Uninstall XData virus (Uninstall Instructions) - May 2017 updated
XData virus Removal Guide
Description of XData ransomware
XData virus wreaks havoc in Ukraine
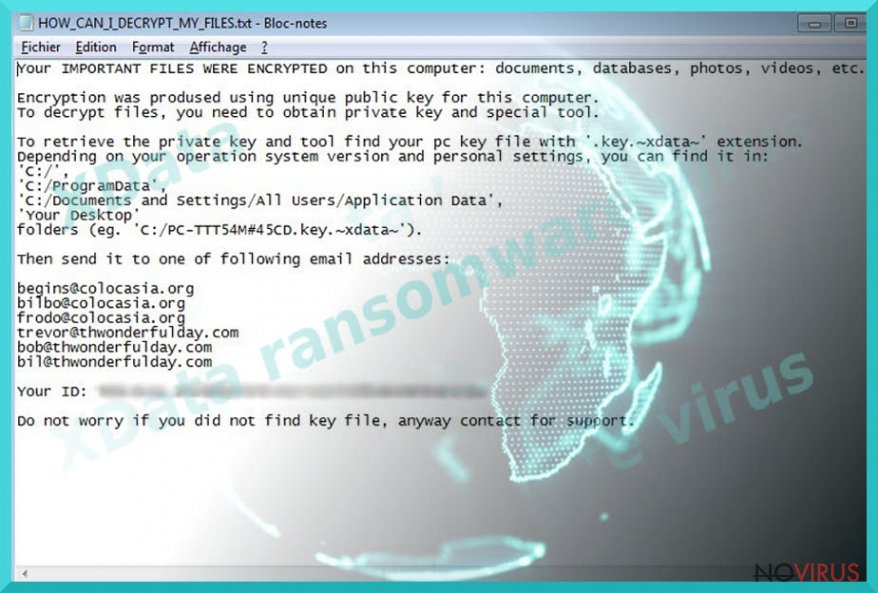
XData ransomware is a computer virus that encrypts data stored on the target computer and also on unmapped network shares. The ransomware surprisingly targets residents on Ukraine, although IT security experts received some reports from different countries as well. The virus locks personal victim’s files leaving .~xdata~ file extension on each of them, and then creates a ransom note called HOW_CAN_I_DECRYPT_MY_FILES.txt on the desktop. The ransom note suggests finding a .key.~xdata~ file on the system, and send it to one of the criminals’ email addresses – begins@colocasia.org, bilbo@colocasia.org, frodo@colocasia.org, trevor@thwonderfulday.com, bob@thwonderfulday.com, or bil@thwonderfulday.com. Although the ransom note doesn’t state the exact price of the data recovery key, victims report that cyber criminals demand 0.2 BTC in exchange for data decryption software. So far there are no reports if victims who paid managed to recover their files, so if you were attacked by the same ransomware as well, do not rush to buy Bitcoins. In fact, we do not recommend paying the ransom at all, because if you do, you will fund further ransomware projects, which is definitely not a praisable idea. To recover corrupted files, we suggest using data backups. Before you plug them into your computer, remove XDATA ransomware completely. It can be done by running a system scan with FortectIntego software.
On May 19, malware researchers announced that XData virus managed to infect more computers than WannaCry ransomware did in a whole week. According to reports, more than 95% of victims affected by the new ransomware were residents of Ukraine, which clearly shows that the attackers intentionally sought to wreak havoc in this country. Although it is unknown who organized the cyber attack, experts advise taking every possible measure to protect computers from malware because it is clear that ransomware authors can strike again soon. Sadly, no one knows which country is going to be the next victim. In case your computer gets infected, we suggest performing a full XData removal using instructions we provided. Keeping the malicious program on the system does no good and simply poses a threat to your privacy. If you were lucky enough not to become a victim of the described ransomware, we would like to remind you of general rules that can protect you from a ransomware attack.
Ransomware distribution tricks
Currently, experts are not so brave to name exact attack vectors used by ransomware authors, but we assume that it mainly spreads via spam. In other words, criminals send out thousands of emails to predetermined recipients and expect them to open files or links added to them. In case of success, the victim’s computer gets infected with the ransomware, which typically spawns such processes on the infected host: mssql.exe, mscomrpc.exe, msdns.exe and msdcom.exe. If you do not want to unknowingly invite these malicious files to your system, never open emails sent by unknown people. Even if the sender claims to be a representative of some well-known company, do not rush to believe such claims. Scammers tend to employ various social engineering techniques to trick victims into opening dangerous email attachments and URLs – please, do not fall for such tricks!
Remove XData malware and restore your files
Before you try to restore encrypted files, remove XData ransomware first. To identify all malicious files and affected Registry Keys, you will need to use anti-malware software. Please remember that unsuccessful attempts to find and remove ransomware files manually can result in various problems, such as system slowdowns, software crashes, errors, and even more. However, you need to know how to launch anti-malware software properly once the system is compromised. Therefore, we provided a detailed XData removal tutorial for you. If you do not have a data backup, please read our suggestions on how to recover files. One of the provided methods might recover your files.
Getting rid of XData virus. Follow these steps
In-depth guide for the XData elimination
This option should help you recover control of the device, in case the malware shuts down anti-virus tools and prevents you from terminating it any other way.
Important! →
The elimination guide can appear too difficult if you are not tech-savvy. It requires some knowledge of computer processes since it includes system changes that need to be performed correctly. You need to take steps carefully and follow the guide avoiding any issues created due to improper setting changes. Automatic methods might suit you better if you find the guide too difficult.
Step 1. Launch Safe Mode with Networking
Safe Mode environment offers better results of manual virus removal
Windows 7 / Vista / XP
- Go to Start.
- Choose Shutdown, then Restart, and OK.
- When your computer boots, start pressing the F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) a few times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click the Start button and choose Settings.

- Scroll down to find Update & Security.

- On the left, pick Recovery.
- Scroll to find Advanced Startup section.
- Click Restart now.

- Choose Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.

- Choose 5) Enable Safe Mode with Networking.
Step 2. End questionable processes
You can rely on Windows Task Manager that finds all the random processes in the background. When the intruder is triggering any processes, you can shut them down:
- Press Ctrl + Shift + Esc keys to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes.
- Look for anything suspicious.
- Right-click and select Open file location.

- Go back to the Process tab, right-click and pick End Task.
- Delete the contents of the malicious folder.
Step 3. Check the program in Startup
- Press Ctrl + Shift + Esc on your keyboard again.
- Go to the Startup tab.
- Right-click on the suspicious app and pick Disable.

Step 4. Find and eliminate virus files
Data related to the infection can be hidden in various places. Follow the steps and you can find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive (C: is your main drive by default and is likely to be the one that has malicious files in) you want to clean.
- Scroll through the Files to delete and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Eliminate XData using System Restore
-
Step 1: Restart your computer in Safe Mode with Command Prompt
Windows 7 / Vista / XP- Go to Start → Shutdown → Restart → OK.
- As soon as your computer starts, start pressing F8 key repeatedly before the Windows logo shows up.
-
Choose Command Prompt from the list

Windows 10 / Windows 8- Click on the Power button at the Windows login screen, and then press and hold Shift key on your keyboard. Then click Restart.
- Then select Troubleshoot → Advanced options → Startup Settings and click Restart.
-
Once your computer starts, select Enable Safe Mode with Command Prompt from the list of options in Startup Settings.

-
Step 2: Perform a system restore to recover files and settings
-
When the Command Prompt window appears, type in cd restore and press Enter.

-
Then type rstrui.exe and hit Enter..

-
In a new window that shows up, click the Next button and choose a restore point that was created before the infiltration of XData and then click on the Next button again.


-
To start system restore, click Yes.

-
When the Command Prompt window appears, type in cd restore and press Enter.
Bonus: Restore your files
Using the tutorial provided above you should be able to eliminate XData from the infected device. novirus.uk team has also prepared an in-depth data recovery guide which you will also find above.There are a couple of methods you can apply to recover data encrypted by XData:
Test Data Recovery Pro
Data Recovery Pro is a beneficial data recovery software that can easily restore corrupted or deleted files, so we suggest testing it on files encrypted by XData.
- Download Data Recovery Pro;
- Install Data Recovery on your computer following the steps indicated in the software’s Setup;
- Run the program to scan your device for the data encrypted by XData ransomware;
- Recover the data.
Test the ShadowExplorer tool
You can use Volume Shadow Copies to roll back your files to their previous state.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Install Shadow Explorer on your computer following the instructions in the software’s Setup Wizard;
- Run the program. Navigate to the menu on the top-left corner and select a disk containing your encrypted files. Look through the available folders;
- When you find the folder you want to recover, right-click it and select “Export”. Also, choose where the recovered data will be stored.
At the moment, files encrypted by XData ransomware cannot be decrypted for free
It is strongly recommended to take precautions and secure your computer from malware attacks. To protect your PC from XData and other dangerous viruses, you should install and keep a powerful malware removal tool, for instance, FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes.
How to prevent from getting ransomware
Prevent the government from spying on you
As there is a growing debate in government about collecting users' data and spying on citizens, you should take a closer look at this issue and find out what shady ways of gathering information can be used to collect information about you. You need to browse anonymously if you want to avoid any government-initiated spying and tracking of information.
You can enjoy secure internet browsing and minimize the risk of intrusion into your system if you use Private Internet Access VPN program. This VPN application creates a virtual private network and provides access to the required data without any content restrictions.
Control government and other third party access to your data and ensure safe web browsing. Even if you do not engage in illegal activities and trust your ISP, we recommend being careful about your security. You should take extra precautions and start using a VPN program.
Recover files damaged by a dangerous malware attack
Despite the fact that there are various circumstances that can cause data to be lost on a system, including accidental deletion, the most common reason people lose photos, documents, videos, and other important data is the infection of malware.
Some malicious programs can delete files and prevent the software from running smoothly. However, there is a greater threat from the dangerous viruses that can encrypt documents, system files, and images. Ransomware-type viruses focus on encrypting data and restricting users’ access to files, so you can permanently lose personal data when you download such a virus to your computer.
The ability to unlock encrypted files is very limited, but some programs have a data recovery feature. In some cases, the Data Recovery Pro program can help recover at least some of the data that has been locked by a virus or other cyber infection.







