Uninstall CryptoWall 3.0 virus (Clear Removal Instructions) - Apr 2016 updated
CryptoWall 3.0 virus Removal Guide
Description of CryptoWall 3.0 virus
How damaging is CryptoWall 3.0 virus?
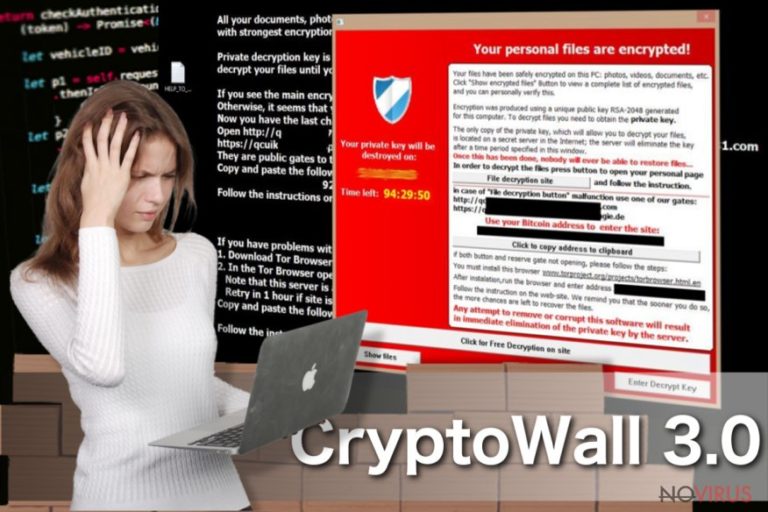
CryptoWall 3.0 virus is a ransomware-type virus which attacks computers and encrypts the most valuable information. After it locks out the data, it delivers a message informing the victim about the encrypted files. Moreover, it requires a ransom in exchange for the encrypted data. Users should not pay the money because cyber criminals might not return the data in exchange for it. This ransomware was released right after the success of the first version of this cyber threat which is called Cryptowall. In this article, we will provide the essential information about it and instructions on CryptoWall 3.0 removal.
CryptoWall 3.0 ransomware: what’s new and what’s old
The original version of CryptoWall struck the world in 2014 after infiltrating millions of computers worldwide. The US, Canada, Brazil, Germany, Turkey, Japan fell into the main victim list. Surprisingly, the most of European and Central Asia states have escaped the assault of this treacherous virus. Speaking of CryptoWall 3.0, it sprung to life in January 2015. It also targeted the same countries. Within its time of the rampage, it has already wheedled out more than £230 million. You might wonder, why this virus still roams freely in the virtual world? The problem is that it uses an exquisite RSA- 2048 algorithm to encrypt the data. Moreover, it employs anonymous Tor gateway for users to transfer the money. Likewise, IT security specialists are still struggling to trace the source domains of CryptoWall 3.0 ransomware.
Speaking of the distribution ways, the virus spreads via infected spam attachments. It has been discovered that mostly bot.exe, internal_31572.scr are spread as the files containing the ransomware. The improved version of CryptoWall 3.0 malware pointed its attention towards exploit kits as well. These malicious files are extremely treacherous since they can come in various forms: macro codes, trojans, minor infected files, scripts, etc. Due to their peculiarity to disguise themselves masterfully in the system, they might be an omen for future ransomware attacks. Therefore, it has been spotted that 1/3 of the ransomware distributions comprise these exploit kits. Internet users are recommended to install an anti-spyware program, such as FortectIntego, which detects and deletes such files. It might also be the first step to remove CryptoWall 3.0.
Furthermore, as mentioned before the virus uses anonymous Tor gateway. The interesting part is that it leads to paytoc4gtpn5cz12.torforall.com/. Once users download the suggested browser and follow payment instructions, they can be pointed to torman2.com, torwoman.com, and torroadsters.com as well. So you should beware of those websites if you accidentally spot them somewhere in the vast universe of the Internet. Additionally, the developers of CryptoWall 3.0 decided to update the virus in terms of raising the ransom amount. Infected users are frightened into paying the money within seven days. Otherwise, the ransom doubles. Certainly, they should not pay the ransom. The cyber criminals do not give any assuring guarantees to return the data.
CryptoWall 3.0 removal guide
The fact that cyber criminals keep generating newer versions of CryptoWall 3.0 virus reflects tits notorious success. Unfortunately, neither cyber criminals nor the virus itself has been terminated yet. Therefore, IT specialists keep working to trace the source domains of the virus, but it seems that cyber criminals are still one step ahead. However, there is good news as well. It is possible to choose from a broad variety of anti-spyware programs which can remove CryptoWall 3.0 and related exploit kits. Moreover, if your computer has been infected, remove the text files left by the ransomware: HELP_DECRYPT (.TXT and .HTML). Certainly, getting rid of the files will not eliminate the virus. However, regarding the fact that they are related, it is a necessity to delete everything that points to the virus. After you install an anti-spyware program, you should also check the manual removal instructions provided by our specialists. Lastly, you ought to employ the back-up function of the operating system to create the copies of precious information in case CryptoWall 3.0 attempts to infect your computer again.
Getting rid of CryptoWall 3.0 virus. Follow these steps
In-depth guide for the CryptoWall 3.0 elimination
Important! →
The elimination guide can appear too difficult if you are not tech-savvy. It requires some knowledge of computer processes since it includes system changes that need to be performed correctly. You need to take steps carefully and follow the guide avoiding any issues created due to improper setting changes. Automatic methods might suit you better if you find the guide too difficult.
Step 1. Launch Safe Mode with Networking
Safe Mode environment offers better results of manual virus removal
Windows 7 / Vista / XP
- Go to Start.
- Choose Shutdown, then Restart, and OK.
- When your computer boots, start pressing the F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) a few times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click the Start button and choose Settings.

- Scroll down to find Update & Security.

- On the left, pick Recovery.
- Scroll to find Advanced Startup section.
- Click Restart now.

- Choose Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.

- Choose 5) Enable Safe Mode with Networking.
Step 2. End questionable processes
You can rely on Windows Task Manager that finds all the random processes in the background. When the intruder is triggering any processes, you can shut them down:
- Press Ctrl + Shift + Esc keys to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes.
- Look for anything suspicious.
- Right-click and select Open file location.

- Go back to the Process tab, right-click and pick End Task.
- Delete the contents of the malicious folder.
Step 3. Check the program in Startup
- Press Ctrl + Shift + Esc on your keyboard again.
- Go to the Startup tab.
- Right-click on the suspicious app and pick Disable.

Step 4. Find and eliminate virus files
Data related to the infection can be hidden in various places. Follow the steps and you can find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive (C: is your main drive by default and is likely to be the one that has malicious files in) you want to clean.
- Scroll through the Files to delete and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Eliminate CryptoWall 3.0 using System Restore
-
Step 1: Restart your computer in Safe Mode with Command Prompt
Windows 7 / Vista / XP- Go to Start → Shutdown → Restart → OK.
- As soon as your computer starts, start pressing F8 key repeatedly before the Windows logo shows up.
-
Choose Command Prompt from the list

Windows 10 / Windows 8- Click on the Power button at the Windows login screen, and then press and hold Shift key on your keyboard. Then click Restart.
- Then select Troubleshoot → Advanced options → Startup Settings and click Restart.
-
Once your computer starts, select Enable Safe Mode with Command Prompt from the list of options in Startup Settings.

-
Step 2: Perform a system restore to recover files and settings
-
When the Command Prompt window appears, type in cd restore and press Enter.

-
Then type rstrui.exe and hit Enter..

-
In a new window that shows up, click the Next button and choose a restore point that was created before the infiltration of CryptoWall 3.0 and then click on the Next button again.


-
To start system restore, click Yes.

-
When the Command Prompt window appears, type in cd restore and press Enter.
It is strongly recommended to take precautions and secure your computer from malware attacks. To protect your PC from CryptoWall 3.0 and other dangerous viruses, you should install and keep a powerful malware removal tool, for instance, FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes.
How to prevent from getting ransomware
Prevent the government from spying on you
As there is a growing debate in government about collecting users' data and spying on citizens, you should take a closer look at this issue and find out what shady ways of gathering information can be used to collect information about you. You need to browse anonymously if you want to avoid any government-initiated spying and tracking of information.
You can enjoy secure internet browsing and minimize the risk of intrusion into your system if you use Private Internet Access VPN program. This VPN application creates a virtual private network and provides access to the required data without any content restrictions.
Control government and other third party access to your data and ensure safe web browsing. Even if you do not engage in illegal activities and trust your ISP, we recommend being careful about your security. You should take extra precautions and start using a VPN program.
Recover files damaged by a dangerous malware attack
Despite the fact that there are various circumstances that can cause data to be lost on a system, including accidental deletion, the most common reason people lose photos, documents, videos, and other important data is the infection of malware.
Some malicious programs can delete files and prevent the software from running smoothly. However, there is a greater threat from the dangerous viruses that can encrypt documents, system files, and images. Ransomware-type viruses focus on encrypting data and restricting users’ access to files, so you can permanently lose personal data when you download such a virus to your computer.
The ability to unlock encrypted files is very limited, but some programs have a data recovery feature. In some cases, the Data Recovery Pro program can help recover at least some of the data that has been locked by a virus or other cyber infection.







