Uninstall Gandcrab 5.1 virus (Virus Removal Tutorial) - Jan 2019 updated
Gandcrab 5.1 virus Removal Guide
Description of Gandcrab 5.1 ransomware
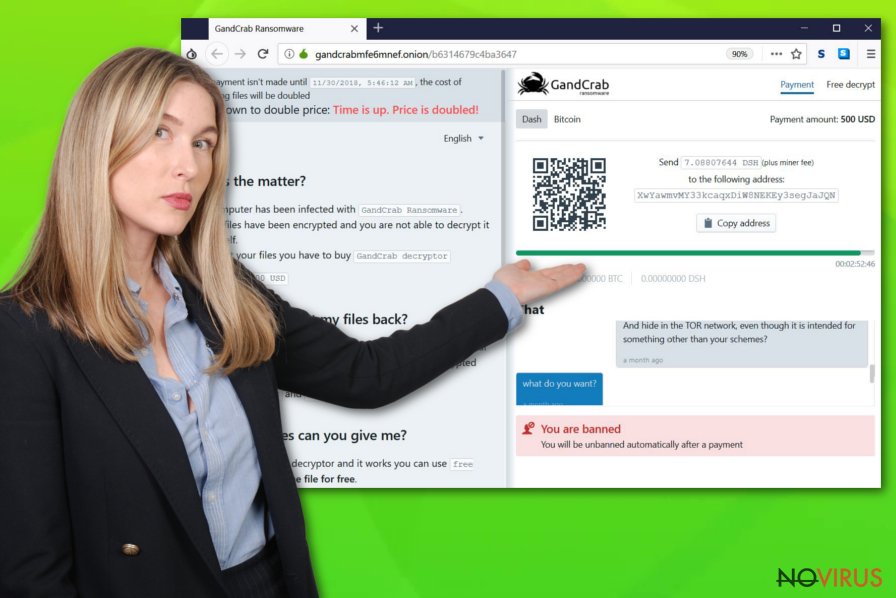
Gandcrab 5.1 ransomware – a dangerous cyber threat that prevents users from accessing their files until a ransom is paid

Gandcrab 5.1 ransomware is one of the newest variants of the notorious virus that locks up data and requires to pay a ransom of $1,200 – $2,400 in Bitcoin or Dash to recover access to pictures, videos, music, documents, databases and other files. This particular malware strain has been one of the most prolific culprits, infecting thousands of users around the world by spreading using exploit kits (such as Fallout), unprotected RDP, spam emails, and other methods. Once installed, Gandcrab 5.1 virus performs several system modifications, then uses Salsa20 for encryption to append a random string as a file extension. [victim’s_ID]-DECRYPT.txt is dropped on the desktop, and the wallpaper swapped to a brief message, explaining the situation to the victim. Unfortunately, Gandcrab 5.1 ransomware is not yet decryptable, although experts are continually working on decryption tools.
| Name | Gandcrab 5.1 |
| Type | Ransomware |
| Parent virus | GandCrab v5 |
| Cipher | Salsa20 |
| File extension | Random string |
| Ransom size | $1,200-2,400 in BTC or DASH |
| Distribution | Exploit kits, repacked installers, spam emails, unprotected RDP, etc. |
| Elimination | Use software that can detect the threat – FortectIntego, SpyHunter 5Combo Cleaner or other engines |
Gandcrab 5.1 ransomware is widely spread around the world and does not target specific regions. Therefore, the possibility to get infected is quite high for those who are careless when using the internet. If that is the case, you should use this guide to remove Gandcrab 5.1 ransomware completely.
Once the malicious payload is executed, Gandcrab 5.1 virus will remove Shadow Volume Copies, modify Windows registry to launch with every system start and make other changes. File encryption follows straight away, and victims can notice within seconds that something is wrong.
Most of the data located on the system becomes encrypted, i.e., unusable. Therefore, a file like picture.jpg would be turned into something like picture.jpg.BujySh. The key to locked data is sent to a remote server that is controlled by Gandcrab 5.1 ransomware authors. The short warning on the wallpaper claims:
ENCRYPTED BY GANDCRAB 5.1
DEAR [USER],
YOUR FILES ARE UNDER STRONG PROTECTION BY OUR SOFTWARE.
IN ORDER TO RESTORE IT YOU MUST BUY DECRYPTOR
For further steps read BUJYSH-DECRYPT.html that is located in every encrypted folder.
Experts do not advise users contacting cybercriminals because there is a high chance of being scammed. Additionally, this motion would prove to malicious actors that Gandcrab 5.1 ransomware works and will attempt to develop and improve the virus further. Unfortunately, that is precisely what seems to be happening with the virus family, as new variants are coming out faster than researchers manage to create decryptors.
Thus, better take care of Gandcrab 5.1 ransomware removal first (we suggest using security software like FortectIntego, SpyHunter 5Combo Cleaner or other tools that can detect this version) and then proceed with file recovery. Check the guide for the process at the end of the article.
Stay away from risky activities online and protect your PC from infections
Ransomware is one of the biggest cyber threats currently. It is continually being evolved and even collaborates with other threats, such as data-stealers, crypto-miners, backdoors, and similar. Furthermore, the malicious software may result in data and money loss. Therefore, users should avoid this dangerous encounter at all costs.
To prevent malware’s entry, users should rely on security expert’s advice:
- Security software is the key when it comes to protecting your device. Download anti-virus software and keep it up to date, as well as the real-time protection enabled;
- Stay away from spam emails. Phishing emails and spoofing sites are notorious for delivering ransomware infections. Malicious messages usually come with an attachment that hides the payload, or a link that redirects to the host site;
- Enable applications and services that would reduce the risk of infection: ad-block, VPN, password manager, etc.;
- Patch your system and programs as soon as updates are available. Be aware that most professional viruses are distributed with the help of exploits and vulnerabilities;
- Avoid using torrent and similar file-sharing sites;
- Scan downloaded installers and other files with such tools like Virus Total.
Finally, we suggest you backup your files regularly on an external drive or a virtual machine.
Remove Gandcrab 5.1 ransomware with the help of reputable security software
Gandcrab 5.1 ransomware removal should be executed as soon as possible. For that, you should use anti-malware software. If you do not have such a tool installed (which is highly likely), you should download one from trusted vendors. You should also be aware that not all AV engines are capable of Gandcrab 5.1 virus elimination, as they use different databases. In such a case, download a separate application and scan the device again.
Once you remove Gandcrab 5.1 ransomware thoroughly, you can attempt file recovery. Unfortunately, there is no official decryptor available for this version. However, numerous tools were created in the past, and security researchers are continually working on cracking the new versions of this malware string. As of now, you can try our decryption solutions below – these are third-party tools that might be able to return at least some of your data. Note: make a copy of all your files before proceeding.
Getting rid of Gandcrab 5.1 virus. Follow these steps
In-depth guide for the Gandcrab 5.1 elimination
To remove Gandcrab 5.1 safely, use Safe Mode with Networking:
Important! →
The elimination guide can appear too difficult if you are not tech-savvy. It requires some knowledge of computer processes since it includes system changes that need to be performed correctly. You need to take steps carefully and follow the guide avoiding any issues created due to improper setting changes. Automatic methods might suit you better if you find the guide too difficult.
Step 1. Launch Safe Mode with Networking
Safe Mode environment offers better results of manual virus removal
Windows 7 / Vista / XP
- Go to Start.
- Choose Shutdown, then Restart, and OK.
- When your computer boots, start pressing the F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) a few times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click the Start button and choose Settings.

- Scroll down to find Update & Security.

- On the left, pick Recovery.
- Scroll to find Advanced Startup section.
- Click Restart now.

- Choose Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.

- Choose 5) Enable Safe Mode with Networking.
Step 2. End questionable processes
You can rely on Windows Task Manager that finds all the random processes in the background. When the intruder is triggering any processes, you can shut them down:
- Press Ctrl + Shift + Esc keys to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes.
- Look for anything suspicious.
- Right-click and select Open file location.

- Go back to the Process tab, right-click and pick End Task.
- Delete the contents of the malicious folder.
Step 3. Check the program in Startup
- Press Ctrl + Shift + Esc on your keyboard again.
- Go to the Startup tab.
- Right-click on the suspicious app and pick Disable.

Step 4. Find and eliminate virus files
Data related to the infection can be hidden in various places. Follow the steps and you can find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive (C: is your main drive by default and is likely to be the one that has malicious files in) you want to clean.
- Scroll through the Files to delete and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Eliminate Gandcrab 5.1 using System Restore
System Restore can also be used as a solution for ransomware’s removal:
-
Step 1: Restart your computer in Safe Mode with Command Prompt
Windows 7 / Vista / XP- Go to Start → Shutdown → Restart → OK.
- As soon as your computer starts, start pressing F8 key repeatedly before the Windows logo shows up.
-
Choose Command Prompt from the list

Windows 10 / Windows 8- Click on the Power button at the Windows login screen, and then press and hold Shift key on your keyboard. Then click Restart.
- Then select Troubleshoot → Advanced options → Startup Settings and click Restart.
-
Once your computer starts, select Enable Safe Mode with Command Prompt from the list of options in Startup Settings.

-
Step 2: Perform a system restore to recover files and settings
-
When the Command Prompt window appears, type in cd restore and press Enter.

-
Then type rstrui.exe and hit Enter..

-
In a new window that shows up, click the Next button and choose a restore point that was created before the infiltration of Gandcrab 5.1 and then click on the Next button again.


-
To start system restore, click Yes.

-
When the Command Prompt window appears, type in cd restore and press Enter.
Bonus: Restore your files
Using the tutorial provided above you should be able to eliminate Gandcrab 5.1 from the infected device. novirus.uk team has also prepared an in-depth data recovery guide which you will also find above.There are a couple of methods you can apply to recover data encrypted by Gandcrab 5.1:
Data Recovery Pro might help you recover your data
This application is a professional tool that might help you with file recovery affected by Gandcrab 5.1.
- Download Data Recovery Pro;
- Install Data Recovery on your computer following the steps indicated in the software’s Setup;
- Run the program to scan your device for the data encrypted by Gandcrab 5.1 ransomware;
- Recover the data.
Make use of Windows Previous Versions feature to recover separate files
This method will prove to be effective for separate files as long as you did enable System Restore before malware attack occurred.
- Right-click on the encrypted document you want to recover;
- Click “Properties” and navigate to “Previous versions” tab;
- In the “Folder versions” section look for the available file copies. Choose the desired version and press “Restore”.
Take advantage of ShadowExplorer – it can recover all of your files under certain conditions
If the virus failed to eliminate Shadow Volume Copies, this software would get all your data back.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Install Shadow Explorer on your computer following the instructions in the software’s Setup Wizard;
- Run the program. Navigate to the menu on the top-left corner and select a disk containing your encrypted files. Look through the available folders;
- When you find the folder you want to recover, right-click it and select “Export”. Also, choose where the recovered data will be stored.
No decryptor is available
It is strongly recommended to take precautions and secure your computer from malware attacks. To protect your PC from Gandcrab 5.1 and other dangerous viruses, you should install and keep a powerful malware removal tool, for instance, FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes.
How to prevent from getting ransomware
Prevent the government from spying on you
As there is a growing debate in government about collecting users' data and spying on citizens, you should take a closer look at this issue and find out what shady ways of gathering information can be used to collect information about you. You need to browse anonymously if you want to avoid any government-initiated spying and tracking of information.
You can enjoy secure internet browsing and minimize the risk of intrusion into your system if you use Private Internet Access VPN program. This VPN application creates a virtual private network and provides access to the required data without any content restrictions.
Control government and other third party access to your data and ensure safe web browsing. Even if you do not engage in illegal activities and trust your ISP, we recommend being careful about your security. You should take extra precautions and start using a VPN program.
Recover files damaged by a dangerous malware attack
Despite the fact that there are various circumstances that can cause data to be lost on a system, including accidental deletion, the most common reason people lose photos, documents, videos, and other important data is the infection of malware.
Some malicious programs can delete files and prevent the software from running smoothly. However, there is a greater threat from the dangerous viruses that can encrypt documents, system files, and images. Ransomware-type viruses focus on encrypting data and restricting users’ access to files, so you can permanently lose personal data when you download such a virus to your computer.
The ability to unlock encrypted files is very limited, but some programs have a data recovery feature. In some cases, the Data Recovery Pro program can help recover at least some of the data that has been locked by a virus or other cyber infection.







