Uninstall Tech Support Scam virus (Virus Removal Instructions) - Jan 2018 updated
Tech Support Scam virus Removal Guide
Description of Tech Support Scam
The operation principle of Tech Support Scams
Tech Support Scam is one of the trickiest and dishonest ways used to steal people's money online. The purpose of this virus is not to damage computers, but to swindle money from people by signing them up for useless services. So, you should never deal with Tech support scammers who will do anything to convince you that your computer is in a huge trouble and that you need to let someone to connect to it to solve the problem.
Several years ago scammers have been calling people and telling them various stories to wheedle massive amounts of money. Telephone scams are supposed to target elder people; however, nowadays scamming, as well as other crimes, went online and now target all internet users. Tech Support scammers use telephone, computer technologies and other methods to get virus inside victim’s computer or simply sign him or her up for useless services.
The virus spreads and acts similarly like adware programs. It travels bundled with freeware and users often let it inside when they install regular software with ‘Quick’ or ‘Recommended’ installation mode. After infiltration, the virus starts delivering warning notifications and pop-ups claiming that your computer is at high risk.
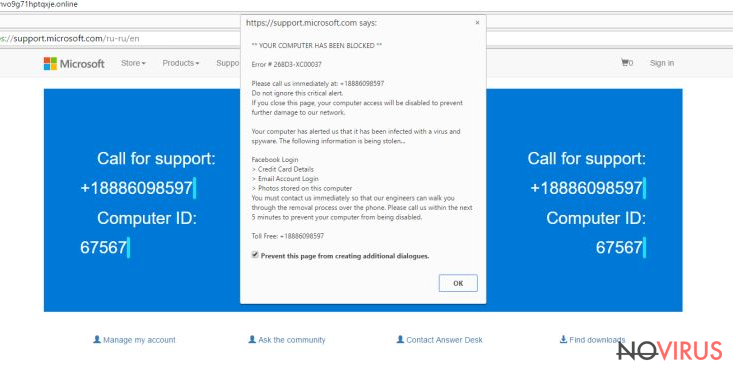
The trickiest feature is that scammers pretend to be from fake or well-known and reputable organizations such as Microsoft. Criminals might copy interface of various Microsoft support services perfectly. It ensures the bigger chances to swindle money from naïve computer users.
Many different Tech Support Scam viruses are spreading around the Internet; however, all of them try to convince users that their computers are vulnerable and need fixing. Scammers act in two ways: they encourage calling technical support staff and purchase software that is capable of repairing ‘serious’ errors. The call to tech support line might cost an enormous amount of money.
Also, scammers might be willing to get your personal information, and you should know that they are good psychologists have excellent communication skills. If you made a phone call and realised that you have been scammed, be careful and end the call immediately.
Besides, crooks are willing to get full access to your PC by asking you to install remote software! If you complete this request, they might install ransomware, Trojan horse and even steal your private data. What is worse, you might not realise what they are doing, because they might act like real support service and do some tricks on your PC.

When Tech Support Scam virus delivers a fake message about poor computer’s state or provides an alert with lots of detected errors, it also offers a chance to repair these problems. All you have to do is to purchase and install a particular program. Needless to say that these computer-related errors are fake just like offered malware removal program, so you have to be careful. Tech Support Scam virus removal is the only step you should take if you encountered suspicious warnings.
Recognizing Tech Support Scam virus
The virus delivers an excessive amount of notifications and pop-ups claiming that your PC is infected with various viruses. Bear in mind that reputable security tools do not provide so many warnings. Tech Support Scam ads follow users everywhere they go; they might be delivered both – online and offline. They might appear even on popular and reliable websites, such as news portals. So, there’s a huge possibility that users do not suspect anything suspicious because they trust their favourite site.
These ads might trick people in three different ways. They might offer to download software that is capable of protecting and improving computer. Besides, they might warn you to update your security software, because it is outdated. Of course, these ads try to play with your emotions and scare you by telling that the computer is at risk. Moreover, you might receive alerts that some malicious files or programs are detected on your PC, and by clicking the ad, you will be able to learn how to eliminate computer-related programs.
More experienced computer users might realise that these ads might be fraudulent and dangerous. However, the virus is capable of delivering alerts when the computer is not connected to the Internet. So, it’s hard not to believe that notification or pop-up provided by so-called Microsoft service is not real. If you have noticed these kinds of warnings, do not call any provided number, purchase software or get criminals access to your computer.
Removing the virus
To remove Tech Support Scam virus from your computer you have to scan the computer with the strong anti-malware program. Security tools are capable of eliminating the virus and other malware that might have been installed on your PC.
If criminals managed to trick you and you gave them access to your PC, provided bank, credit card or other sensitive information, you should take care of yourself as well. Change all passwords to your bank, social media, and other accounts. Also, contact your bank and inform that you have been scammed and inform necessary institutions about potential identity theft.
Besides, it’s better to take precautions that dealing with the virus. To avoid Tech Support Scam virus you have to be careful online and pay attention to software installation. Download necessary programs from reliable sources and install them using ‘Advanced’ or ‘Custom’ installation mode.
You may remove virus damage with a help of FortectIntego. SpyHunter 5Combo Cleaner and Malwarebytes are recommended to detect potentially unwanted programs and viruses with all their files and registry entries that are related to them.
Getting rid of Tech Support Scam virus. Follow these steps
Uninstall Tech Support Scam in Windows systems
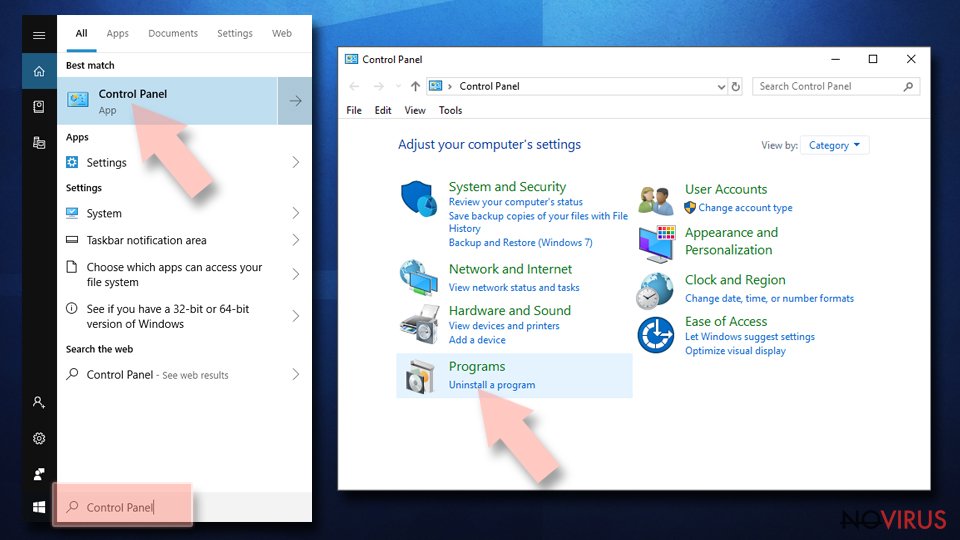
Bear in mind that you won't find a program in the Control Panel labeled as Tech Support virus. The program might be hidden under different names, so it takes time so find it. If you find several suspicious programs, check their credibility online.
Terminate suspicious programs from Windows 10/8 machines by following these instructions:
- Type Control Panel into Windows search and once the result shows up hit Enter.
- Under Programs, choose Uninstall a program.
- Find components related to suspicious programs.
- Right-click on the application and select Uninstall.
- Click Yes when User Account Control shows up.
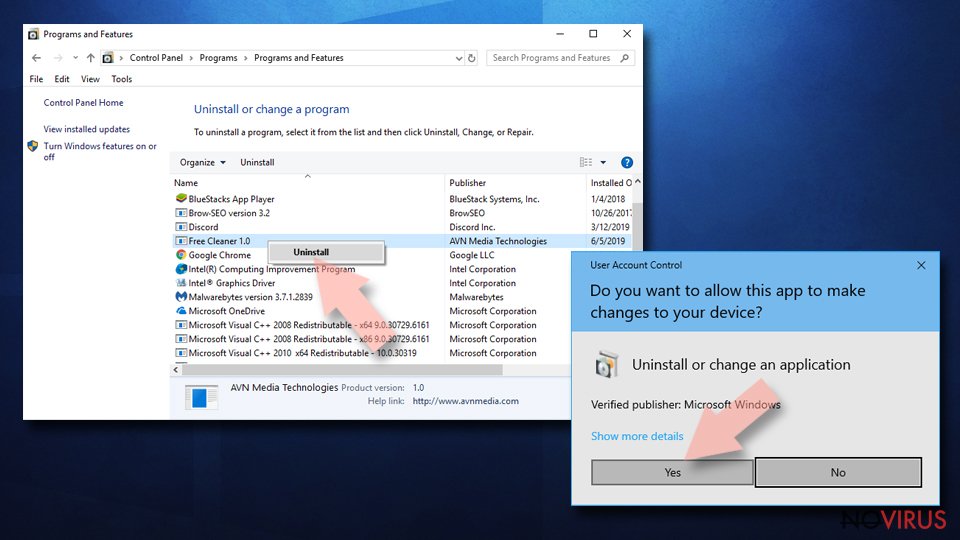
- Wait for the process of uninstallation to be done and click OK.
Windows 7/XP instructions:
- Click on Windows Start and go to Control Panel on the right pane.
- Choose Add/Remove Programs.
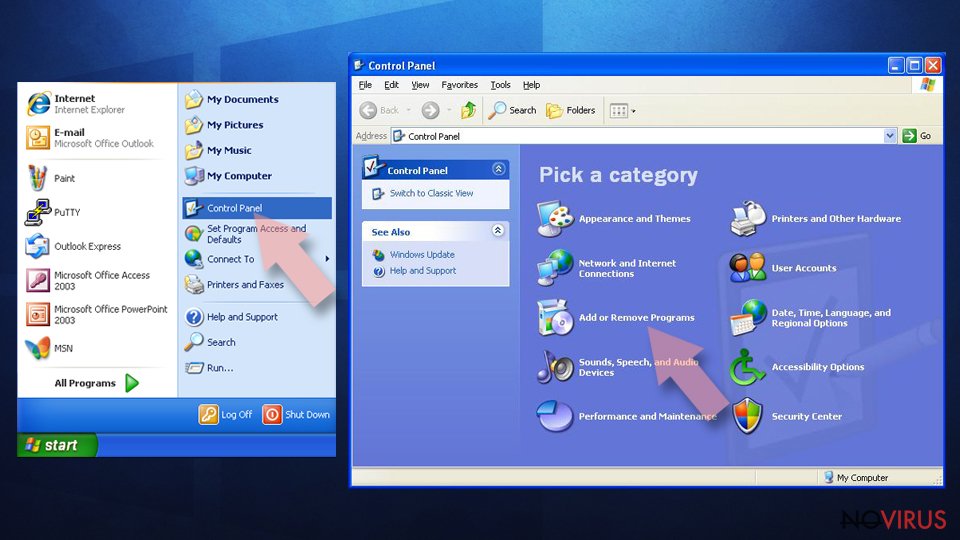
- Select Uninstall a program under Programs in Control Panel.
- Click once on the unwanted application.
- Click Uninstall/Change at the top.
- Confirm with Yes.
- Click OK and finish the removal.
Uninstall Tech Support Scam in Mac OS X system
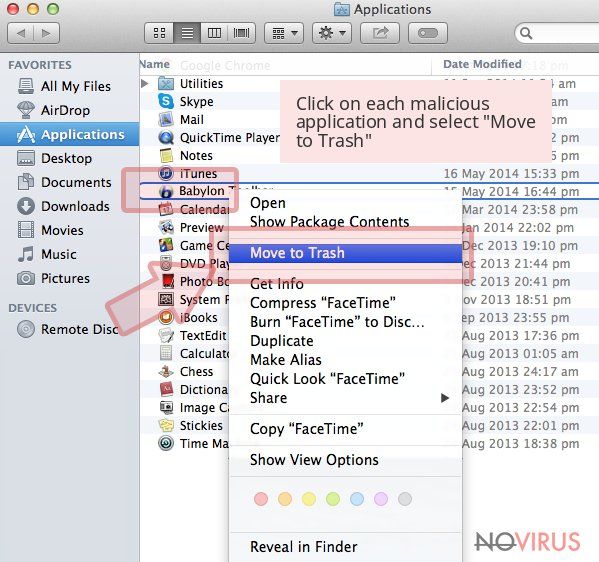
Mostly Tech Support virus targets Windows OS; however, Mac OS X users might encounter the virus too. If you are one of the victims, check the 'Applications' section and look for suspicious programs.
-
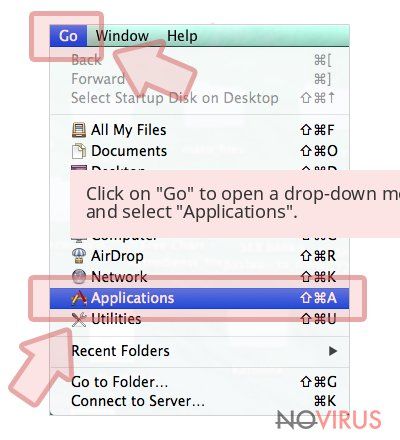
Users who use OS X should click on Go button, which can be found at the top left corner of the screen and select Applications.

-
Wait until you see Applications folder and look for Tech Support Scam or any other suspicious programs on it. Now right click on every of such entries and select Move to Trash.

Delete Tech Support Scam from Mozilla Firefox (FF)
Virus might install various extensions on the Mozilla Firefox that help to deliver misleading ads. Check the list of extensions and uninstall questionable entries.
Remove suspicious Firefox extensions:
- Open Mozilla Firefox browser and click on the three horizontal lines at the top-right to open the menu.
- Select Add-ons in the context menu.
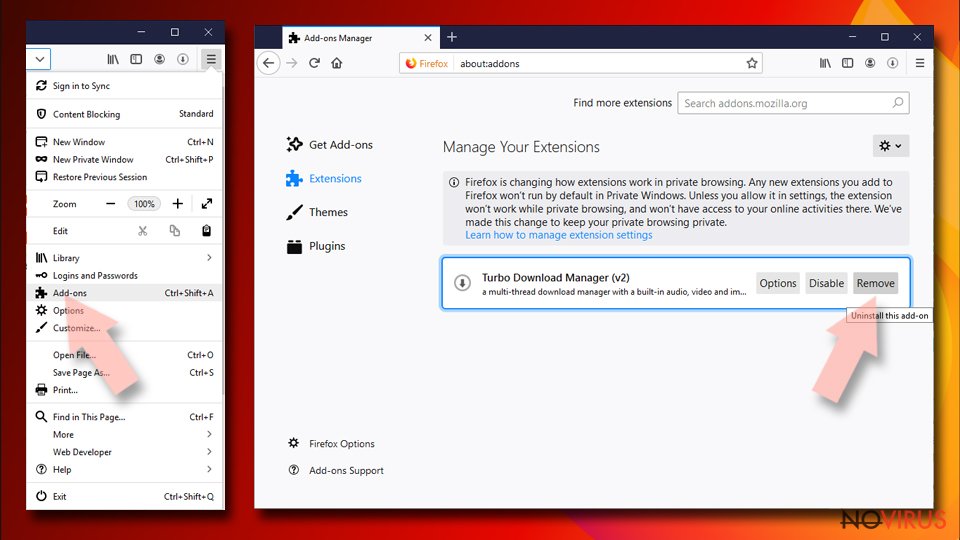
- Choose plugins that are creating issues and select Remove.
Reset the homepage on the browser:
- Click three horizontal lines at the top right corner.
- This time select Options.
- Under Home section, enter your preferred site for the homepage that will open every time you launch Mozilla Firefox.
Clear cookies and site data:
- Click Menu and pick Options.
- Find the Privacy & Security section.
- Scroll down to choose Cookies and Site Data.
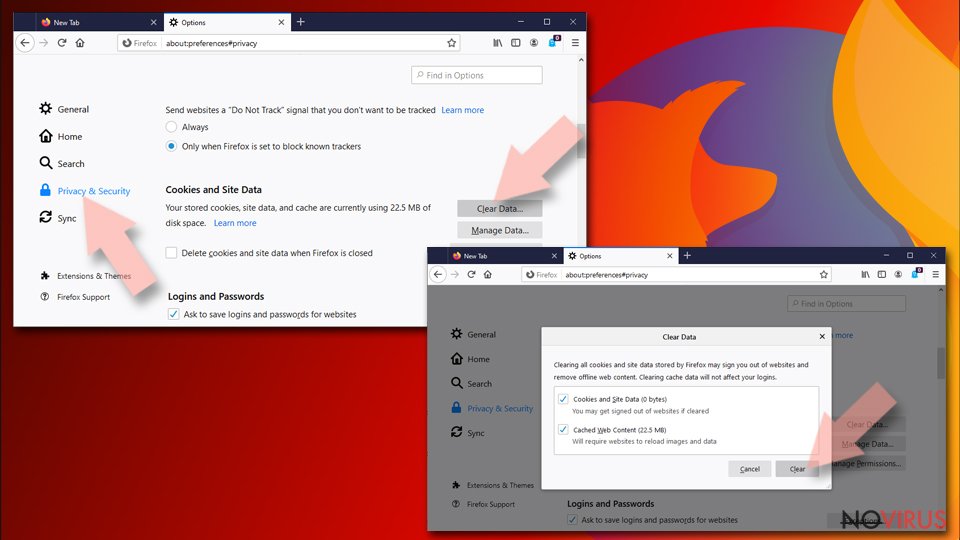
- Click on Clear Data… option.
- Click Cookies and Site Data, Cached Web Content and press Clear.
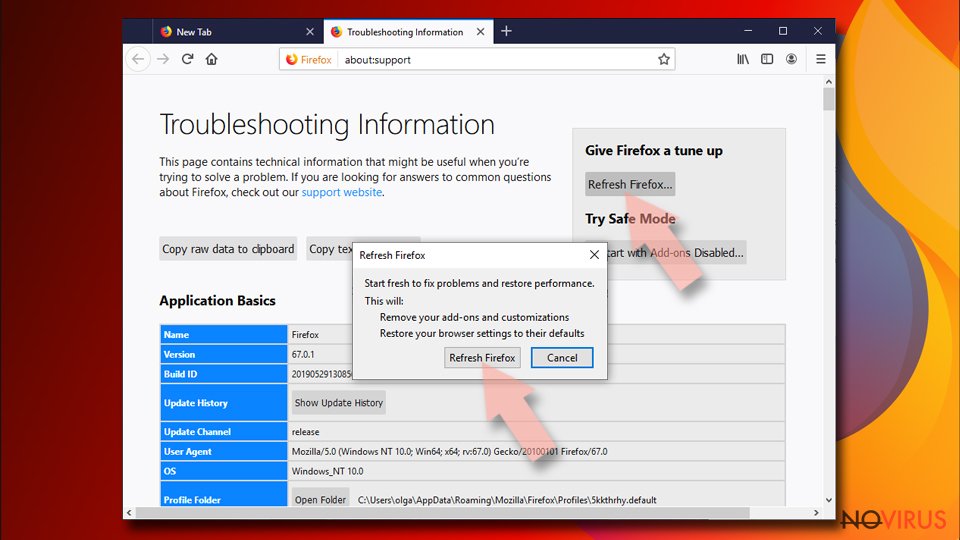
Reset Mozilla Firefox:
If none of the steps above helped you, reset Mozilla Firefox as follows:
- Open Mozilla Firefox and go to the menu.
- Click Help and then choose Troubleshooting Information.
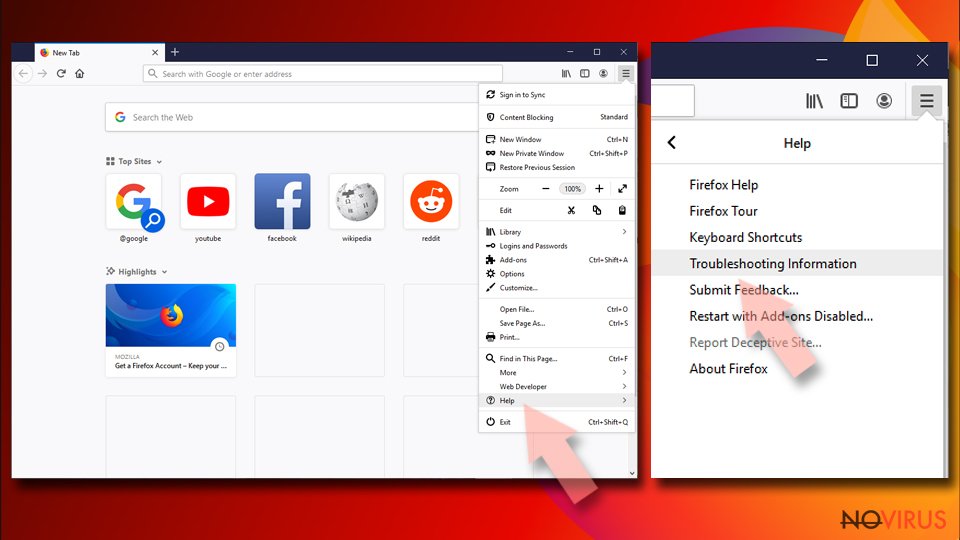
- Locate Give Firefox a tune-up section, click on Refresh Firefox…
- Confirm the action by pressing on Refresh Firefox on the pop-up.
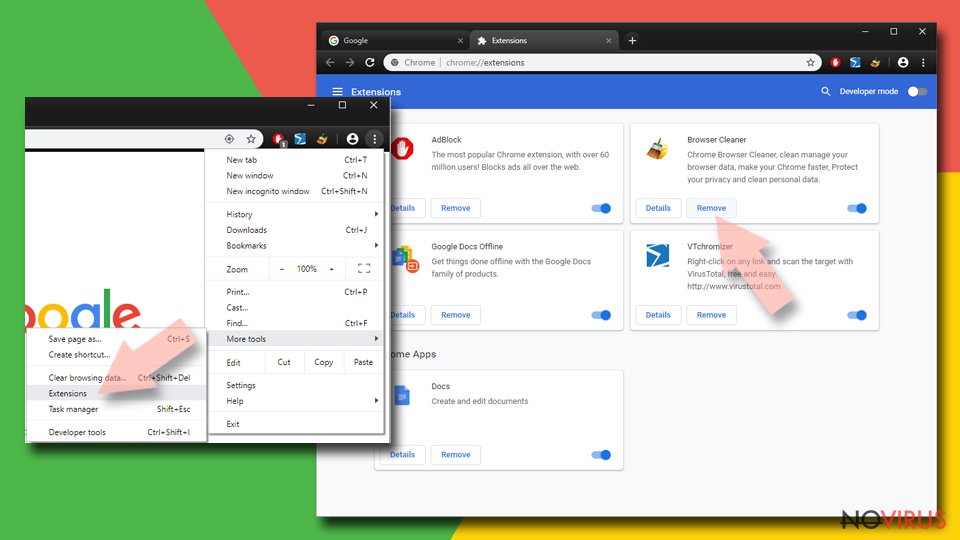
Chrome browser reset
Tech Support virus might have installed various extensions or plugins that help to generate fraudulent warnings. In order to eliminate the virus, you have to detect these extensions and uninstall them.
Find and remove suspicious extensions from Google Chrome:
- In Google Chrome, open the Menu by clicking three vertical dots at the top-right corner.
- Select More tools > Extensions.
- Once the window opens, you will see all the installed extensions.
- Find any suspicious add-ons related to any PUP.
- Uninstall them by clicking Remove.
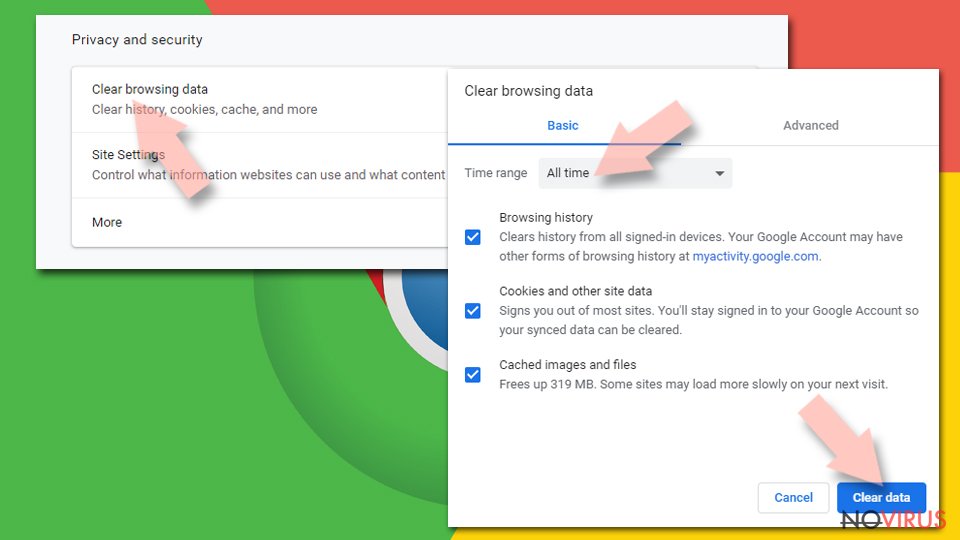
Clear cache and web data from Chrome:
- Click the Menu and select Settings.
- Find Privacy and security section.
- Choose Clear browsing data.
- Select Browsing history.
- Cookies and other site data, also Cached images and files.
- Click Clear data.
Alter settings of the homepage:
- Go to the menu and choose Settings.
- Find odd entries in the On startup section.
- Click on Open a specific or set of pages.
- Then click on three dots and look for the Remove option.
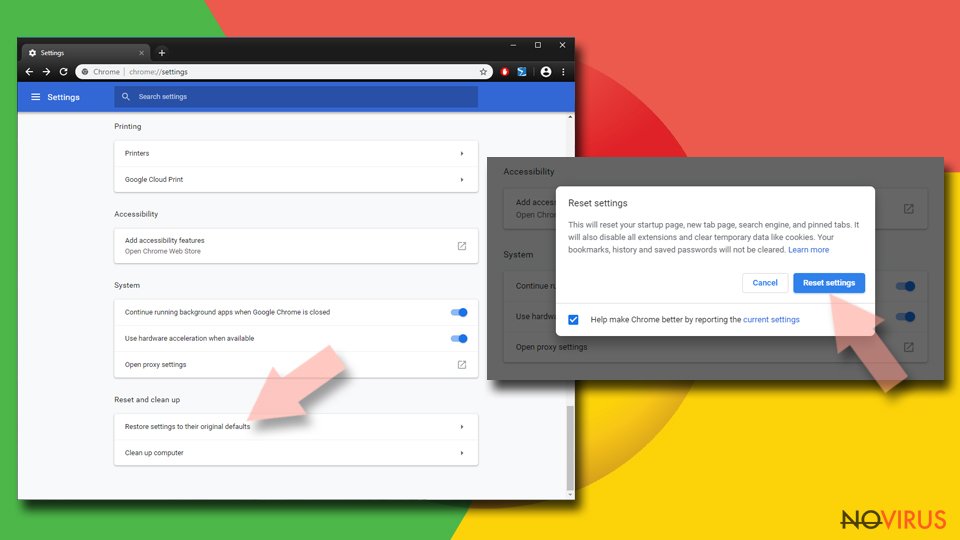
Reset Google Chrome fully:
You might need to reset Google Chrome and properly eliminate all the unwanted components:
- Go to Chrome Settings.
- Once there, scroll down to expand Advanced section.
- Scroll down to choose Reset and clean up.
- Click Restore settings to their original defaults.
- Click Reset settings again.
Delete Tech Support Scam from Safari
It's uncommon that virus targets Mac OS X, but if it has happened, your Safari browser might be infected as well. Chech the list of extensions and uninstall all suspicious extensions.
Get rid of questionable extensions from Safari:
- Click Safari.
- Then go to Preferences…
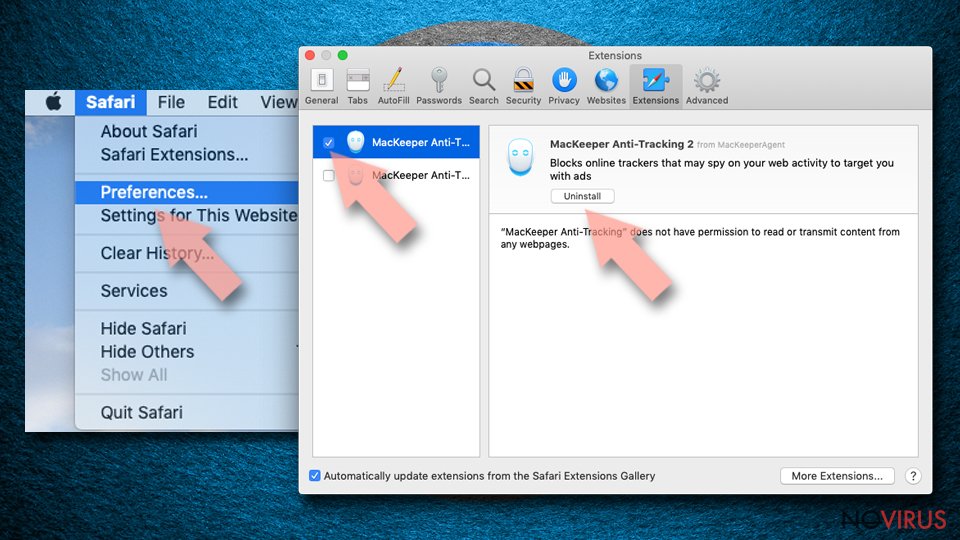
- Choose Extensions on the menu.
- Select the unwanted extension and then pick Uninstall.
Clear cookies from Safari:
- Click Safari.
- Choose Clear History…
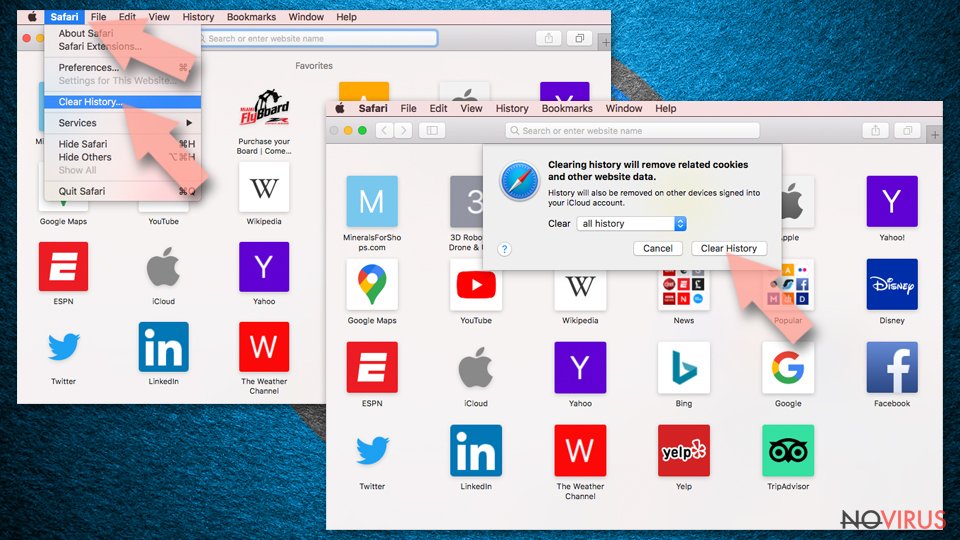
- From the drop-down menu under Clear, find and pick all history.
- Confirm with Clear History.
Reset Safari fully:
- Click Safari and then Preferences…
- Choose the Advanced tab.
- Tick the Show Develop menu in the menu bar.
- From the menu bar, click Develop.
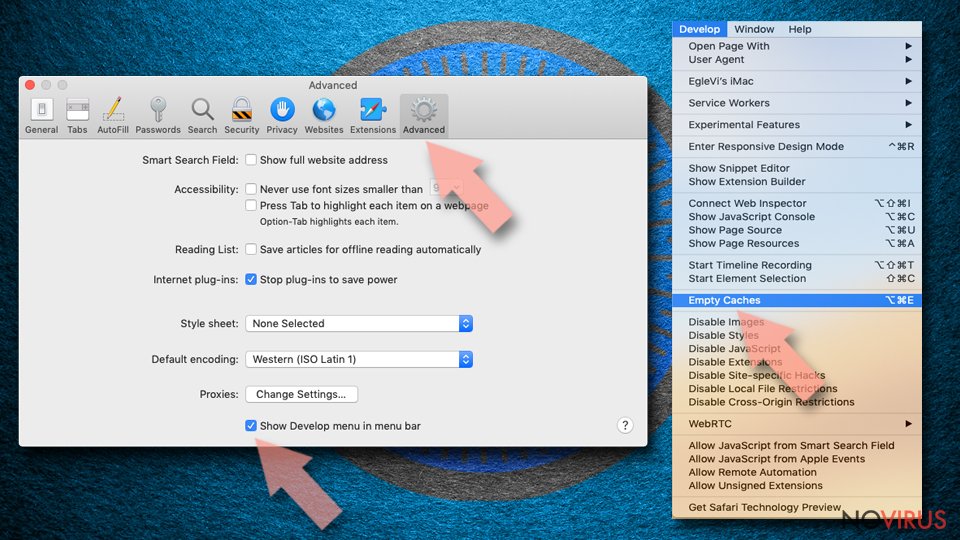
- Then select Empty Caches.
Even if you have completed all the steps above, we still strongly recommend you to scan your computer system with a powerful anti-malware software. It is advisable to do that because an automatic malware removal tool can detect and delete all remains of Tech Support Scam, for instance, its registry keys. The anti-malware program can help you to easily detect and eliminate possibly dangerous software and malicious viruses in an easy way. You can use any of our top-rated malware removal programs: FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes.
How to prevent from getting adware
Securely connect to your website wherever you are
Sometimes you may need to log in to a content management system or server more often, especially if you are actively working on a blog, website, or different project that needs constant maintenance or that requires frequent content updates or other changes. Avoiding this problem can be easy if you choose a dedicated/fixed IP address. It's a static IP address that only belongs to a specific device and does not change when you are in different locations.
VPN service providers such as Private Internet Access can help you with these settings. This tool can help you control your online reputation and successfully manage your projects wherever you are. It is important to prevent different IP addresses from connecting to your website. With a dedicated/fixed IP address, VPN service, and secure access to a content management system, your project will remain secure.
Recover files damaged by a dangerous malware attack
Despite the fact that there are various circumstances that can cause data to be lost on a system, including accidental deletion, the most common reason people lose photos, documents, videos, and other important data is the infection of malware.
Some malicious programs can delete files and prevent the software from running smoothly. However, there is a greater threat from the dangerous viruses that can encrypt documents, system files, and images. Ransomware-type viruses focus on encrypting data and restricting users’ access to files, so you can permanently lose personal data when you download such a virus to your computer.
The ability to unlock encrypted files is very limited, but some programs have a data recovery feature. In some cases, the Data Recovery Pro program can help recover at least some of the data that has been locked by a virus or other cyber infection.