Uninstall Zepto virus (Uninstall Guide) - 2017 updated
Zepto virus Removal Guide
Description of Zepto virus
Locky creators release a new virus called Zepto:
A new ransomware called Zepto virus has recently joined the Locky virus family. Locky has already made its creators a profit of millions of dollars, which apparently encouraged them to continue developing new malware. Bart ransomware or Zepto are just a few examples. Unfortunately, all Locky-related programs justify their name as being virtually undecryptable.
To this day, no fully-functional decryption key for these viruses has been invented. And it seems that it is going to stay that way for a while because Locky developers are not new to this sphere, they are aware of all the potential vulnerabilities of their malicious programs and have sufficient knowledge and skills to repair them. Thus, for the most part, the best way to fight these viruses is by avoiding their infiltration.
If this virus already managed to sneak into your computer, bare in mind that it is never too early to remove Zepto from your computer. The quicker you do it, the more likely you are to save your data before it gets locked. Anti-malware utilities, such as FortectIntego, are always a recommended option to go for if you seek fast and guaranteed removal.
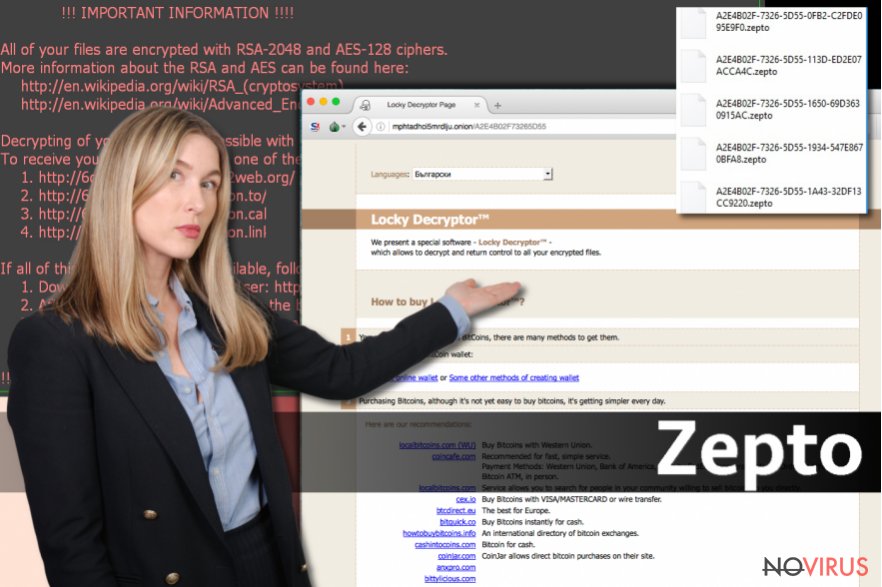
For the file encryption, Zepto uses RSA-2048 and AES-128 algorithms, already proven successful by Locky and other encryption-based malware. These ciphers were initially invented for the military purposes, so it is not surprising that ransomware developers turn to them as the best encryption solution.
After the file encryption is done, the files become inaccessible and instead of their regular names, the virus ads particular code, featuring encrypted computer’s ID and a .zepto extension appended at the end. Since such files are impossible to decrypt for the regular users, the ransomware creators quickly offer their ‘solution’.
File recovery instructions are presented in two documents, which appear on every infected computer folder. _[2 chars]_HELP_instructions.html and _[2 chars]_HELP_instructions.txt files feature information the information about data recovery, indicate addresses of the payments sites and demand the victims to pay 4 Bitcoins (around 2541 USD) in return of their files.
If you even consider sacrificing such a large sum for your files, you should be aware that this will not necessarily help you recover your data. The hackers can simply disappear with your money without providing any explanation. Thus, although Zepto removal does not recover data but it eliminates this malicious script from your computer and ensures your data’s safety in the future.
What can you do to protect your device from ransomware attack?
As we have pointed out previously, the best way to protect your data from being encrypted is by preventing the virus infection. There are several important rules you should follow to strengthen your computer’s security:
- Obtain an antivirus utility to monitor your system’s security status and protect it from malware;
- Enable automatic updates on all of your software; do not download random updates you may be offered online and always check the official site for new releases;
- Most importantly, backup your data. Regular backup is probably the only reliable option for your data protection. Keep in mind, though, that your important files must be stored on removable drives which should be unplugged from the computer after the data transfer.
- Finally, if you receive an invoice, speeding penalty notice, CV or similar letter in your email, do not rush downloading the attached file, because it might be a ransomware in disguise.
Where am I most likely to get infected with ransomware?
As you might have already understood from the protection against ransomware section of this article, these viruses tend to spread through infected email attachments.
The ransomware creators set up fake email accounts under the names of important institutions or organisations and try trick their victims into download supposedly important information, attached to the email. Usually, viruses use completely legitimate-looking Word documents which, in reality, contain a malicious script. This script can be activated immediately if the Word Macros function is enabled or ask the victims to enable it themselves.
If you receive such a request, do not enable Macros, because you will simply unleash the virus and lose your files. Remember, though, that the virus may come in JS format too, so you have to beware.
Generally speaking, interacting with any suspicious content online is unsafe. A variety of techniques can be used to trick you into downloading ransomware on your computer, and the list of the ways in which you might get infected is only expanding. Thus, you should take your computer’s security in consideration and follow computer security recommendations above.
Zepto ransomware removal recommendations:
Zepto removal is not an easy task, and it is definitely not for everyone. If you are less experienced, it is better that you rely on a professional anti-malware to deal with this problem.
Even if you are not new to the virus removal, automatic tools can significantly facilitate the process. It is also possible that the virus will try to obfuscate the removal by messing with your antivirus. Luckily, we have a solution if such situation ever occurs. Follow the steps indicated below and we are sure you will remove Zepto without any trouble.
Getting rid of Zepto virus. Follow these steps
In-depth guide for the Zepto elimination
Important! →
The elimination guide can appear too difficult if you are not tech-savvy. It requires some knowledge of computer processes since it includes system changes that need to be performed correctly. You need to take steps carefully and follow the guide avoiding any issues created due to improper setting changes. Automatic methods might suit you better if you find the guide too difficult.
Step 1. Launch Safe Mode with Networking
Safe Mode environment offers better results of manual virus removal
Windows 7 / Vista / XP
- Go to Start.
- Choose Shutdown, then Restart, and OK.
- When your computer boots, start pressing the F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) a few times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click the Start button and choose Settings.

- Scroll down to find Update & Security.

- On the left, pick Recovery.
- Scroll to find Advanced Startup section.
- Click Restart now.

- Choose Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.

- Choose 5) Enable Safe Mode with Networking.
Step 2. End questionable processes
You can rely on Windows Task Manager that finds all the random processes in the background. When the intruder is triggering any processes, you can shut them down:
- Press Ctrl + Shift + Esc keys to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes.
- Look for anything suspicious.
- Right-click and select Open file location.

- Go back to the Process tab, right-click and pick End Task.
- Delete the contents of the malicious folder.
Step 3. Check the program in Startup
- Press Ctrl + Shift + Esc on your keyboard again.
- Go to the Startup tab.
- Right-click on the suspicious app and pick Disable.

Step 4. Find and eliminate virus files
Data related to the infection can be hidden in various places. Follow the steps and you can find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive (C: is your main drive by default and is likely to be the one that has malicious files in) you want to clean.
- Scroll through the Files to delete and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Eliminate Zepto using System Restore
-
Step 1: Restart your computer in Safe Mode with Command Prompt
Windows 7 / Vista / XP- Go to Start → Shutdown → Restart → OK.
- As soon as your computer starts, start pressing F8 key repeatedly before the Windows logo shows up.
-
Choose Command Prompt from the list

Windows 10 / Windows 8- Click on the Power button at the Windows login screen, and then press and hold Shift key on your keyboard. Then click Restart.
- Then select Troubleshoot → Advanced options → Startup Settings and click Restart.
-
Once your computer starts, select Enable Safe Mode with Command Prompt from the list of options in Startup Settings.

-
Step 2: Perform a system restore to recover files and settings
-
When the Command Prompt window appears, type in cd restore and press Enter.

-
Then type rstrui.exe and hit Enter..

-
In a new window that shows up, click the Next button and choose a restore point that was created before the infiltration of Zepto and then click on the Next button again.


-
To start system restore, click Yes.

-
When the Command Prompt window appears, type in cd restore and press Enter.
It is strongly recommended to take precautions and secure your computer from malware attacks. To protect your PC from Zepto and other dangerous viruses, you should install and keep a powerful malware removal tool, for instance, FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes.
How to prevent from getting ransomware
Securely connect to your website wherever you are
Sometimes you may need to log in to a content management system or server more often, especially if you are actively working on a blog, website, or different project that needs constant maintenance or that requires frequent content updates or other changes. Avoiding this problem can be easy if you choose a dedicated/fixed IP address. It's a static IP address that only belongs to a specific device and does not change when you are in different locations.
VPN service providers such as Private Internet Access can help you with these settings. This tool can help you control your online reputation and successfully manage your projects wherever you are. It is important to prevent different IP addresses from connecting to your website. With a dedicated/fixed IP address, VPN service, and secure access to a content management system, your project will remain secure.
Recover files damaged by a dangerous malware attack
Despite the fact that there are various circumstances that can cause data to be lost on a system, including accidental deletion, the most common reason people lose photos, documents, videos, and other important data is the infection of malware.
Some malicious programs can delete files and prevent the software from running smoothly. However, there is a greater threat from the dangerous viruses that can encrypt documents, system files, and images. Ransomware-type viruses focus on encrypting data and restricting users’ access to files, so you can permanently lose personal data when you download such a virus to your computer.
The ability to unlock encrypted files is very limited, but some programs have a data recovery feature. In some cases, the Data Recovery Pro program can help recover at least some of the data that has been locked by a virus or other cyber infection.







