Remove Koobface (Jan 2020 updated) - Uninstall Guide
Koobface Removal Guide
Description of Koobface
Koobface worm – extremely dangerous virus

Since 2009 Koobface has been known as computer worm that spreads on social networks and tries to steal private users’ information. Malware attacks have been spotted on Facebook, Twitter, MySpace, Skype, Yahoo messenger and even Gmail, Yahoo and AOL mailing. Usually, computer infections target only Windows OS users; however, this cyber threat can affect Mac OS X and Linux as well. Koobface malware tries to trick users to install fake Flash Update that is necessary to watch a particular video. Victims receive the video link on direct message on the social network, and if they click on it, they are redirected to a dangerous website which asks to install updates. This bogus update hides Koobface virus which has been created to steal personal and private computer users’ information. Indeed, malware is a serious threat to your credit card and banking credentials, information published on social media and so on. During its lifetime, the developers of the malware have already earned thousands of dollars.
On the affected computer malware checks browser’s cookies and looks for cookies that are related to social media. If malware finds them, it activates itself, steals login information and spreads a malicious message to the entire social media friend list. If Koobface worm got in the ‘wrong computer’ that owner does not use or is inactive social media user, it deletes itself and delivers a fake pop-up message informing about particular codec error and asks to contact the service.
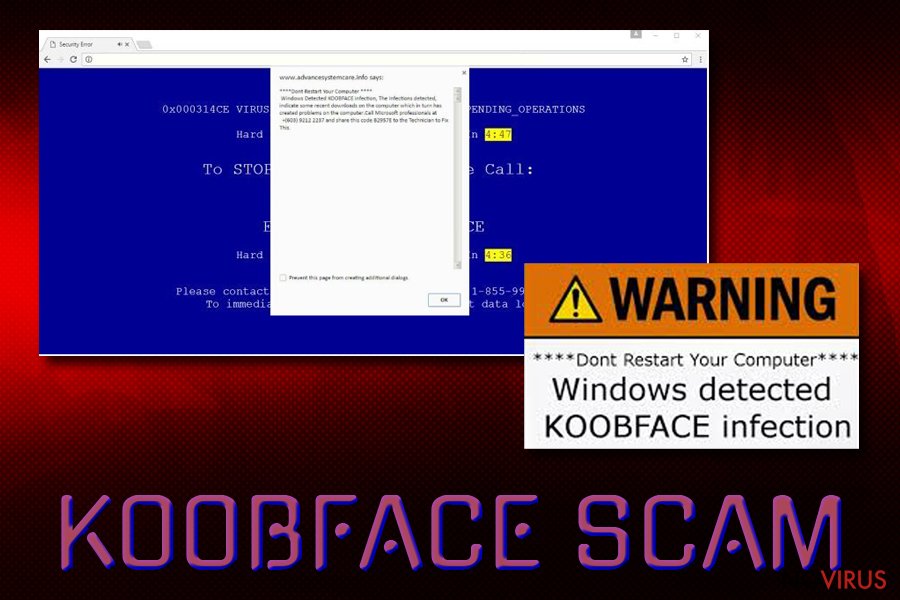
Indeed, Koobface virus can provide lots of misleading advertisements that warns about various computer-related issues, offers software installation or updates. However, these notifications, ads, and warnings are just Tech support scam. If you click on them or even decide to contact cyber criminals, you may be tricked into installing software or giving criminals full access to your computer to solve a particular issue. However, these warnings are an actual sign of computer infection, and you should not ignore them. Keep in mind that it’s crucial to remove Koobface immediately because keeping in on PC may lead to the money loss.

Some cyber criminals use Koobface name in order to scare computer users and swindle their money. Some tech support scammers deliver a pop-up message that computer has been infected with Koobface. To remove it from the system and protect the computer, the user has to call provided numbers. Keep in mind that calling suspicious numbers is not a wise decision. Crooks may trick you into purchasing or installing questionable software and cause more problems for you. They might also convince you to install remote control tools and give full access to your PC for them. If you see suspicious warnings about various computer-related issues, instead of calling to the shady help services, run a full system scan with strong and professional anti-malware application. However, if you do not have it, we recommend installing FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes. These programs are capable of detecting and eliminating malware. Within several minutes Koobface removal will be over.
Koobface distribution and how to avoid it
As we already mentioned Koobface, malware spreads via social media messages and fake video player. Social media users receive an infected video link from a friend which redirects them to the suspicious website, where they are asked to install Flash Updates. If users are curious and have no idea about safe ways to update programs and allows installing fake updates, they let malware inside the computer.
It’s not hard to recognise infected link from the safe one. The dangerous link usually has various symbols, letters or numbers and the domain looks unfamiliar. If the link looks strange or suspicious, do not open it. Victims claim that in the message their ‘friend’ told that they are in this video and encouraged them to watch it as well. Indeed, you can be easily tricked to open the link if you are close to the sender; otherwise, you should think before opening it. It’s doubtful that your colleague or old classmate whom you haven’t talked in ages will send you a funny video.
The only possible way to avoid Koobface virus is to stay away from unreliable and high-risk websites and do not click on any suspicious links or advertisements that you see online. Bear in mind that some viral videos on social may also include malicious content. Do not open any links and videos sent from your friends that look suspicious. Before opening it, double check the information and ask your friend if this link is really safe to open. If you end up on the website that asks to update Flash or install other applications, leave it immediately. Remember, that reliable updates do not show up as pop-ups or ads. Lastly, protecting your computer with strong antivirus program will also help to avoid malware.
Koobface removal options
The best way to remove Koobface is to employ a strong malware removal tool. We recommend choosing FortectIntego or SpyHunter 5Combo Cleaner because these programs have been created to detect and eliminate malicious files. Install and update the program and run a full system scan. After a couple of minutes, it will remove this annoying computer infection.
If you are not sure if your computer has been infected with Koobface or not, open Windows Task Manager and look for these processes: Ld12.exe, freddy79.exe, mstre6.exe, fbtre6.exe, ld08.exe. After Koobface removal, don’t forget to change all your passwords, just to be sure that cyber criminals do not have access to your accounts.
Getting rid of Koobface. Follow these steps
In-depth guide for the Koobface elimination
Reboot your computer in Safe Mode with Networking. Then employ a professional anti-malware program and run a full system scan. The program will find and delete Koobface Trojan and other malicious components. Keep in mind that it's important to delete all malware-related components in order to avoid attacks in the future. For this reason, we do not recommend removing this worm manually.
Important! →
The elimination guide can appear too difficult if you are not tech-savvy. It requires some knowledge of computer processes since it includes system changes that need to be performed correctly. You need to take steps carefully and follow the guide avoiding any issues created due to improper setting changes. Automatic methods might suit you better if you find the guide too difficult.
Step 1. Launch Safe Mode with Networking
Safe Mode environment offers better results of manual virus removal
Windows 7 / Vista / XP
- Go to Start.
- Choose Shutdown, then Restart, and OK.
- When your computer boots, start pressing the F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) a few times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click the Start button and choose Settings.

- Scroll down to find Update & Security.

- On the left, pick Recovery.
- Scroll to find Advanced Startup section.
- Click Restart now.

- Choose Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.

- Choose 5) Enable Safe Mode with Networking.
Step 2. End questionable processes
You can rely on Windows Task Manager that finds all the random processes in the background. When the intruder is triggering any processes, you can shut them down:
- Press Ctrl + Shift + Esc keys to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes.
- Look for anything suspicious.
- Right-click and select Open file location.

- Go back to the Process tab, right-click and pick End Task.
- Delete the contents of the malicious folder.
Step 3. Check the program in Startup
- Press Ctrl + Shift + Esc on your keyboard again.
- Go to the Startup tab.
- Right-click on the suspicious app and pick Disable.

Step 4. Find and eliminate virus files
Data related to the infection can be hidden in various places. Follow the steps and you can find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive (C: is your main drive by default and is likely to be the one that has malicious files in) you want to clean.
- Scroll through the Files to delete and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Eliminate Koobface using System Restore
-
Step 1: Restart your computer in Safe Mode with Command Prompt
Windows 7 / Vista / XP- Go to Start → Shutdown → Restart → OK.
- As soon as your computer starts, start pressing F8 key repeatedly before the Windows logo shows up.
-
Choose Command Prompt from the list

Windows 10 / Windows 8- Click on the Power button at the Windows login screen, and then press and hold Shift key on your keyboard. Then click Restart.
- Then select Troubleshoot → Advanced options → Startup Settings and click Restart.
-
Once your computer starts, select Enable Safe Mode with Command Prompt from the list of options in Startup Settings.

-
Step 2: Perform a system restore to recover files and settings
-
When the Command Prompt window appears, type in cd restore and press Enter.

-
Then type rstrui.exe and hit Enter..

-
In a new window that shows up, click the Next button and choose a restore point that was created before the infiltration of Koobface and then click on the Next button again.


-
To start system restore, click Yes.

-
When the Command Prompt window appears, type in cd restore and press Enter.
It is strongly recommended to take precautions and secure your computer from malware attacks. To protect your PC from Koobface and other dangerous viruses, you should install and keep a powerful malware removal tool, for instance, FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes.
How to prevent from getting worms
Securely connect to your website wherever you are
Sometimes you may need to log in to a content management system or server more often, especially if you are actively working on a blog, website, or different project that needs constant maintenance or that requires frequent content updates or other changes. Avoiding this problem can be easy if you choose a dedicated/fixed IP address. It's a static IP address that only belongs to a specific device and does not change when you are in different locations.
VPN service providers such as Private Internet Access can help you with these settings. This tool can help you control your online reputation and successfully manage your projects wherever you are. It is important to prevent different IP addresses from connecting to your website. With a dedicated/fixed IP address, VPN service, and secure access to a content management system, your project will remain secure.
Recover files damaged by a dangerous malware attack
Despite the fact that there are various circumstances that can cause data to be lost on a system, including accidental deletion, the most common reason people lose photos, documents, videos, and other important data is the infection of malware.
Some malicious programs can delete files and prevent the software from running smoothly. However, there is a greater threat from the dangerous viruses that can encrypt documents, system files, and images. Ransomware-type viruses focus on encrypting data and restricting users’ access to files, so you can permanently lose personal data when you download such a virus to your computer.
The ability to unlock encrypted files is very limited, but some programs have a data recovery feature. In some cases, the Data Recovery Pro program can help recover at least some of the data that has been locked by a virus or other cyber infection.







