Remove Trojan:Win32/CryptInject!ml (Free Removal Instructions) - Uninstall Guide
Trojan:Win32/CryptInject!ml Removal Guide
Description of Trojan:Win32/CryptInject!ml
Trojan:Win32/CryptInject!ml – a detection name for various types of malware on a Windows PC

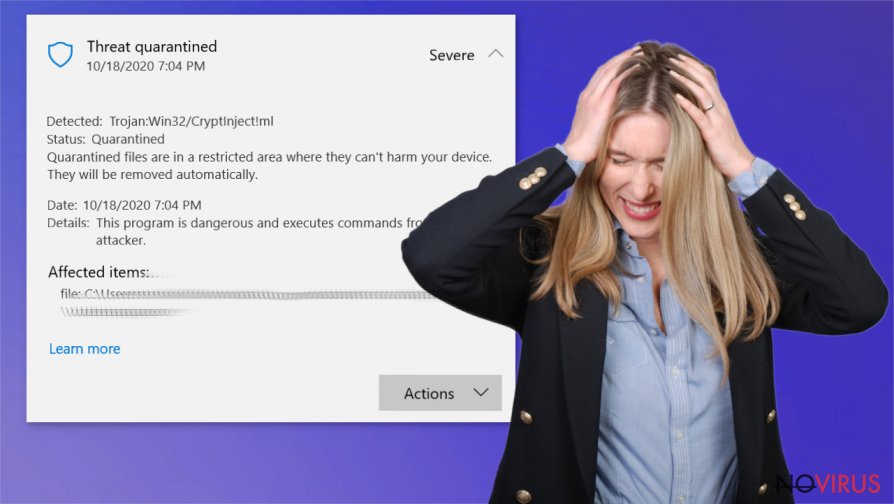
Trojan:Win32/CryptInject!ml is a computer virus that runs background processes. This type of infection can be programmed to exfiltrate sensitive data after downloading additional modules, perform crypto-mining activities, or lead to further device compromise due to additional payload injection.
While the detection might indicate serious malware infection, it is important to note that it's a generic name for particular malicious files or programs. Therefore, it is not uncommon to see heuristic detection as a false-positive, meaning that even completely legitimate files could be marked by security software due to behavioral patterns it recognizes as malicious (while they are not).
If, while performing a scheduled regular system check, you spot an alert, please immediately take action. Run the scan once more with the same default anti-malware tool or any other powerful AV software and remove Trojan:Win32/CryptInject!ml virus as soon as possible to prevent disastrous consequences in the future.
| name | Trojan:Win32/CryptInject!ml |
|---|---|
| Type | Trojan, malware |
| Issues | A threat protection alert pops up on the screen out of the blue. System performance might be lower |
| Distribution | Trojans, like most malware, are delivered with phishing email attachments, through hacked websites, RDP attacks |
| Virus removal | Trust dependable anti-malware software to eliminate such cyber threats from infected devices |
| System check | All malware damage system settings and its files in some way, to restore devices health to a pre-contamination phase, use the FortectIntego tool |
Malware like Trojan:Win32/CryptInject!ml infection can be delivered to your computer in various ways, from infected email attachments to RDP attacks, but more on that in the second part of this article. Infected devices might exhibit abnormal behavior, such as:
- freezing
- crashing
- slower overall performance
- severe lag, and others.
As soon as you spot any of these issues, you should scan your computer system with a trustworthy anti-malware software like SpyHunter 5Combo Cleaner or Malwarebytes, which would be capable of finding the infection even if it's hiding camouflaged as a background process by another name. If your AV tools detect it – remove Trojan:Win32/CryptInject!ml immediately.
Having this type of malware on your computer is extremely dangerous, as it could lead not only to slower performance but to data leakage, identity theft, financial loses due to the fact that it might download other malicious software that would be capable of keylogging, cryptocurrency mining, data exfiltration, etc.
Trojan:Win32/CryptInject!ml removal is of utmost importance. We suggest rebooting your computer and removing the malware infection in Safe Mode with Networking mode on for anti-malware tools to work without needless interruptions. A detailed guide on how to do it is provided at the bottom of this article.
Depending on how long Trojan:Win32/CryptInject!ml virus stayed on your device, it might have gotten its dirty hands on various system files and system settings. These changes might cause all types of performance and security issues, so we recommend using the FortectIntego or any other powerful system repair tool to restore the default settings and maintain your computer health at top-notch.
Popular cyberthreat delivery methods
Cybercriminals have many tools when it comes to malware delivery – spam emails, drive-by downloads from hacked sites, file-sharing platforms, Remote Desktop Protocol attacks, deceptive advertisements, and more. We're going to expand on one of them now.
Hackers love to exploit unaware users who decide to use software illegal activation toolkits, popularly known as cracks. File-sharing platforms, especially torrent sites, harbor various pirated software, and with some of it, their users are getting more than they anticipated.
Cybercriminals upload their created malware camouflaged as the latest, the most popular or anticipated game cracks, and sit and wait until unaware users download it. As soon as a malware payload file gets access to a computer system, it executes itself, and infection of the device is triggered. To evade such mishaps, refrain from using file-sharing platforms and be sure to scan all downloadable content with a reliable anti-malware tool.
Instructions for a successful Trojan:Win32/CryptInject!ml removal
As we've pointed out before, malware should be eliminated immediately after any signs of infection are spotted. To remove Trojan:Win32/CryptInject!ml with a push of few buttons, we advise using professional antimalware software such as SpyHunter 5Combo Cleaner or Malwarebytes.
Anti-malware virus databases should be up-to-date at all times. Once Trojan:Win32/CryptInject!ml removal is completed, users should take care of their computer registry and other core system settings and files by running a full system scan with the FortectIntego app and reverting any changes that the infection has executed.
Getting rid of Trojan:Win32/CryptInject!ml. Follow these steps
In-depth guide for the Trojan:Win32/CryptInject!ml elimination
You can access Safe Mode with Networking and perform a full system scan from there to ensure that all malware components are eliminated fully:
Important! →
The elimination guide can appear too difficult if you are not tech-savvy. It requires some knowledge of computer processes since it includes system changes that need to be performed correctly. You need to take steps carefully and follow the guide avoiding any issues created due to improper setting changes. Automatic methods might suit you better if you find the guide too difficult.
Step 1. Launch Safe Mode with Networking
Safe Mode environment offers better results of manual virus removal
Windows 7 / Vista / XP
- Go to Start.
- Choose Shutdown, then Restart, and OK.
- When your computer boots, start pressing the F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) a few times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click the Start button and choose Settings.

- Scroll down to find Update & Security.

- On the left, pick Recovery.
- Scroll to find Advanced Startup section.
- Click Restart now.

- Choose Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.

- Choose 5) Enable Safe Mode with Networking.
Step 2. End questionable processes
You can rely on Windows Task Manager that finds all the random processes in the background. When the intruder is triggering any processes, you can shut them down:
- Press Ctrl + Shift + Esc keys to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes.
- Look for anything suspicious.
- Right-click and select Open file location.

- Go back to the Process tab, right-click and pick End Task.
- Delete the contents of the malicious folder.
Step 3. Check the program in Startup
- Press Ctrl + Shift + Esc on your keyboard again.
- Go to the Startup tab.
- Right-click on the suspicious app and pick Disable.

Step 4. Find and eliminate virus files
Data related to the infection can be hidden in various places. Follow the steps and you can find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive (C: is your main drive by default and is likely to be the one that has malicious files in) you want to clean.
- Scroll through the Files to delete and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Eliminate Trojan:Win32/CryptInject!ml using System Restore
System restore feature can help with virus termination:
-
Step 1: Restart your computer in Safe Mode with Command Prompt
Windows 7 / Vista / XP- Go to Start → Shutdown → Restart → OK.
- As soon as your computer starts, start pressing F8 key repeatedly before the Windows logo shows up.
-
Choose Command Prompt from the list

Windows 10 / Windows 8- Click on the Power button at the Windows login screen, and then press and hold Shift key on your keyboard. Then click Restart.
- Then select Troubleshoot → Advanced options → Startup Settings and click Restart.
-
Once your computer starts, select Enable Safe Mode with Command Prompt from the list of options in Startup Settings.

-
Step 2: Perform a system restore to recover files and settings
-
When the Command Prompt window appears, type in cd restore and press Enter.

-
Then type rstrui.exe and hit Enter..

-
In a new window that shows up, click the Next button and choose a restore point that was created before the infiltration of Trojan:Win32/CryptInject!ml and then click on the Next button again.


-
To start system restore, click Yes.

-
When the Command Prompt window appears, type in cd restore and press Enter.
It is strongly recommended to take precautions and secure your computer from malware attacks. To protect your PC from Trojan:Win32/CryptInject!ml and other dangerous viruses, you should install and keep a powerful malware removal tool, for instance, FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes.
How to prevent from getting trojans
A proper web browser and VPN tool can guarantee better safety
As online spying becomes an increasing problem, people are becoming more interested in how to protect their privacy. One way to increase your online security is to choose the most secure and private web browser. But if you want complete anonymity and security when surfing the web, you need Private Internet Access VPN service. This tool successfully reroutes traffic across different servers, so your IP address and location remain protected. It is also important that this tool is based on a strict no-log policy, so no data is collected and cannot be leaked or made available to first or third parties. If you want to feel safe on the internet, a combination of a secure web browser and a Private Internet Access VPN will help you.
Reduce the threat of viruses by backing up your data
Due to their own careless behavior, computer users can suffer various losses caused by cyber infections. Viruses can affect the functionality of the software or directly corrupt data on your system by encrypting it. These problems can disrupt the system and cause you to lose personal data permanently. There is no such threat if you have the latest backups, as you can easily recover lost data and get back to work.
It is recommended to update the backups in parallel each time the system is modified. This way, you will be able to access the latest saved data after an unexpected virus attack or system failure. By having the latest copies of important documents and projects, you will avoid serious inconveniences. File backups are especially useful if malware attacks your system unexpectedly. We recommend using the Data Recovery Pro program to restore the system.







