Uninstall Meds virus (Free Removal Guide) - Decryption Methods Included
Meds virus Removal Guide
Description of Meds ransomware
Meds ransomware is the threat that infects the system and encrypts important files to hold them hostage until the demanded ransom is paid
Developers of this Meds ransomware virus offers a discount for the ransom for a while, so people are more trusting and eager to pay for the alleged decryption service. But even though the ransom seems small there is no need to pay for claims that are not real. Cybercriminals only care for their financial gains, not your belongings or files.
| Name | Meds ransomware |
|---|---|
| Symptoms | Files get locked and marked with a particular appendix, system crashes and slowdowns caused by additional processes and added files, programs, disabled applications |
| File marker | .meds |
| Ransom note | _readme.txt |
| Family | Djvu ransomware |
| Distribution | Infected files attached to spam emails |
| Elimination | Remove Meds ransomware from the machine fully with FortectIntego |
Meds ransomware aims to encrypt your files and extort you into paying for the alleged decryption that, in most cases, doesn't even work. So if you decide to pay the ransom, you lose your money and files. There is no need to even consider paying those criminals since they are not trustworthy or even caring for your belongings.
When the computer ends up infected with Meds ransomware, the system becomes especially affected and slow due to additional processes and files the malware adds on the machine. The device gets altered by the threat too, besides all that file locking.
Although your machine gets interfered, Meds ransomware is not affecting the system or programs until the encryption is done. The process runs as a first step of the attack once the script is launched and files like documents, images, videos, audio files, databases, archives get encoded with the help of an army-grade algorithm.
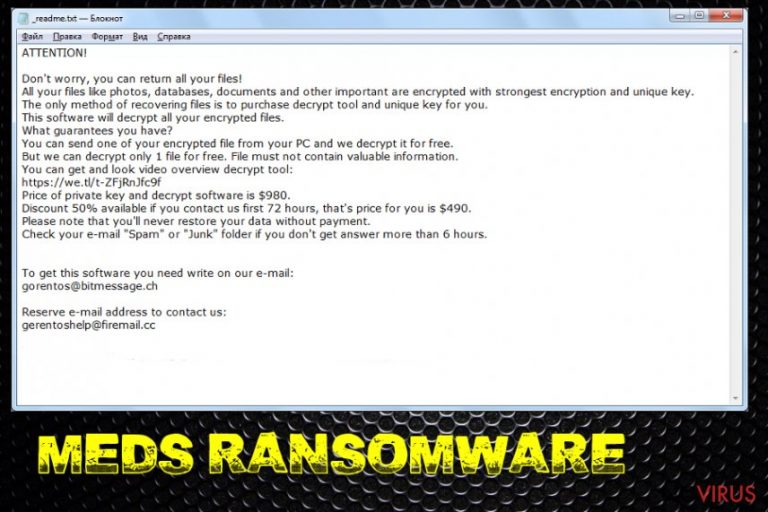
Meds ransomware delivers a ransom-demanding message immediately after the file-locking in a file _readme.txt that reads the following:
ATTENTION!
Don’t worry, you can return all your files!
All your files like photos, databases, documents and other important are encrypted with strongest encryption and unique key.The only method of recovering files is to purchase decrypt tool and unique key for you.
This software will decrypt all your encrypted files.What guarantees you have?
You can send one of your encrypted file from your PC and we decrypt it for free.
But we can decrypt only 1 file for free. File must not contain valuable information.You can get and look video overview decrypt tool:
[link edited]Price of private key and decrypt software is $980.
Discount 50% available if you contact us first 72 hours, that’s price for you is $490.
Please note that you’ll never restore your data without payment.
Check your e-mail “Spam” or “Junk” folder if you don’t get answer more than 6 hours.To get this software you need write on our e- mail:
gorentos@bitmessage.chReserve e-mail address to contact us:
gorentos2@firemail.cc
Our Telegram account:
@datarestoreYour personal ID:
For the proper Meds ransomware removal, you need to choose a program that can detect and delete this malware and other possible threats on the machine, anti-malware programs are designed for such purposes. Remember that detection name for the same virus may differ and there are many databases that AV tools use, so get rid of malware that is indicated by your program after a system scan, don't look for a particular result.
Meds ransomware gets detected as many different threat names, but that doesn't mean anything for the virus eliminations process:
- TR/AD.InstaBot.wrdas;
- Trojan.MalPack.GS;
- Trojan.PSW.Racealer.cu;
- W32/GandCrab.G!tr;
- Trojan.Ransom.Stop;
- Trojan.GenericKD.32424829.
Remove Meds ransomware using the anti-malware of your choice or one of the tools that we offer below, but remember to check the machine for virus damage. You can rely on FortectIntego for that since the program can recover files if needed. Also, go through your file backups only when the machine is virus-free to avoid repetitive encryption.
Ransomware gets downloaded on the system as software or malicious executable
Virus ends up downloaded as fake software or file when the torrent site is used, or cracks get downloaded. However, the more common way of spreading this type of malware is spam email campaigns. The malicious email has attachments in the form of Word or Excel document, often even EXE or PDF format files.
Such attachments pretend to be legitimate invoices, receipts, order notifications and claim that financial information or other sensitive and important details get revealed, so people are more eager to open the email and download the attachment on the computer. You need to avoid downloading such files, opening them on the machine, and enabling suspicious content when asked.
The best tip from us as experts is to delete any suspicious email that gets on your email box and pay attention to other details that may indicate suspicious activities or purposes of the file or senders in general. Clean the email box more often and especially do that with spam email section.
Meds ransomware removal requires additional attention
Meds ransomware virus is the threat that shows up on the machine silently and, until the ransom demanding message is displayed, you cannot notice the infection. However, the device is affected immediately after the infiltration and all your files are encrypted right after the needed changes are started in the background.
To remove Meds ransomware with all the associated files completely, you need a thorough system scan. Choose FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes to run a full check that can indicate all potential issues and malware components. You should never try removing ransomware manually as there is a great danger of removing needed system components.
To know more about how can you repair some Windows files if the threat affected any, watch the video guide below.
Unfortunately, automatic Meds ransomware removal method won't give you the opportunity to recover encrypted data. However, having in mind that STOP decrypter has been actively updated to help people recover after previous versions of DJVU family viruses. Also, make sure you eliminate virus damage from the machine to prevent potential issues in the future.
Getting rid of Meds virus. Follow these steps
In-depth guide for the Meds elimination
Remove Meds ransomware by rebooting the system in Safe Mode with Networking and then running antivirus tool on the computer
Important! →
The elimination guide can appear too difficult if you are not tech-savvy. It requires some knowledge of computer processes since it includes system changes that need to be performed correctly. You need to take steps carefully and follow the guide avoiding any issues created due to improper setting changes. Automatic methods might suit you better if you find the guide too difficult.
Step 1. Launch Safe Mode with Networking
Safe Mode environment offers better results of manual virus removal
Windows 7 / Vista / XP
- Go to Start.
- Choose Shutdown, then Restart, and OK.
- When your computer boots, start pressing the F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) a few times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click the Start button and choose Settings.

- Scroll down to find Update & Security.

- On the left, pick Recovery.
- Scroll to find Advanced Startup section.
- Click Restart now.

- Choose Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.

- Choose 5) Enable Safe Mode with Networking.
Step 2. End questionable processes
You can rely on Windows Task Manager that finds all the random processes in the background. When the intruder is triggering any processes, you can shut them down:
- Press Ctrl + Shift + Esc keys to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes.
- Look for anything suspicious.
- Right-click and select Open file location.

- Go back to the Process tab, right-click and pick End Task.
- Delete the contents of the malicious folder.
Step 3. Check the program in Startup
- Press Ctrl + Shift + Esc on your keyboard again.
- Go to the Startup tab.
- Right-click on the suspicious app and pick Disable.

Step 4. Find and eliminate virus files
Data related to the infection can be hidden in various places. Follow the steps and you can find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive (C: is your main drive by default and is likely to be the one that has malicious files in) you want to clean.
- Scroll through the Files to delete and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Eliminate Meds using System Restore
Use System Restore for Meds virus termination. This feature allows recovering the machine in a previous state when ransomware was not running
-
Step 1: Restart your computer in Safe Mode with Command Prompt
Windows 7 / Vista / XP- Go to Start → Shutdown → Restart → OK.
- As soon as your computer starts, start pressing F8 key repeatedly before the Windows logo shows up.
-
Choose Command Prompt from the list

Windows 10 / Windows 8- Click on the Power button at the Windows login screen, and then press and hold Shift key on your keyboard. Then click Restart.
- Then select Troubleshoot → Advanced options → Startup Settings and click Restart.
-
Once your computer starts, select Enable Safe Mode with Command Prompt from the list of options in Startup Settings.

-
Step 2: Perform a system restore to recover files and settings
-
When the Command Prompt window appears, type in cd restore and press Enter.

-
Then type rstrui.exe and hit Enter..

-
In a new window that shows up, click the Next button and choose a restore point that was created before the infiltration of Meds and then click on the Next button again.


-
To start system restore, click Yes.

-
When the Command Prompt window appears, type in cd restore and press Enter.
Bonus: Restore your files
Using the tutorial provided above you should be able to eliminate Meds from the infected device. novirus.uk team has also prepared an in-depth data recovery guide which you will also find above.There are a couple of methods you can apply to recover data encrypted by Meds:
Data Recovery Pro is the program that helps with encrypted or accidentally deleted files
You can restore files encrypted by Meds ransomware virus or deleted accidentally
- Download Data Recovery Pro;
- Install Data Recovery on your computer following the steps indicated in the software’s Setup;
- Run the program to scan your device for the data encrypted by Meds ransomware;
- Recover the data.
Windows Previous Versions feature can be used as an alternate file recovery method
If you enable System Restore, Windows Previous versions feature can be employed for file recovery
- Right-click on the encrypted document you want to recover;
- Click “Properties” and navigate to “Previous versions” tab;
- In the “Folder versions” section look for the available file copies. Choose the desired version and press “Restore”.
ShadowExplorer is the feature used for data recovery
You can use ShadowExplorer if Meds ransomware left your Shadow Volume Copies untouched
- Download Shadow Explorer (http://shadowexplorer.com/);
- Install Shadow Explorer on your computer following the instructions in the software’s Setup Wizard;
- Run the program. Navigate to the menu on the top-left corner and select a disk containing your encrypted files. Look through the available folders;
- When you find the folder you want to recover, right-click it and select “Export”. Also, choose where the recovered data will be stored.
Decryption tool is not available for Meds ransomware
It is strongly recommended to take precautions and secure your computer from malware attacks. To protect your PC from Meds and other dangerous viruses, you should install and keep a powerful malware removal tool, for instance, FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes.
How to prevent from getting ransomware
A proper web browser and VPN tool can guarantee better safety
As online spying becomes an increasing problem, people are becoming more interested in how to protect their privacy. One way to increase your online security is to choose the most secure and private web browser. But if you want complete anonymity and security when surfing the web, you need Private Internet Access VPN service. This tool successfully reroutes traffic across different servers, so your IP address and location remain protected. It is also important that this tool is based on a strict no-log policy, so no data is collected and cannot be leaked or made available to first or third parties. If you want to feel safe on the internet, a combination of a secure web browser and a Private Internet Access VPN will help you.
Reduce the threat of viruses by backing up your data
Due to their own careless behavior, computer users can suffer various losses caused by cyber infections. Viruses can affect the functionality of the software or directly corrupt data on your system by encrypting it. These problems can disrupt the system and cause you to lose personal data permanently. There is no such threat if you have the latest backups, as you can easily recover lost data and get back to work.
It is recommended to update the backups in parallel each time the system is modified. This way, you will be able to access the latest saved data after an unexpected virus attack or system failure. By having the latest copies of important documents and projects, you will avoid serious inconveniences. File backups are especially useful if malware attacks your system unexpectedly. We recommend using the Data Recovery Pro program to restore the system.







