that case, mere vigilance and cautiousness will not be sufficient in ceasing the attack. Thus, it is vital to install several security applications and keep them updated.
Jaff Decryption System elimination guide
Whether older or newer version has settled on the system, we offer one elimination method. Manual Jaff removal is not the option since the malware spreads its files throughout the entire operating system physical effort may not be fruitful. Time is of crucial importance when dealing with ransomware. Therefore, run the scan with malware elimination tool to remove Jaff virus. In case you cannot run the program, take a look at the below instructions. They instruct how to launch the computer in Safe Mode. This mode provides limited access, but it bypasses malware intervention and attempts to shut down the tool. There is also a second option if the first method fails to recover access.
Getting rid of Jaff virus. Follow these steps
In-depth guide for the Jaff elimination
Important! →
The elimination guide can appear too difficult if you are not tech-savvy. It requires some knowledge of computer processes since it includes system changes that need to be performed correctly. You need to take steps carefully and follow the guide avoiding any issues created due to improper setting changes. Automatic methods might suit you better if you find the guide too difficult.
Step 1. Launch Safe Mode with Networking
Safe Mode environment offers better results of manual virus removal
Windows 7 / Vista / XP
- Go to Start.
- Choose Shutdown, then Restart, and OK.
- When your computer boots, start pressing the F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) a few times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click the Start button and choose Settings.

- Scroll down to find Update & Security.

- On the left, pick Recovery.
- Scroll to find Advanced Startup section.
- Click Restart now.

- Choose Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.

- Choose 5) Enable Safe Mode with Networking.
Step 2. End questionable processes
You can rely on Windows Task Manager that finds all the random processes in the background. When the intruder is triggering any processes, you can shut them down:
- Press Ctrl + Shift + Esc keys to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes.
- Look for anything suspicious.
- Right-click and select Open file location.

- Go back to the Process tab, right-click and pick End Task.
- Delete the contents of the malicious folder.
Step 3. Check the program in Startup
- Press Ctrl + Shift + Esc on your keyboard again.
- Go to the Startup tab.
- Right-click on the suspicious app and pick Disable.

Step 4. Find and eliminate virus files
Data related to the infection can be hidden in various places. Follow the steps and you can find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive (C: is your main drive by default and is likely to be the one that has malicious files in) you want to clean.
- Scroll through the Files to delete and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Eliminate Jaff using System Restore
Since Jaff ransomware operates as a full-fledged file-encrypting threat, it may meddle with an anti-virus launch process.
-
Step 1: Restart your computer in Safe Mode with Command Prompt
Windows 7 / Vista / XP- Go to Start → Shutdown → Restart → OK.
- As soon as your computer starts, start pressing F8 key repeatedly before the Windows logo shows up.
-
Choose Command Prompt from the list

Windows 10 / Windows 8- Click on the Power button at the Windows login screen, and then press and hold Shift key on your keyboard. Then click Restart.
- Then select Troubleshoot → Advanced options → Startup Settings and click Restart.
-
Once your computer starts, select Enable Safe Mode with Command Prompt from the list of options in Startup Settings.

-
Step 2: Perform a system restore to recover files and settings
-
When the Command Prompt window appears, type in cd restore and press Enter.

-
Then type rstrui.exe and hit Enter..

-
In a new window that shows up, click the Next button and choose a restore point that was created before the infiltration of Jaff and then click on the Next button again.


-
To start system restore, click Yes.

-
When the Command Prompt window appears, type in cd restore and press Enter.
Bonus: Restore your files
Using the tutorial provided above you should be able to eliminate Jaff from the infected device. novirus.uk team has also prepared an in-depth data recovery guide which you will also find above.If you have created backups a while ago, they may be your only chance to restore all files.
There are a couple of methods you can apply to recover data encrypted by Jaff:
Does Data Recovery Pro restore files affected by Jaff virus?
It has been devised to recover corrupted, damaged, deleted and some of the encrypted files. The developers also promote its capability to restore lost od damaged email messages.
- Download Data Recovery Pro;
- Install Data Recovery on your computer following the steps indicated in the software’s Setup;
- Run the program to scan your device for the data encrypted by Jaff ransomware;
- Recover the data.
Windows Previous Versions option
In case System Restore was previously activated, you may benefit from this method. However, this method requires more time as you have to manually go through affected file and apply following steps.
- Right-click on the encrypted document you want to recover;
- Click “Properties” and navigate to “Previous versions” tab;
- In the “Folder versions” section look for the available file copies. Choose the desired version and press “Restore”.
Jeff Decryptor
At the moment, no official decryption software is available.
It is strongly recommended to take precautions and secure your computer from malware attacks. To protect your PC from Jaff and other dangerous viruses, you should install and keep a powerful malware removal tool, for instance, FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes.
How to prevent from getting ransomware
Securely connect to your website wherever you are
Sometimes you may need to log in to a content management system or server more often, especially if you are actively working on a blog, website, or different project that needs constant maintenance or that requires frequent content updates or other changes. Avoiding this problem can be easy if you choose a dedicated/fixed IP address. It's a static IP address that only belongs to a specific device and does not change when you are in different locations.
VPN service providers such as Private Internet Access can help you with these settings. This tool can help you control your online reputation and successfully manage your projects wherever you are. It is important to prevent different IP addresses from connecting to your website. With a dedicated/fixed IP address, VPN service, and secure access to a content management system, your project will remain secure.
Reduce the threat of viruses by backing up your data
Due to their own careless behavior, computer users can suffer various losses caused by cyber infections. Viruses can affect the functionality of the software or directly corrupt data on your system by encrypting it. These problems can disrupt the system and cause you to lose personal data permanently. There is no such threat if you have the latest backups, as you can easily recover lost data and get back to work.
It is recommended to update the backups in parallel each time the system is modified. This way, you will be able to access the latest saved data after an unexpected virus attack or system failure. By having the latest copies of important documents and projects, you will avoid serious inconveniences. File backups are especially useful if malware attacks your system unexpectedly. We recommend using the Data Recovery Pro program to restore the system.