Uninstall CryptoMix virus (Uninstall Guide) - Aug 2017 updated
CryptoMix virus Removal Guide
Description of CryptoMix virus
The menace of CryptoMix lies in its distribution
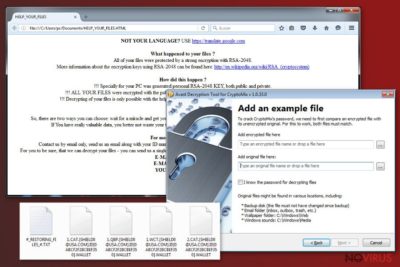
CryptoMix virus is an elaborate virtual threat detected already in the second half of last year. Since this cyber infection differs significantly from recently detected threats regarding its complexity and distribution methods, it has attracted IT experts’ attention. The malware appends a series of file extensions to the corrupted data: .lesli, id_7cb3b7bc1b34fa_email_xoomx@dr.com_.code , .ici, and several more.
At first glance, it looks like a compilation of infamous threats: Locky ransomware, Cerber virus, and CryptoWall. The ransom message resembles the former virtual threat, while the infected spam email mocks Cerber virus. In any case, the virus is able to encrypt data with a complex RSA-2048 encryption method.
Likewise, it is unwise to underestimate it. Even if this misfortune has befallen you, there is no need to succumb to the distress and comply with felons’ demands. It is understandable if you decide to transfer the money in the pursuit of retrieving files, but we offer you CryptoMix removal guide and alternative decryption methods.
By the end of the last year, the virus has entered the market as yet another crypto-malware. At that time, few might have anticipated that the improved version of the malware will reemerge several times again. It tries to follow the trodden path of Locky virus by imitating its ransom instructions and using the same encryption method – RSA-2048.
It generates a complex public key and the most viable method to retrieve unaffected documents is to obtain the matching private key. However, racketeers present instructions for users to remit the payment. Interestingly, that the original version of the virus did not present any Tor website or other domain for collecting money. Only the latter CryptoMix ransomware editions demand 5 bitcoins (approximately 4335 USD).
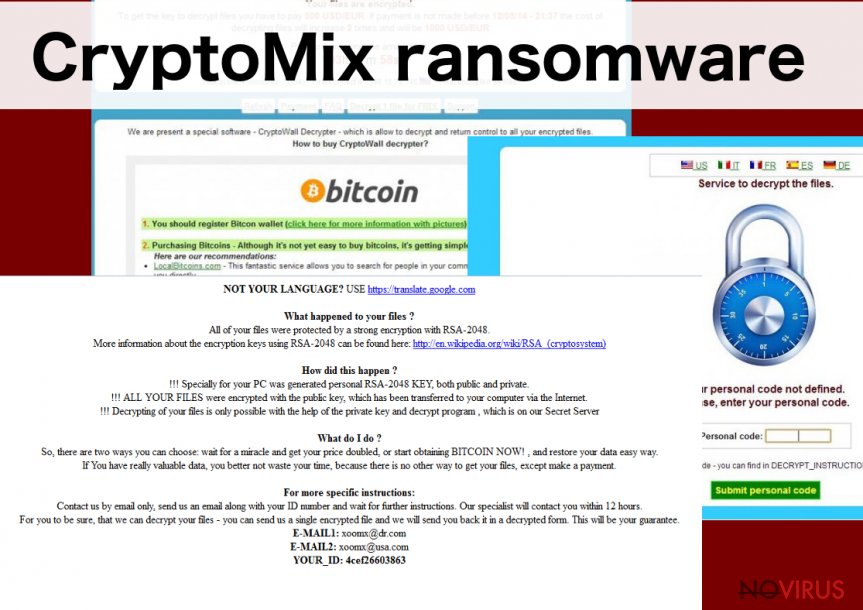
The money should be transferred to the specified email address. Even if the money is remitted, victims have to wait for several tiresome hours for the response. In comparison with the first malware, it indicates supl@post.com, while more recent versions display supl@oath.com email address.
The malware does not simply imitate the mentioned virus but it also includes key features of them. In the mocking ransom file of the virus, felons address users‘ and their sense of ‘honesty.’ Such bullying might enrage the victims if not the concern about the need to decode the files. Note that the felons offer their decryptor. However, this software might be a future menace rather than a tool decrypting the files. It might serve as the facilitator for a future CryptoMix hijack.
The transmission preferences of the malware
This cyber infection has been detected to be spreading via several channels: compromised emails, spam messages, and fake software updates. Elaborating on the first method, the signs of CryptoMix hijack have been detected in activaclinics.com, msimechanical.com, and nanotec.cnr.it.
Specifically, the payload is delivered through RIG-V exploit kit which is distinct from improved URL patterns and RC4 encryption method. In order to strengthen the attack of this virtual threat, the cyber gearheads even disguise it under a fake Adobe Flash Player update. AdobeFlashPlayer_7cb3b7bc1b34fa.exe might be found among the system files of the infected device.
Lastly, spam emails which urge to review the attached files about (un)delivered parcels might dwell a devastating malware. In order to reduce the risk of such infection, you should improve the overall protection of your system. Run regular scans and update security tools as well as system applications frequently.
Eradicating CryptoMix malware
The most efficient method to fully terminate CryptoMix virus is to install malware elimination utility, FortectIntego or Malwarebytes for instance. If the anti-virus program failed to prevent the assault of this file-encrypting threat, the former program would remove CryptoMix elements and registry keys.
Bear in mind that the malware removal software does not decrypt the files, so you might shift your attention to alternative options. Though the malware is more complicated than the majority of recently detected crypto-viruses, it has attracted more public attention. It means that there is a higher chance for the official decryptor to be released.
Getting rid of CryptoMix virus. Follow these steps
In-depth guide for the CryptoMix elimination
If you are struggling to complete CryptoMix removal, try using these instructions.
Important! →
The elimination guide can appear too difficult if you are not tech-savvy. It requires some knowledge of computer processes since it includes system changes that need to be performed correctly. You need to take steps carefully and follow the guide avoiding any issues created due to improper setting changes. Automatic methods might suit you better if you find the guide too difficult.
Step 1. Launch Safe Mode with Networking
Safe Mode environment offers better results of manual virus removal
Windows 7 / Vista / XP
- Go to Start.
- Choose Shutdown, then Restart, and OK.
- When your computer boots, start pressing the F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) a few times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click the Start button and choose Settings.

- Scroll down to find Update & Security.

- On the left, pick Recovery.
- Scroll to find Advanced Startup section.
- Click Restart now.

- Choose Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.

- Choose 5) Enable Safe Mode with Networking.
Step 2. End questionable processes
You can rely on Windows Task Manager that finds all the random processes in the background. When the intruder is triggering any processes, you can shut them down:
- Press Ctrl + Shift + Esc keys to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes.
- Look for anything suspicious.
- Right-click and select Open file location.

- Go back to the Process tab, right-click and pick End Task.
- Delete the contents of the malicious folder.
Step 3. Check the program in Startup
- Press Ctrl + Shift + Esc on your keyboard again.
- Go to the Startup tab.
- Right-click on the suspicious app and pick Disable.

Step 4. Find and eliminate virus files
Data related to the infection can be hidden in various places. Follow the steps and you can find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive (C: is your main drive by default and is likely to be the one that has malicious files in) you want to clean.
- Scroll through the Files to delete and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Eliminate CryptoMix using System Restore
-
Step 1: Restart your computer in Safe Mode with Command Prompt
Windows 7 / Vista / XP- Go to Start → Shutdown → Restart → OK.
- As soon as your computer starts, start pressing F8 key repeatedly before the Windows logo shows up.
-
Choose Command Prompt from the list

Windows 10 / Windows 8- Click on the Power button at the Windows login screen, and then press and hold Shift key on your keyboard. Then click Restart.
- Then select Troubleshoot → Advanced options → Startup Settings and click Restart.
-
Once your computer starts, select Enable Safe Mode with Command Prompt from the list of options in Startup Settings.

-
Step 2: Perform a system restore to recover files and settings
-
When the Command Prompt window appears, type in cd restore and press Enter.

-
Then type rstrui.exe and hit Enter..

-
In a new window that shows up, click the Next button and choose a restore point that was created before the infiltration of CryptoMix and then click on the Next button again.


-
To start system restore, click Yes.

-
When the Command Prompt window appears, type in cd restore and press Enter.
Bonus: Restore your files
Using the tutorial provided above you should be able to eliminate CryptoMix from the infected device. novirus.uk team has also prepared an in-depth data recovery guide which you will also find above.There are a couple of methods you can apply to recover data encrypted by CryptoMix:
Data Recovery Pro – as a solution
This application is a practical solution after an unexpected system crash. Recent ransomware activity also encouraged the creators of this tool to improve it. You might stand a chance to recover your files with this tool.
- Download Data Recovery Pro;
- Install Data Recovery on your computer following the steps indicated in the software’s Setup;
- Run the program to scan your device for the data encrypted by CryptoMix ransomware;
- Recover the data.
Opt for Windows Previous Versions feature
This method is effective only if System Restore function was activated on the computer before the invasion of this ransomware.
- Right-click on the encrypted document you want to recover;
- Click “Properties” and navigate to “Previous versions” tab;
- In the “Folder versions” section look for the available file copies. Choose the desired version and press “Restore”.
The effectiveness of ShadowExplorer
This program recreates the files using shadow volume copies. Likewise, there are more chances to recover the files to their original form.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Install Shadow Explorer on your computer following the instructions in the software’s Setup Wizard;
- Run the program. Navigate to the menu on the top-left corner and select a disk containing your encrypted files. Look through the available folders;
- When you find the folder you want to recover, right-click it and select “Export”. Also, choose where the recovered data will be stored.
It is strongly recommended to take precautions and secure your computer from malware attacks. To protect your PC from CryptoMix and other dangerous viruses, you should install and keep a powerful malware removal tool, for instance, FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes.
How to prevent from getting ransomware
Securely connect to your website wherever you are
Sometimes you may need to log in to a content management system or server more often, especially if you are actively working on a blog, website, or different project that needs constant maintenance or that requires frequent content updates or other changes. Avoiding this problem can be easy if you choose a dedicated/fixed IP address. It's a static IP address that only belongs to a specific device and does not change when you are in different locations.
VPN service providers such as Private Internet Access can help you with these settings. This tool can help you control your online reputation and successfully manage your projects wherever you are. It is important to prevent different IP addresses from connecting to your website. With a dedicated/fixed IP address, VPN service, and secure access to a content management system, your project will remain secure.
Recover files damaged by a dangerous malware attack
Despite the fact that there are various circumstances that can cause data to be lost on a system, including accidental deletion, the most common reason people lose photos, documents, videos, and other important data is the infection of malware.
Some malicious programs can delete files and prevent the software from running smoothly. However, there is a greater threat from the dangerous viruses that can encrypt documents, system files, and images. Ransomware-type viruses focus on encrypting data and restricting users’ access to files, so you can permanently lose personal data when you download such a virus to your computer.
The ability to unlock encrypted files is very limited, but some programs have a data recovery feature. In some cases, the Data Recovery Pro program can help recover at least some of the data that has been locked by a virus or other cyber infection.




















