Uninstall Aleta virus (Improved Guide) - Free Removal Instructions
Aleta virus Removal Guide
Description of Aleta ransomware
BTCWare Aleta virus attacks computers worldwide, asks for large ransoms
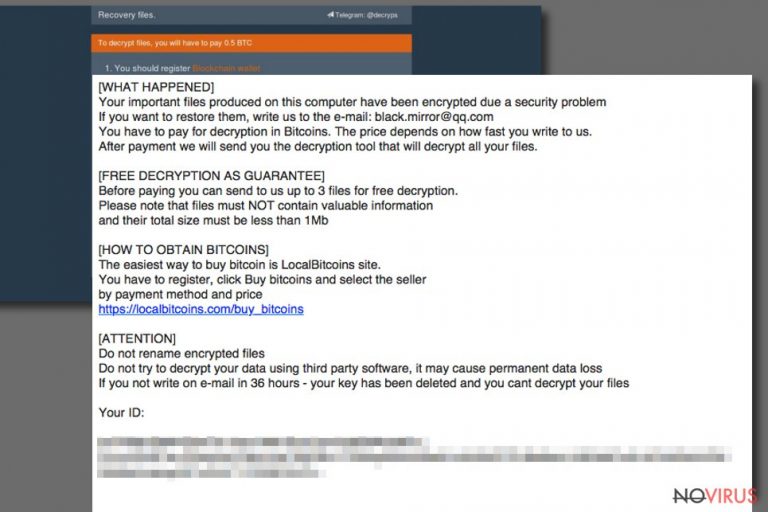
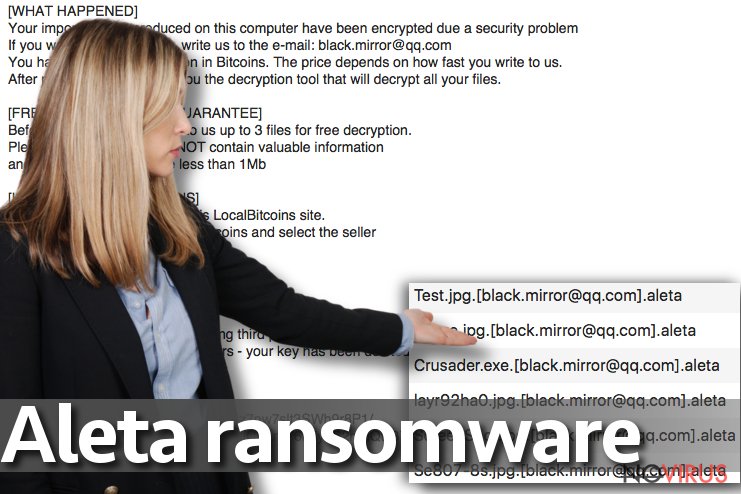
Aleta ransomware is a new data-encoding virus that belongs to BTCWare ransomware family. As soon as it infiltrates the target computer system, it encrypts files, adds .[black.mirror@qq.com].aleta file extensions to their filenames and drops !#_READ_ME_#!.inf file. This file is the ransom note that contains instructions on how to recover encrypted data.
The virus is also known as BTCWare Aleta ransomware. Its functionality hardly differs from earlier BTCWare versions – it is an illegal program designed to temporarily or permanently corrupt files on victim’s computer. There are very few possibilities to recover encrypted data, and of course, everything depends on victim’s choices.
The !#_READ_ME_#!.inf file left on victim’s computer informs the victim about the ransomware attack. It suggests writing to black.mirror@qq.com email to discover data recovery possibilities. Of course, criminals take advantage of victim’s frustration and suggest buying the data decryption tool for a particular price – ransom.
Unlike previous BTCWare variants, Aleta uses only one email address for communication with ransomware victims. For example, Master ransomware used more than ten different email addresses for the same purpose.
Aleta demands 2 Bitcoins per each compromised computer. In British pounds, this sum equals 3700. It goes without saying that cyber security experts do not recommend paying sum amounts of money to cybercriminals, especially when there are no guarantees regarding data recovery.
Remember that fraudsters use all possible methods to make themselves anonymous; therefore it wouldn’t be possible to catch them if they would decide to deceive you.
BTCWare Aleta developers suggest testing their decryptor on three files no larger than 1 Mb in their total size. These files can be sent to criminals via email. Criminals claim that their reply will contain decrypted versions of these files.
However, you shouldn’t put your trust in cybercriminals’ promises. We highly recommend deleting the ransomware with an anti-spyware or anti-malware program to protect the system from further damage. To remove Aleta, use trustworthy programs like FortectIntego or Malwarebytes.
Distribution of BTCWare-based viruses
Aleta virus is distributed in a similar way like the rest of viruses from BTCWare ransomware group. They all are promoted via traditional malware distribution techniques such as:
- Malicious spam;
- Exploit kits;
- Trojans;
- Malvertising;
- Illegal software.
To avoid installing this virus, never open email attachments that come from someone who is a complete stranger to you. Also, remember that scammers just love to pretend that they’re working at legitimate companies.
Just because someone who claims to be from Amazon sent you an invoice or a receipt in a letter filled with Amazon logos, it doesn’t mean that you are talking to a real employee. It can a scammer trying to push malware to your computer.
To ward off ransomware distributed in different ways, you will need a powerful anti-malware solution and a data backup. These are two must-haves in order to bypass tragic consequences that ransomware can cause.
Remove Aleta ransomware with ease
It can be hard to remove Aleta virus because it tends to create obstacles for anti-malware or anti-spyware to start. To prepare a safe environment for malware removal software, restart your PC into Safe Mode with Networking.
The 2-spyware team says that there should be no attempts to perform a manual BTCware Aleta removal. This ransomware is highly sophisticated, and unless you are a professional malware analyst, most likely you won’t find all files and programs associated with the virus.
Getting rid of Aleta virus. Follow these steps
In-depth guide for the Aleta elimination
You can only remove Aleta after rebooting your PC into Safe Mode with Networking. This tutorial explains everything from A to Z to ease the task for you.
Important! →
The elimination guide can appear too difficult if you are not tech-savvy. It requires some knowledge of computer processes since it includes system changes that need to be performed correctly. You need to take steps carefully and follow the guide avoiding any issues created due to improper setting changes. Automatic methods might suit you better if you find the guide too difficult.
Step 1. Launch Safe Mode with Networking
Safe Mode environment offers better results of manual virus removal
Windows 7 / Vista / XP
- Go to Start.
- Choose Shutdown, then Restart, and OK.
- When your computer boots, start pressing the F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) a few times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click the Start button and choose Settings.

- Scroll down to find Update & Security.

- On the left, pick Recovery.
- Scroll to find Advanced Startup section.
- Click Restart now.

- Choose Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.

- Choose 5) Enable Safe Mode with Networking.
Step 2. End questionable processes
You can rely on Windows Task Manager that finds all the random processes in the background. When the intruder is triggering any processes, you can shut them down:
- Press Ctrl + Shift + Esc keys to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes.
- Look for anything suspicious.
- Right-click and select Open file location.

- Go back to the Process tab, right-click and pick End Task.
- Delete the contents of the malicious folder.
Step 3. Check the program in Startup
- Press Ctrl + Shift + Esc on your keyboard again.
- Go to the Startup tab.
- Right-click on the suspicious app and pick Disable.

Step 4. Find and eliminate virus files
Data related to the infection can be hidden in various places. Follow the steps and you can find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive (C: is your main drive by default and is likely to be the one that has malicious files in) you want to clean.
- Scroll through the Files to delete and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Eliminate Aleta using System Restore
-
Step 1: Restart your computer in Safe Mode with Command Prompt
Windows 7 / Vista / XP- Go to Start → Shutdown → Restart → OK.
- As soon as your computer starts, start pressing F8 key repeatedly before the Windows logo shows up.
-
Choose Command Prompt from the list

Windows 10 / Windows 8- Click on the Power button at the Windows login screen, and then press and hold Shift key on your keyboard. Then click Restart.
- Then select Troubleshoot → Advanced options → Startup Settings and click Restart.
-
Once your computer starts, select Enable Safe Mode with Command Prompt from the list of options in Startup Settings.

-
Step 2: Perform a system restore to recover files and settings
-
When the Command Prompt window appears, type in cd restore and press Enter.

-
Then type rstrui.exe and hit Enter..

-
In a new window that shows up, click the Next button and choose a restore point that was created before the infiltration of Aleta and then click on the Next button again.


-
To start system restore, click Yes.

-
When the Command Prompt window appears, type in cd restore and press Enter.
Bonus: Restore your files
Using the tutorial provided above you should be able to eliminate Aleta from the infected device. novirus.uk team has also prepared an in-depth data recovery guide which you will also find above.We do not recommend paying the ransom to Aleta developers because malware analysts managed to create decryption tools for previous versions of BTCWare. Therefore, you can either test your patience, or try one of data recovery methods listed below.
There are a couple of methods you can apply to recover data encrypted by Aleta:
Check out this data recovery tool
Data Recovery Pro is a software praised by many users who accidentally deleted or corrupted their files. Although it wasn’t balanced to work on files encrypted by ransomware, we still recommend trying it.
- Download Data Recovery Pro;
- Install Data Recovery on your computer following the steps indicated in the software’s Setup;
- Run the program to scan your device for the data encrypted by Aleta ransomware;
- Recover the data.
Try to find those Volume Shadow Copies
Volume Shadow Copies are data backups created by Microsoft Windows system. However, many ransomware viruses delete these copies right after the data encryption procedure. Sometimes, ransomware viruses fail to complete all tasks properly. This idea makes us think that ShadowExplorer could come in handy when looking for those Volume Shadow Copies.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Install Shadow Explorer on your computer following the instructions in the software’s Setup Wizard;
- Run the program. Navigate to the menu on the top-left corner and select a disk containing your encrypted files. Look through the available folders;
- When you find the folder you want to recover, right-click it and select “Export”. Also, choose where the recovered data will be stored.
It is strongly recommended to take precautions and secure your computer from malware attacks. To protect your PC from Aleta and other dangerous viruses, you should install and keep a powerful malware removal tool, for instance, FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes.
How to prevent from getting ransomware
Securely connect to your website wherever you are
Sometimes you may need to log in to a content management system or server more often, especially if you are actively working on a blog, website, or different project that needs constant maintenance or that requires frequent content updates or other changes. Avoiding this problem can be easy if you choose a dedicated/fixed IP address. It's a static IP address that only belongs to a specific device and does not change when you are in different locations.
VPN service providers such as Private Internet Access can help you with these settings. This tool can help you control your online reputation and successfully manage your projects wherever you are. It is important to prevent different IP addresses from connecting to your website. With a dedicated/fixed IP address, VPN service, and secure access to a content management system, your project will remain secure.
Reduce the threat of viruses by backing up your data
Due to their own careless behavior, computer users can suffer various losses caused by cyber infections. Viruses can affect the functionality of the software or directly corrupt data on your system by encrypting it. These problems can disrupt the system and cause you to lose personal data permanently. There is no such threat if you have the latest backups, as you can easily recover lost data and get back to work.
It is recommended to update the backups in parallel each time the system is modified. This way, you will be able to access the latest saved data after an unexpected virus attack or system failure. By having the latest copies of important documents and projects, you will avoid serious inconveniences. File backups are especially useful if malware attacks your system unexpectedly. We recommend using the Data Recovery Pro program to restore the system.







