Remove Your computer has been locked (Dec 2016 updated) - Easy-to-follow Removal Guide
Your computer has been locked Removal Guide
Description of 'Your computer has been locked' scam
Information about ‘Your computer has been locked’ virus
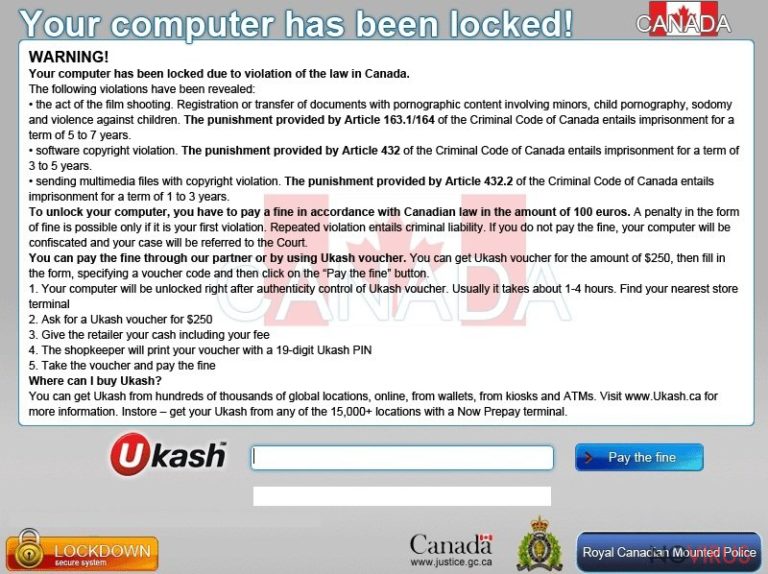
‘Your computer has been locked’ virus belongs to the ransomware category; however, it has features of Trojan and tech support scam. The virus spreads using tricky methods and users rarely notice when it happened. However, after the attack ‘Your computer has been locked’ ransomware delivers a fake lock screen informing about the illegal activities, for example, downloading child pornography, spreading spam, illegally using copyrighted content, etc. Keep in mind that legal institutions, such as Royal Canadian Mounted Police or the Department of Justice, do not ask making a particular fee through Ukash, Paysafecard, Moneypak or similar payment systems. We understand that many computer users might get scared seeing this notification; however, you should not stress out and attentively look through the message again. There might be some grammar mistakes or typos. Evaluate this information critically. It’s doubtful that governmental or federal institutions deliver poorly written messages. After analysis, probably you will need advice on how to remove ‘Your computer has been locked’ scam from the computer. The easiest way is to use FortectIntego; however, detailed removal instructions we will provide at the end of the article.
‘Your computer has been locked’ virus has several versions. The first version uses psychological terror and blackmails victims to pay the ransom if they don’t want to lose their personal files. However, if your files have been encrypted, you should try using this code which is supposed to restore all your files: 01548764GHEZG784. Another variant of ‘Your computer has been locked’ malware delivers fake warnings and tries to convince users to call a technical support service +62 0678 8516 9823. The alert informs that computer has been infected with viruses and disclose about other operating system’s error. Well, looking from the broader perspective, your PC has been infected; however, you should not call any provided number. Keep in mind that these calls may cost you a lot, and we don’t only talk about the huge phone bill. Scammers may trick you into purchasing fake software or install remote control tools and give them full access to your PC. Criminals will not fix your computer’s errors; they just cause you serious problems. Instead of that, you have to initiate ‘Your computer has been locked’ removal. Some versions of malware can get access to the affected computer’s webcam and show victim the live view from his or her home. It allows hackers to scare victims even more and encourage them to pay the ransom faster.
Methods of distribution
‘Your computer has been locked’ ransomware spread using several methods. It may infect computers via malicious and legitimate websites, exploit kits, illegal file-sharing domains or spam email attachments. Malware is waiting for inattentive and careless computer users everywhere. Crooks may send an infected document via email and pretend to be from bank, governmental organisation or other reputable institution. Unfortunately, it’s the most popular and effective ransomware distribution method. Fortunately, computer users can minimise the risk of ransomware attack by installing a reputable antivirus program, downloading only legal software from the reliable sources, keeping all their programs updated and avoiding potentially dangerous websites, suspicious email attachments, and ads.
Obliteration of the ‘Your computer has been locked’ ransomware
For ‘Your computer has been locked’ removal you will need a strong and professional anti-malware program. We recommend scanning your infected PC with FortectIntego or SpyHunter 5Combo Cleaner. Besides these programs will protect your computer from other malware attacks in the future. Keep in mind that malware may not let you install or access security tools. It’s quite expected behaviour because developers try their best to get your money. Therefore, if you face some difficulties, have a look at our prepared step-by-step guide. It will help you remove ‘Your computer has been locked’ from the system.
Getting rid of Your computer has been locked. Follow these steps
In-depth guide for the Your computer has been locked elimination
Important! →
The elimination guide can appear too difficult if you are not tech-savvy. It requires some knowledge of computer processes since it includes system changes that need to be performed correctly. You need to take steps carefully and follow the guide avoiding any issues created due to improper setting changes. Automatic methods might suit you better if you find the guide too difficult.
Step 1. Launch Safe Mode with Networking
Safe Mode environment offers better results of manual virus removal
Windows 7 / Vista / XP
- Go to Start.
- Choose Shutdown, then Restart, and OK.
- When your computer boots, start pressing the F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) a few times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click the Start button and choose Settings.

- Scroll down to find Update & Security.

- On the left, pick Recovery.
- Scroll to find Advanced Startup section.
- Click Restart now.

- Choose Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.

- Choose 5) Enable Safe Mode with Networking.
Step 2. End questionable processes
You can rely on Windows Task Manager that finds all the random processes in the background. When the intruder is triggering any processes, you can shut them down:
- Press Ctrl + Shift + Esc keys to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes.
- Look for anything suspicious.
- Right-click and select Open file location.

- Go back to the Process tab, right-click and pick End Task.
- Delete the contents of the malicious folder.
Step 3. Check the program in Startup
- Press Ctrl + Shift + Esc on your keyboard again.
- Go to the Startup tab.
- Right-click on the suspicious app and pick Disable.

Step 4. Find and eliminate virus files
Data related to the infection can be hidden in various places. Follow the steps and you can find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive (C: is your main drive by default and is likely to be the one that has malicious files in) you want to clean.
- Scroll through the Files to delete and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Eliminate Your computer has been locked using System Restore
-
Step 1: Restart your computer in Safe Mode with Command Prompt
Windows 7 / Vista / XP- Go to Start → Shutdown → Restart → OK.
- As soon as your computer starts, start pressing F8 key repeatedly before the Windows logo shows up.
-
Choose Command Prompt from the list

Windows 10 / Windows 8- Click on the Power button at the Windows login screen, and then press and hold Shift key on your keyboard. Then click Restart.
- Then select Troubleshoot → Advanced options → Startup Settings and click Restart.
-
Once your computer starts, select Enable Safe Mode with Command Prompt from the list of options in Startup Settings.

-
Step 2: Perform a system restore to recover files and settings
-
When the Command Prompt window appears, type in cd restore and press Enter.

-
Then type rstrui.exe and hit Enter..

-
In a new window that shows up, click the Next button and choose a restore point that was created before the infiltration of Your computer has been locked and then click on the Next button again.


-
To start system restore, click Yes.

-
When the Command Prompt window appears, type in cd restore and press Enter.
Bonus: Restore your files
Using the tutorial provided above you should be able to eliminate Your computer has been locked from the infected device. novirus.uk team has also prepared an in-depth data recovery guide which you will also find above.There are a couple of methods you can apply to recover data encrypted by Your computer has been locked:
Data Recovery Pro
If ‘Your computer has been locked’ virus encrypted some of your files and you do not have data backups, this tool may recover at least some of your files.
- Download Data Recovery Pro;
- Install Data Recovery on your computer following the steps indicated in the software’s Setup;
- Run the program to scan your device for the data encrypted by Your computer has been locked ransomware;
- Recover the data.
ShadowExplorer
If this malware haven’t deleted Shadow Volume Copies, you can try recovering corrupted files using Shadow Explorer.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Install Shadow Explorer on your computer following the instructions in the software’s Setup Wizard;
- Run the program. Navigate to the menu on the top-left corner and select a disk containing your encrypted files. Look through the available folders;
- When you find the folder you want to recover, right-click it and select “Export”. Also, choose where the recovered data will be stored.
It is strongly recommended to take precautions and secure your computer from malware attacks. To protect your PC from Your computer has been locked and other dangerous viruses, you should install and keep a powerful malware removal tool, for instance, FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes.
How to prevent from getting ransomware
Securely connect to your website wherever you are
Sometimes you may need to log in to a content management system or server more often, especially if you are actively working on a blog, website, or different project that needs constant maintenance or that requires frequent content updates or other changes. Avoiding this problem can be easy if you choose a dedicated/fixed IP address. It's a static IP address that only belongs to a specific device and does not change when you are in different locations.
VPN service providers such as Private Internet Access can help you with these settings. This tool can help you control your online reputation and successfully manage your projects wherever you are. It is important to prevent different IP addresses from connecting to your website. With a dedicated/fixed IP address, VPN service, and secure access to a content management system, your project will remain secure.
Reduce the threat of viruses by backing up your data
Due to their own careless behavior, computer users can suffer various losses caused by cyber infections. Viruses can affect the functionality of the software or directly corrupt data on your system by encrypting it. These problems can disrupt the system and cause you to lose personal data permanently. There is no such threat if you have the latest backups, as you can easily recover lost data and get back to work.
It is recommended to update the backups in parallel each time the system is modified. This way, you will be able to access the latest saved data after an unexpected virus attack or system failure. By having the latest copies of important documents and projects, you will avoid serious inconveniences. File backups are especially useful if malware attacks your system unexpectedly. We recommend using the Data Recovery Pro program to restore the system.







