Uninstall Crypted virus (Improved Removal Guide) - Aug 2017 updated
Crypted virus Removal Guide
Description of Crypted virus
Crypted virus: should you be afraid of this computer infection?

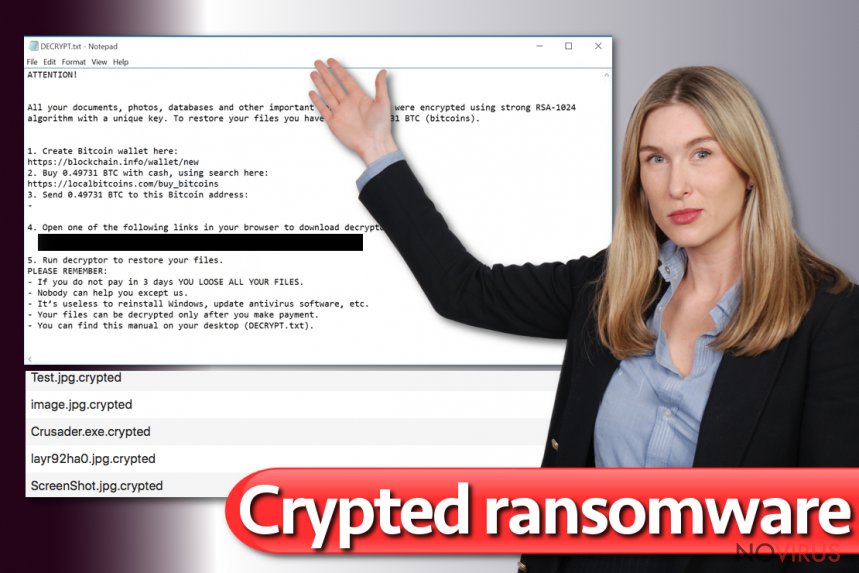
Crypted virus is one of many ransomware-type viruses that are spreading all around the Internet. The authors created this malware to blackmail people: once the virus gets inside the system, it encrypts all victim’s personal files and asks to pay the ransom. How does it get on the computer? It might enter with a help of malicious email attachment, malware-laden ad or exploit kit.
There are numerous ways how Crypted ransomware can infiltrate computers. To avoid this malware, users should pay attention to their computer’s security and look their behaviour online. Once the ransomware gets inside, it starts scanning a computer and looking for necessary file extensions.
Unfortunately, it can encrypt hundreds of different types of files using strong RSA algorithm. There’s no way that some of your personal documents might survive the attack; all of them are damaged and have .crypted file extension.
Following data encryption, the virus drops ransom notes where criminals explain what have happened. They try to scare and convince victims that the only solution to get back access to their files is to pay the ransom. However, we have some good news for you! Virus researchers managed to crack virus code and created a free decryption tool. Therefore, all you need to after the attack is to remove Crypted from your PC. FortectIntego will help you to wipe out malware and protect your computer from other virus attacks in the future.
Ransomware viruses are quite trendy right now in the cyber world. Unfortunately, this trend is scary and cause computer users many problems, such as data and money loss. Crypted ransomware virus as well as other file-encrypting viruses damage files using a strong algorithm and try to swindle the money from frightened computer users. In the ransom note hackers always stress out that all victim’s files were corrupted using a sophisticated algorithm and explain that data decryption is possible only with their provided software.
The creators of Crypted malware also provide links and explanation how to download anonymous Tor browser, which is necessary for making the payment. Sadly, lots of victims believe in cyber criminals’ words and transfer the money, and then, they are left with an even bigger loss. If you consider paying the ransom, bear in mind that crooks usually disappear after receiving the payment. We want to remind you that after the attack, you should not rush with wasting your money. Concentrate on virus elimination, and meanwhile, virus researchers might develop a free decryption tool. Don’t delay Crypted removal, because the virus is capable of installing additional malware and make your computer’s system even more vulnerable.
How does malware proliferate?
The biggest chance to meet Crypted virus is in spam email inbox. Similarly to other file-encrypting viruses, this malware also mainly spread via malicious email campaigns. Security specialists remind people to be careful online and double check information about the sender before opening any email attachments.
Unfortunately, this information doesn’t reach many computer users. They are tricked to open fake invoices, receipts, shopping confirmations and other ‘important’ documents. Once they open an infected file, the virus gets into the system and starts damaging data. Moreover, ransomware viruses might be hidden under various links and malware-laden ads.
Usually, infected advertisements offer to download questionable security tools or warn about problems detected on your computer. We strongly recommend to strengthen your computer’s security with a strong antivirus program and always keep software updated, because Crypted ransomware might enter the system using exploit kits as well.
Crypted removal and data encryption options
If your computer is infected with malware, we have good news for you. You can remove Crypted and restore corrupted files. The first step you have to take is to install or update anti-malware program. If your computer is unprotected, we recommend installing one of these programs: FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes.
If you already have a reputable antivirus program, update it right now. Sometimes malware disables antivirus programs or prevents from scanning the system. In this case, reboot the computer in the Safe Mode with Networking and follow the instructions below. After Crypted removal, you can restore your files from backups or use decryption software. All necessary information related to data recovery options you will find bellow as well.
Getting rid of Crypted virus. Follow these steps
In-depth guide for the Crypted elimination
Important! →
The elimination guide can appear too difficult if you are not tech-savvy. It requires some knowledge of computer processes since it includes system changes that need to be performed correctly. You need to take steps carefully and follow the guide avoiding any issues created due to improper setting changes. Automatic methods might suit you better if you find the guide too difficult.
Step 1. Launch Safe Mode with Networking
Safe Mode environment offers better results of manual virus removal
Windows 7 / Vista / XP
- Go to Start.
- Choose Shutdown, then Restart, and OK.
- When your computer boots, start pressing the F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) a few times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click the Start button and choose Settings.

- Scroll down to find Update & Security.

- On the left, pick Recovery.
- Scroll to find Advanced Startup section.
- Click Restart now.

- Choose Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.

- Choose 5) Enable Safe Mode with Networking.
Step 2. End questionable processes
You can rely on Windows Task Manager that finds all the random processes in the background. When the intruder is triggering any processes, you can shut them down:
- Press Ctrl + Shift + Esc keys to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes.
- Look for anything suspicious.
- Right-click and select Open file location.

- Go back to the Process tab, right-click and pick End Task.
- Delete the contents of the malicious folder.
Step 3. Check the program in Startup
- Press Ctrl + Shift + Esc on your keyboard again.
- Go to the Startup tab.
- Right-click on the suspicious app and pick Disable.

Step 4. Find and eliminate virus files
Data related to the infection can be hidden in various places. Follow the steps and you can find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive (C: is your main drive by default and is likely to be the one that has malicious files in) you want to clean.
- Scroll through the Files to delete and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Eliminate Crypted using System Restore
-
Step 1: Restart your computer in Safe Mode with Command Prompt
Windows 7 / Vista / XP- Go to Start → Shutdown → Restart → OK.
- As soon as your computer starts, start pressing F8 key repeatedly before the Windows logo shows up.
-
Choose Command Prompt from the list

Windows 10 / Windows 8- Click on the Power button at the Windows login screen, and then press and hold Shift key on your keyboard. Then click Restart.
- Then select Troubleshoot → Advanced options → Startup Settings and click Restart.
-
Once your computer starts, select Enable Safe Mode with Command Prompt from the list of options in Startup Settings.

-
Step 2: Perform a system restore to recover files and settings
-
When the Command Prompt window appears, type in cd restore and press Enter.

-
Then type rstrui.exe and hit Enter..

-
In a new window that shows up, click the Next button and choose a restore point that was created before the infiltration of Crypted and then click on the Next button again.


-
To start system restore, click Yes.

-
When the Command Prompt window appears, type in cd restore and press Enter.
Bonus: Restore your files
Using the tutorial provided above you should be able to eliminate Crypted from the infected device. novirus.uk team has also prepared an in-depth data recovery guide which you will also find above.If you have encountered Crypted virus, do not consider paying the ransom! Virus researchers have already created a Crypted decryption software, so feel free to use it.
There are a couple of methods you can apply to recover data encrypted by Crypted:
Recover files with Crypter decryptor
For data recovery, you will need to download Crypter decryptor. Select encrypted and unencrypted file and upload them onto the decrypter. Then, the decryptor will provide you the key, which is neccessary for data decryption.
It is strongly recommended to take precautions and secure your computer from malware attacks. To protect your PC from Crypted and other dangerous viruses, you should install and keep a powerful malware removal tool, for instance, FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes.
How to prevent from getting ransomware
Securely connect to your website wherever you are
Sometimes you may need to log in to a content management system or server more often, especially if you are actively working on a blog, website, or different project that needs constant maintenance or that requires frequent content updates or other changes. Avoiding this problem can be easy if you choose a dedicated/fixed IP address. It's a static IP address that only belongs to a specific device and does not change when you are in different locations.
VPN service providers such as Private Internet Access can help you with these settings. This tool can help you control your online reputation and successfully manage your projects wherever you are. It is important to prevent different IP addresses from connecting to your website. With a dedicated/fixed IP address, VPN service, and secure access to a content management system, your project will remain secure.
Reduce the threat of viruses by backing up your data
Due to their own careless behavior, computer users can suffer various losses caused by cyber infections. Viruses can affect the functionality of the software or directly corrupt data on your system by encrypting it. These problems can disrupt the system and cause you to lose personal data permanently. There is no such threat if you have the latest backups, as you can easily recover lost data and get back to work.
It is recommended to update the backups in parallel each time the system is modified. This way, you will be able to access the latest saved data after an unexpected virus attack or system failure. By having the latest copies of important documents and projects, you will avoid serious inconveniences. File backups are especially useful if malware attacks your system unexpectedly. We recommend using the Data Recovery Pro program to restore the system.







