Uninstall BBOO virus (Virus Removal Tutorial) - Decryption Methods Included
BBOO virus Removal Guide
Description of BBOO ransomware removal guide
BBOO ransomware – a dangerous computer infection that may result in complete loss of personal files
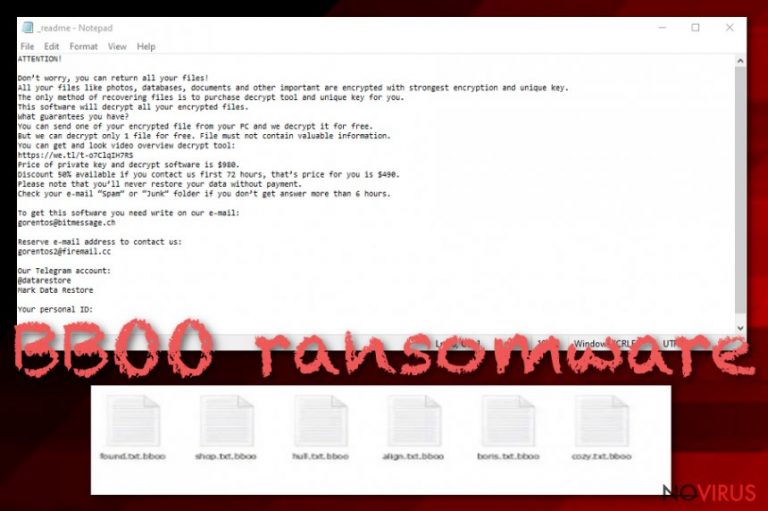
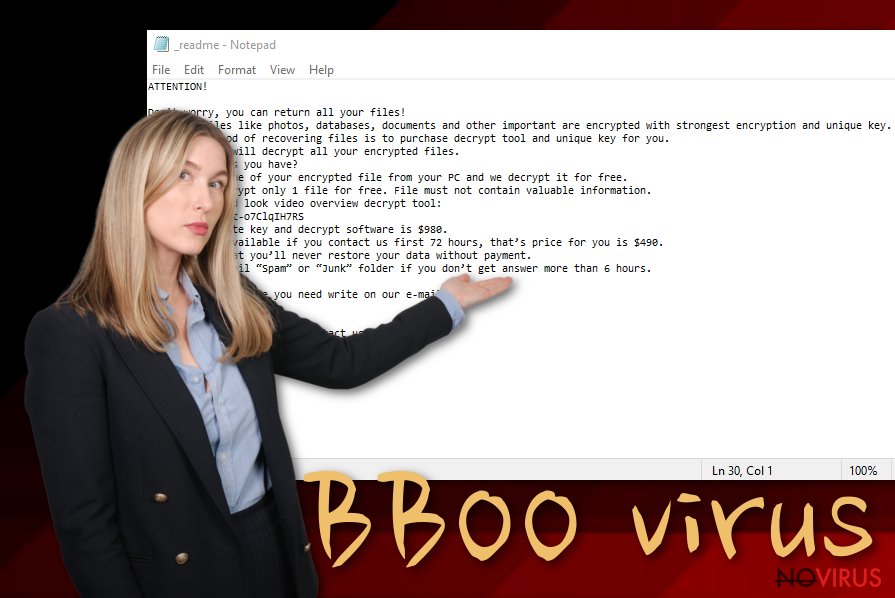
BBOO ransomware is a file locking virus that stems from a notorious family Djvu/STOP and is usually spread via pirated software installers or cracks/keygens. Once inside the system, the malware performs a variety of changes to it and then begins to look for files to encrypt. As a result, all pictures, documents, databases, and other data receive a .bboo file extension, and the owners can no longer access it.
To ensure that users are aware of what happened to their files, malicious actors behind the BBOO virus also provide a ransom note _readme.txt, which is placed inside almost every folder, as well as the desktop. Inside, hackers ask victims to contact them via the helpdatarestore@firemail.cc or helpmanager@mail.ch emails, and then pay $490 for the BBOO ransomware decryptor.
If you got infected with BBOO ransomware, you should not rush paying cybercriminals, as we will provide instructions that may help you retrieve data using alternative methods listed below.
| Name | BBOO ransomware |
| Type | Cryptovirus, file locking malware |
| Originates from | Djvu/STOP ransomware family |
| Distribution | Almost all infections of Djvu stem from pirated software installers and software cracks/keygens download from third-party websites |
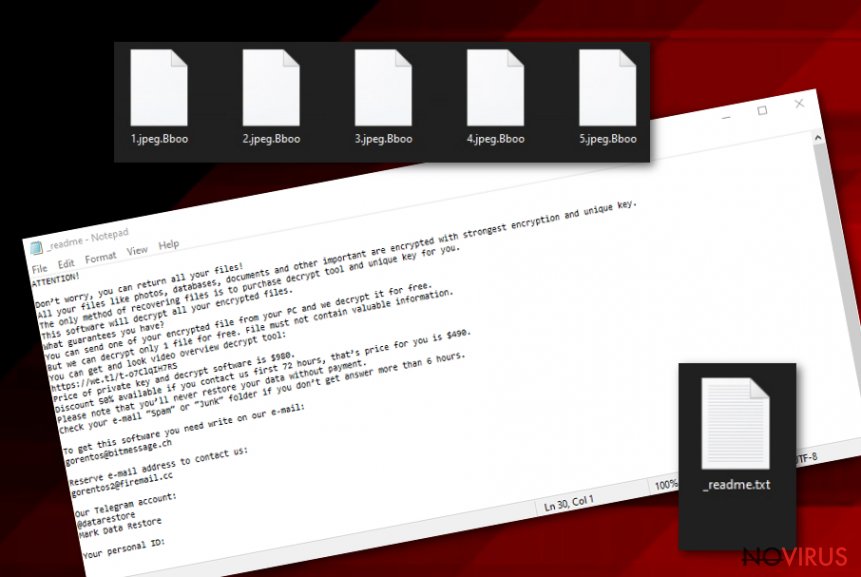
| File extension | Each of the personal files is applied with .bboo extension; example of an encrypted file: picture.jpg.bboo |
| Encryption algorithm | Personal data is encrypted with the help of the RSA cipher, although malware skips most of the executables and system files |
| Ransom note | _readme.txt is dropped on the desktop as well as every folder where encrypted files are located |
| Contact details | Users are asked to send an email to helpdatarestore@firemail.cc or helpmanager@mail.ch to establish contact with cybercriminals responsible for ransomware infection |
| Ransom size | Initially, hackers ask for $490 in Bitcoin, although this sum doubles after 72 hours |
| Malware removal | Download and install powerful security software that can detect the threat and perform a full system scan (in Safe Mode if required) |
| File recovery | There are minimal chances of recovering data without backups, although Emsisoft's decryptor should work for those whose files encrypted using an offline ID. Additionally, data recovery tools may also retrieve at least some portion of the data. For more details, refer to the recovery section below |
| System fix | Since ransomware heavily modifies Windows system files, it may also damage the in the process. As a result, a computer may crash and become unstable. To avoid the operating system reinstallation, scan your computer with repair software FortectIntego – it will attempt to fix virus damage and replace corrupted system files with working ones |
Djvu/Stop ransomware has a long history in the cybercriminal world and is now a well-established illegal business for actors behind it. At the time of the writing, there are over 200 variants released, with at least two being produced each week. Cybercriminals keep releasing new versions because thousands of users get infected, and some are willing to pay the ransom, making it a lucrative business. BBOO ransomware is 205th version of the virus spotted in the wild – previous ones include:
BBOO ransomware removal is vital for every infected system, as cybercriminals are known to insert additional malware modules that can steal sensitive data from various web browsers, such as Google Chrome, Mozilla Firefox, or Internet Explorer. Due to this component, users may expose their credentials, banking information, and other sensitive data to cybercriminals, which can result in devastating consequences such as money loss or even identity theft.
Additionally, BBOO ransomware is also programmed to modify Windows “hosts” file in order to prevent users from visiting security-related websites that could help them deal with the infection and provide alternative methods for file recovery. To revert this, users should visit the following folder and delete the “hosts” file – it will be recreated by Windows automatically, although the malware-added IPs will be removed:
C:\Windows\System32\drivers\etc\
Besides, some variants of this ransomware were distributed with another malware, such as data-stealer AZORult – this is another reason to remove BBOO ransomware as soon as possible (important note: if you have no backups to restore your files from, make a copy of encrypted files before removing malware from your computer, as this action may permanently damage data without any chance of recovery). After you get rid of malware, scan your machine with FortectIntego to ensure it recovered promptly – this will prevent any stability or functionality issues.
System modification and file encryption
As soon as the BBOO ransomware virus starts the infection routine, it begins to prepare the system for the file encryption process. The virus performs the following changes:
- Modifies Windows registry to establish persistence
- Deletes Shadow Volume Copies with the help of “vssadmin delete shadows /all /quiet” command
- Contacts a remote Command-and-Control server and makes several other HTTP requests
- Drops multiple malicious files into %LocalAppData%, %Temp%, %WinDir% and other folders, etc.
As soon as the necessary changes are complete, BBOO ransomware will begin a full system scan, looking for predetermined file types, such as .doc, .pdf, .jpg, .mp4, .rar, and many others. During this time, the virus will show a fake Windows Update window in order to prevent users from interrupting the procedure.
After the encryption process, users will be immediately presented with the ransom note _readme.txt, which reads:
ATTENTION!
Don’t worry, you can return all your files!
All your files like photos, databases, documents and other important are encrypted with strongest encryption and unique key.
The only method of recovering files is to purchase decrypt tool and unique key for you.
This software will decrypt all your encrypted files.
What guarantees you have?
You can send one of your encrypted file from your PC and we decrypt it for free.
But we can decrypt only 1 file for free. File must not contain valuable information.
You can get and look video overview decrypt tool:
https://we.tl/t-Oc0xgfzC7q
Price of private key and decrypt software is $980.
Discount 50% available if you contact us first 72 hours, that’s price for you is $490.
Please note that you’ll never restore your data without payment.
Check your e-mail “Spam” or “Junk” folder if you don’t get answer more than 6 hours.To get this software you need write on our e-mail:
helpmanager@firemail.ccReserve e-mail address to contact us:
helpmanager@iran.irYour personal ID:
BBOO ransomware: file recovery options
BBOO ransomware belongs to the newer surge of Djvu ransomware viruses that use more advanced encryption with the help of the asymmetric RSA cypher. Before August 2019, most of the malware versions applied the AES algorithm, which was relatively weak – this served as a major breakthrough when it came to data decryption options, as security experts from Emsisoft managed to create a decryptor that worked for 148 versions.
Unfortunately, the RSA-encrypted files were secured more tightly. Since BBOO ransomware came out in early February 2020, it can no longer be decrypted. Emsisoft, however, also provides an alternative tool that can help some users, even if they were infected with a version released past August 2019.
For that tool to work, the BBOO virus should have failed to contact its C&C server, which can happen due to various reasons, including victims ' bandwidth problems, or if the encryption process was interrupted. There is no particular way to establish whether an offline ID was used, so the only way to find out is to try using the decryptor.
If BBOO encrypted files with an online ID, data recovery without paying hackers is low. However, you can attempt to recover at least some files with data recovery tools or make use of built-in features like Windows Previous Version. For comprehensive instructions, please refer to our recovery section below.
Even if none of the above helped you, you should not lose hope. Security experts are constantly working on free decryption software, and a working tool for BBOO ransomware may be released in the future.
Software cracks and pirated software installers – the main ransomware attack vector
Users often ignore cybersecurity experts' advice and proceed to risk their online safety by neglecting basic malware prevention measures. As a result, they infect their machines with such dangerous malware like ransomware, and then ask for help, although it might be a little too late, as ransomware does not revert changes to data, even after it is removed. Therefore, it is best to listen to industry experts to prevent permanent data loss, as well as other negative consequences.
Most of Djvu variants are spread with the help pirated software installers, and software cracks/keygens such as KMSpico – these tools are designed to bypass the licencing process of the program, which allows its free usage. However, these files can often be booby-trapped with malware, and most of the security software will flag cracks as malicious regardless if they include malware payload or not. Thus, there is no way to check whether the installer is actually malicious.
For that reason, we highly advise you staying away from software cracks and unsolicited installers, as these are often malicious. Instead, download and alternative software that is free to use, or purchase a licence for a program you wanted initially. Besides this, you should always practice additional security measures:
- When dealing with spam email attachments do not allow a macro function to run; do not click on hyperlinks inside a suspicious email
- Keep Windows and all the other programs on your computer updated with latest security patches
- Employ comprehensive security software with real-time protection feature
- Use two-factor authentication where possible, and never reuse passwords for different accounts
- Backup your files on a regular basis.
BBOO ransomware removal instructions
Before you proceed with BBOO ransomware removal, you should first consider whether you have a working backup. Under no circumstances connect to a remote server or external storage that holds your files, as these will also be encrypted by ransomware. However, if you have no backups, you should not get rid of BBOO virus just yet.
If you remove BBOO ransomware immediately, the encrypted data may become permanently damaged. As a result, even a working decryption tool will not be able to help you. Thus, backup the locked data, and only then scan your machine with a reputable anti-malware software, such as SpyHunter 5Combo Cleaner or Malwarebytes. A full system scan will ensure that all the malicious files are deleted correctly. Note that, in some cases, ransomware may interfere with your security software; if that happens, access Safe Mode with Networking as explained below.
After you are sure that BBOO file virus is eliminated, you can then attempt to recover your data with the help of Emsisoft's decryptor or third-party recovery tools.
Getting rid of BBOO virus. Follow these steps
In-depth guide for the BBOO elimination
You can access Safe Mode with Networking if ransomware interferes with your anti-malware software:
Important! →
The elimination guide can appear too difficult if you are not tech-savvy. It requires some knowledge of computer processes since it includes system changes that need to be performed correctly. You need to take steps carefully and follow the guide avoiding any issues created due to improper setting changes. Automatic methods might suit you better if you find the guide too difficult.
Step 1. Launch Safe Mode with Networking
Safe Mode environment offers better results of manual virus removal
Windows 7 / Vista / XP
- Go to Start.
- Choose Shutdown, then Restart, and OK.
- When your computer boots, start pressing the F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) a few times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click the Start button and choose Settings.

- Scroll down to find Update & Security.

- On the left, pick Recovery.
- Scroll to find Advanced Startup section.
- Click Restart now.

- Choose Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.

- Choose 5) Enable Safe Mode with Networking.
Step 2. End questionable processes
You can rely on Windows Task Manager that finds all the random processes in the background. When the intruder is triggering any processes, you can shut them down:
- Press Ctrl + Shift + Esc keys to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes.
- Look for anything suspicious.
- Right-click and select Open file location.

- Go back to the Process tab, right-click and pick End Task.
- Delete the contents of the malicious folder.
Step 3. Check the program in Startup
- Press Ctrl + Shift + Esc on your keyboard again.
- Go to the Startup tab.
- Right-click on the suspicious app and pick Disable.

Step 4. Find and eliminate virus files
Data related to the infection can be hidden in various places. Follow the steps and you can find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive (C: is your main drive by default and is likely to be the one that has malicious files in) you want to clean.
- Scroll through the Files to delete and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Eliminate BBOO using System Restore
Safe Mode may also be used for malware elimination:
-
Step 1: Restart your computer in Safe Mode with Command Prompt
Windows 7 / Vista / XP- Go to Start → Shutdown → Restart → OK.
- As soon as your computer starts, start pressing F8 key repeatedly before the Windows logo shows up.
-
Choose Command Prompt from the list

Windows 10 / Windows 8- Click on the Power button at the Windows login screen, and then press and hold Shift key on your keyboard. Then click Restart.
- Then select Troubleshoot → Advanced options → Startup Settings and click Restart.
-
Once your computer starts, select Enable Safe Mode with Command Prompt from the list of options in Startup Settings.

-
Step 2: Perform a system restore to recover files and settings
-
When the Command Prompt window appears, type in cd restore and press Enter.

-
Then type rstrui.exe and hit Enter..

-
In a new window that shows up, click the Next button and choose a restore point that was created before the infiltration of BBOO and then click on the Next button again.


-
To start system restore, click Yes.

-
When the Command Prompt window appears, type in cd restore and press Enter.
Bonus: Restore your files
Using the tutorial provided above you should be able to eliminate BBOO from the infected device. novirus.uk team has also prepared an in-depth data recovery guide which you will also find above.There are a couple of methods you can apply to recover data encrypted by BBOO:
Data Recovery Pro option may be viable
The less you use your computer after the infection, the more chances there are that Data Recovery Pro can recover at least some of your files.
- Download Data Recovery Pro;
- Install Data Recovery on your computer following the steps indicated in the software’s Setup;
- Run the program to scan your device for the data encrypted by BBOO ransomware;
- Recover the data.
Make use of Windows Previous Version when dealing with BBOO ransomware
If you had System Restore enabled before malware infection, this method might be useful.
- Right-click on the encrypted document you want to recover;
- Click “Properties” and navigate to “Previous versions” tab;
- In the “Folder versions” section look for the available file copies. Choose the desired version and press “Restore”.
Recover your data with ShadowExplorer
ShadowExplorer might be successful at restoring all your files if the virus failed to remove Shadow Volume Copies.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Install Shadow Explorer on your computer following the instructions in the software’s Setup Wizard;
- Run the program. Navigate to the menu on the top-left corner and select a disk containing your encrypted files. Look through the available folders;
- When you find the folder you want to recover, right-click it and select “Export”. Also, choose where the recovered data will be stored.
Try Emsisoft's decryptor and Dr.Web
In case you are lucky, and data encryption was performed using an offline ID, Emsisoft's decryptor might be helpful for you. If no luck, you can also ask Dr.Web to provide recovery options for you (might work for some file types only), although the service is not free.
It is strongly recommended to take precautions and secure your computer from malware attacks. To protect your PC from BBOO and other dangerous viruses, you should install and keep a powerful malware removal tool, for instance, FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes.
How to prevent from getting ransomware
Securely connect to your website wherever you are
Sometimes you may need to log in to a content management system or server more often, especially if you are actively working on a blog, website, or different project that needs constant maintenance or that requires frequent content updates or other changes. Avoiding this problem can be easy if you choose a dedicated/fixed IP address. It's a static IP address that only belongs to a specific device and does not change when you are in different locations.
VPN service providers such as Private Internet Access can help you with these settings. This tool can help you control your online reputation and successfully manage your projects wherever you are. It is important to prevent different IP addresses from connecting to your website. With a dedicated/fixed IP address, VPN service, and secure access to a content management system, your project will remain secure.
Reduce the threat of viruses by backing up your data
Due to their own careless behavior, computer users can suffer various losses caused by cyber infections. Viruses can affect the functionality of the software or directly corrupt data on your system by encrypting it. These problems can disrupt the system and cause you to lose personal data permanently. There is no such threat if you have the latest backups, as you can easily recover lost data and get back to work.
It is recommended to update the backups in parallel each time the system is modified. This way, you will be able to access the latest saved data after an unexpected virus attack or system failure. By having the latest copies of important documents and projects, you will avoid serious inconveniences. File backups are especially useful if malware attacks your system unexpectedly. We recommend using the Data Recovery Pro program to restore the system.







