Uninstall BTC virus (Uninstall Guide) - Apr 2017 updated
BTC virus Removal Guide
Description of BTC ransomware
BTC ransomware – another menace in the cyber space
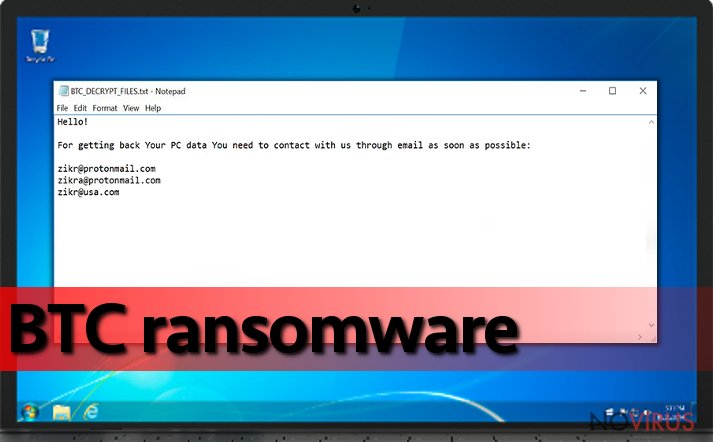
The first signs of BTC or alternatively called BTCLocker were detected already on the last months of 2016. Specialists suspect it to be the derivative version of Radamant virus. On the other hand, it also leads to another file-encrypting malware called CryptoMix. It already gave birth to a dozen new malware. The acronym of the malware supposedly stands for bitcoin. Such name was also given due to another feature of the malware – after infiltrating the system, the malware appends .BTC file extension to encrypted documents. Further information on data recovery is presented in BTC_DECRYPT_FILES.txt or IDR__BTC_DECRYPT_FILES.txt. BTC ransomware authors do not miss the opportunity to alarm victims – the payment should be transmitted during the indicated period. It seems that the hackers are not apt in using Tor network and contact in more sophisticated ways. In the case of inquiry, victims should contact zikr@protonmail.com, zikra@protonmail.com, or zikr@usa.com. According to the reports, the felons of this malware are not inclined in returning the files after you pay. On the contrary, after you make the transaction, you will be demanded to pay an additional amount of money. Direct your attention to BTC removal. FortectIntego or Malwarebytes is one of the options to terminate the infection.
For some users, 0,5 (≈£500) or 1,5(≈£1300) bitcoins might seem like a sufficient sum of money to pay in order to retrieve the files. One of the most problematic issues when dealing with a file-encrypting threat is that you cannot rely on fraudsters’ sense of conscience. In the case of BTC malware, the authors seem to be even keener on breaking their word. We do not recommend downloading BTC Decrypter proposed by the cyber villains. Amid the hopes of returning the data, you might install a ‘long-term malware’ which get activated after some time. Such software is also speculated to have spyware elements. Instead, hurry up to remove BTC malware. On the other hand, less delicate malware might be prevented if you restart the system. Even if BTC modifies startup files, restart the device. This action might interfere with the encryption process. Other versions of the infections might trigger fake User Account Control messages. Do not rush to enable them. Hackers might forge the name of initiating the program and present it as a Microsoft Windows process. However, unexpectedly long file names or odd system locations might signal you of the malice. During the encryption, the device starts to underperform. Check whether no questionable tasks are activated in Task Manager.
Does this malware spread in any peculiar ways?
BTC virus does not stand out much considering its distribution techniques. In fact, you are most likely to get infected with it via a spam message. Unfortunately, users are still not aware of possible consequences after curiously opening unknown attachments. Later on, they might have to battle not only an elaborate virus but look for data decryption alternatives. In addition, ransomware might be disguised as an exploit kit. In order to improve the protection from such virtual menaces, you need to add an anti-spyware application to the current anti-virus program. On the final note, if your browser toolbar is loaded with a series of extensions and plug-ins, note that crypto-malware might take its disguise as well. Such cautiousness will reduce the probability of encountering BTC hijack.
Are there any guarantees that BTC ransomware is fully eliminated?
BTC removal may not be a highly difficult task. Entrust the elimination process to malware removal software. In case, you cannot launch it, you might find the below-displayed guide to be of use. At the very bottom of the page, there is a few suggestions on data recovery as well. Luckily, this malware seems to belong to the group of decryptable crypto-malware. Until then, you might restore your files either via backups or shadow volume copies. More information about the latter method is provided under ‘Bonus’ recovery headlines.
Getting rid of BTC virus. Follow these steps
In-depth guide for the BTC elimination
It might not be surprising if BTC ransomware shuts down the anti-virus utility forcefully. To regain access, launch the computer in Safe Mode with Networking.
Important! →
The elimination guide can appear too difficult if you are not tech-savvy. It requires some knowledge of computer processes since it includes system changes that need to be performed correctly. You need to take steps carefully and follow the guide avoiding any issues created due to improper setting changes. Automatic methods might suit you better if you find the guide too difficult.
Step 1. Launch Safe Mode with Networking
Safe Mode environment offers better results of manual virus removal
Windows 7 / Vista / XP
- Go to Start.
- Choose Shutdown, then Restart, and OK.
- When your computer boots, start pressing the F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) a few times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click the Start button and choose Settings.

- Scroll down to find Update & Security.

- On the left, pick Recovery.
- Scroll to find Advanced Startup section.
- Click Restart now.

- Choose Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.

- Choose 5) Enable Safe Mode with Networking.
Step 2. End questionable processes
You can rely on Windows Task Manager that finds all the random processes in the background. When the intruder is triggering any processes, you can shut them down:
- Press Ctrl + Shift + Esc keys to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes.
- Look for anything suspicious.
- Right-click and select Open file location.

- Go back to the Process tab, right-click and pick End Task.
- Delete the contents of the malicious folder.
Step 3. Check the program in Startup
- Press Ctrl + Shift + Esc on your keyboard again.
- Go to the Startup tab.
- Right-click on the suspicious app and pick Disable.

Step 4. Find and eliminate virus files
Data related to the infection can be hidden in various places. Follow the steps and you can find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive (C: is your main drive by default and is likely to be the one that has malicious files in) you want to clean.
- Scroll through the Files to delete and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Eliminate BTC using System Restore
System Restore is another function which restores full control of the device. Note that this action does delete the crypto-malware.
-
Step 1: Restart your computer in Safe Mode with Command Prompt
Windows 7 / Vista / XP- Go to Start → Shutdown → Restart → OK.
- As soon as your computer starts, start pressing F8 key repeatedly before the Windows logo shows up.
-
Choose Command Prompt from the list

Windows 10 / Windows 8- Click on the Power button at the Windows login screen, and then press and hold Shift key on your keyboard. Then click Restart.
- Then select Troubleshoot → Advanced options → Startup Settings and click Restart.
-
Once your computer starts, select Enable Safe Mode with Command Prompt from the list of options in Startup Settings.

-
Step 2: Perform a system restore to recover files and settings
-
When the Command Prompt window appears, type in cd restore and press Enter.

-
Then type rstrui.exe and hit Enter..

-
In a new window that shows up, click the Next button and choose a restore point that was created before the infiltration of BTC and then click on the Next button again.


-
To start system restore, click Yes.

-
When the Command Prompt window appears, type in cd restore and press Enter.
Bonus: Restore your files
Using the tutorial provided above you should be able to eliminate BTC from the infected device. novirus.uk team has also prepared an in-depth data recovery guide which you will also find above.There are a couple of methods you can apply to recover data encrypted by BTC:
Retrieve encrypted data by BTC virus the assistance of Data Recovery Pro
Data Recovery Pro may be practical in restoring lost and damaged emails as well.
- Download Data Recovery Pro;
- Install Data Recovery on your computer following the steps indicated in the software’s Setup;
- Run the program to scan your device for the data encrypted by BTC ransomware;
- Recover the data.
Opt for Windows Previous Versions feature
Windows Previous Versions feature is one of the alternative data recovery solutions. Note that you will need to go through each file individually. Note that this method is only fruitful if System Restore was enabled prior the attack.
- Right-click on the encrypted document you want to recover;
- Click “Properties” and navigate to “Previous versions” tab;
- In the “Folder versions” section look for the available file copies. Choose the desired version and press “Restore”.
Employ Radamant decrypter to recover the documents locked by BTCLocker
Radamant decrypter might come in handy deciphering your files.
It is strongly recommended to take precautions and secure your computer from malware attacks. To protect your PC from BTC and other dangerous viruses, you should install and keep a powerful malware removal tool, for instance, FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes.
How to prevent from getting ransomware
Securely connect to your website wherever you are
Sometimes you may need to log in to a content management system or server more often, especially if you are actively working on a blog, website, or different project that needs constant maintenance or that requires frequent content updates or other changes. Avoiding this problem can be easy if you choose a dedicated/fixed IP address. It's a static IP address that only belongs to a specific device and does not change when you are in different locations.
VPN service providers such as Private Internet Access can help you with these settings. This tool can help you control your online reputation and successfully manage your projects wherever you are. It is important to prevent different IP addresses from connecting to your website. With a dedicated/fixed IP address, VPN service, and secure access to a content management system, your project will remain secure.
Reduce the threat of viruses by backing up your data
Due to their own careless behavior, computer users can suffer various losses caused by cyber infections. Viruses can affect the functionality of the software or directly corrupt data on your system by encrypting it. These problems can disrupt the system and cause you to lose personal data permanently. There is no such threat if you have the latest backups, as you can easily recover lost data and get back to work.
It is recommended to update the backups in parallel each time the system is modified. This way, you will be able to access the latest saved data after an unexpected virus attack or system failure. By having the latest copies of important documents and projects, you will avoid serious inconveniences. File backups are especially useful if malware attacks your system unexpectedly. We recommend using the Data Recovery Pro program to restore the system.







