Uninstall Instagram virus (Virus Removal Tutorial) - Jul 2019 updated
Instagram virus Removal Guide
Description of Instagram malware
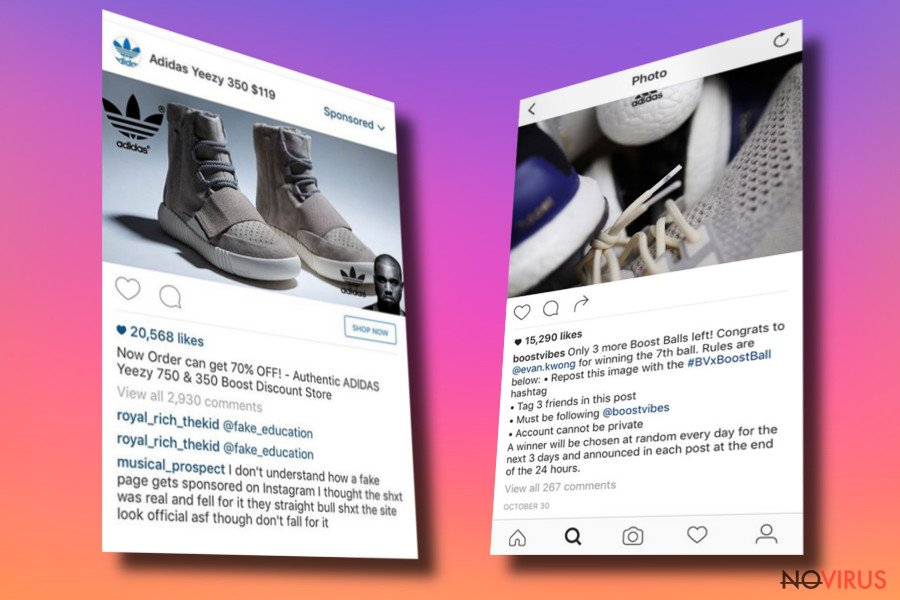
Versions of Instagram virus

The Instagram virus is another proof that cyber criminals try new methods and places to do illegal activities. Social media plays more and more important role in our daily lives, so, it’s no surprise that cyber criminals try to be the part of it. Instagram users probably have noticed several versions of the virus, such as The Ugly List 2016 scam, Instagram followers virus and Who Viewed Your Instagram Profile virus.
The crooks try to get user’s login information and might post on behalf of the victim. In this way, the virus spreads and cause chaos on this platform. Cyber criminals have already launched several malware distribution campaigns on Facebook[1] and Skype; therefore, there’s no doubt that after the success, they try new social media platforms for their illegal activities. However, if your account has been hacked, you should scan your smartphone or mobile device with FortectIntego or SpyHunter 5Combo Cleaner and initiate Instagram virus removal. At the end of the article you will find detailed instructions on virus elimination, please follow them carefully.

Who Viewed Your Instagram Profile virus
Many social media users are interested in who viewed their profiles and cybercriminals try to convince naïve and curious users that it’s possible. However, at the moment Instagram does not have this function, so all these apps that are on Google Play and App Store are fraudulent.[2]
If you have been interested in who has stalked your Instagram, probably, you have seen or even tried applications such as ‘InstaCare – Who cares with me?’ and ‘Who Viewed Me on Instagram?’ Sadly, the developer Turkyer Bayram is known for creating ‘InstaAgent’[3] application which has been used for stealing users’ credentials. Apart from that, this version of the Instagram virus can post lots of spam.
Instagram followers virus
The young generation dreams about getting more followers and becoming famous on this social platform. The developers of this malware can make this dream come true; however, the new followers are nothing more than zombies. This version of the malware is closely related to the Zeus virus which has been created for stealing credit cards’ information.[4]
This time malware hacks the Instagram account, steals credentials, starts following random profiles, liking posts and posting spam. Therefore, if you noticed this activity on your account, you should report about it to Instagram directly, change the password and start virus elimination.
The Ugly List 2016 scam
This one of the latest versions of the Instagram virus which has shown up in the middle of 2016. Users might receive a message or a comment from the random person, a follower or the person they follow that they have been added to the ‘Instagram Ugly List.'
Keep in mind that this message has been sent from the compromised account and usually includes the link. It’s important to stay away from this link because it leads to the malicious website where users can lose their login information. As soon as malware hacks the account, it starts spreading malware further. If you notice the symptoms of this infection, you should report about it to Instagram, change your password and clean the device.[5]

How does malware spread on Instagram?
All variants of Instagram malware spread via spam messages, comments, and tags. The majority of this platform users have been tagged in the suspicious picture or received spam comments suggesting to click the link and get more followers. Keep in mind that all these offers are not real and have a shady purpose of stealing your login details.
For those who dream about popularity on Instagram, we can recommend focusing on making great pictures, using relevant tags and growing the audience naturally. If you want to protect your account and avoid this annoying malware, you should stay away from these links and do not click them no matter how great the offers they provide. The applications that offer to see who viewed your profile are generally created for getting your login credentials and hacking your account. Bear in mind that Instagram does not have this function, so all these programs are shady and not worth trusting.
Getting rid of the Instagram virus
If you notice strange activities on your Instagram account, we recommend scanning the device with a mobile version of FortectIntego or SpyHunter 5Combo Cleaner. Using one of the anti-malware/anti-spyware tools you will start the Instagram virus removal process. Apart from scanning the device you should also login to your Instagram using the Web browser and then, revoke and block all suspicious applications:
- On your profile click on Edit Profile and then Authorized Applications.
- Look through the list of apps that have access to the account. When you find some suspicious programs, click on Revoke Access button, then Yes and a confirmation notification.
Once you’ve done it, change your password. However, if you cannot access your profile and remove Instagram virus, contact the Instagram directly. We also recommend reporting all compromised accounts to keep this social platform clean.
How to prevent from getting malware
Securely connect to your website wherever you are
Sometimes you may need to log in to a content management system or server more often, especially if you are actively working on a blog, website, or different project that needs constant maintenance or that requires frequent content updates or other changes. Avoiding this problem can be easy if you choose a dedicated/fixed IP address. It's a static IP address that only belongs to a specific device and does not change when you are in different locations.
VPN service providers such as Private Internet Access can help you with these settings. This tool can help you control your online reputation and successfully manage your projects wherever you are. It is important to prevent different IP addresses from connecting to your website. With a dedicated/fixed IP address, VPN service, and secure access to a content management system, your project will remain secure.
Recover files damaged by a dangerous malware attack
Despite the fact that there are various circumstances that can cause data to be lost on a system, including accidental deletion, the most common reason people lose photos, documents, videos, and other important data is the infection of malware.
Some malicious programs can delete files and prevent the software from running smoothly. However, there is a greater threat from the dangerous viruses that can encrypt documents, system files, and images. Ransomware-type viruses focus on encrypting data and restricting users’ access to files, so you can permanently lose personal data when you download such a virus to your computer.
The ability to unlock encrypted files is very limited, but some programs have a data recovery feature. In some cases, the Data Recovery Pro program can help recover at least some of the data that has been locked by a virus or other cyber infection.
- ^ Locky ransomware goes on Facebook: malware started spreading via instant messages. Esolutions.lt The blog about latest virus infections.
- ^ Swati Khandelwal. Who Viewed Your Profile on Instagram? Obviously, Hackers!. The Hacker News. Security in a serious way.
- ^ Juli Clover. Password-Stealing Instagram App 'InstaAgent' Reappears in App Store Under New Name. MacRumors. News and rumors you care about.
- ^ Kurt Wagner. This Virus Creates Fake Followers on Instagram. Mashable. The website about social media, marketing, technologies and other news.
- ^ Cammy Haribson. Is Instagram 'Ugly List 2016' Real? Hack Scams Users Into Thinking They’ve Been Tagged, Then Takes Over Their Accounts. iDigitalTimes. Digital Technology News, Latest Technology News.
