Remove Js Miner (Uninstall Guide) - Free Removal Instructions
Js Miner Removal Guide
Description of Js Miner
Js miner is a digital currency mining tool that ca be utilized by hackers to illegally earn money

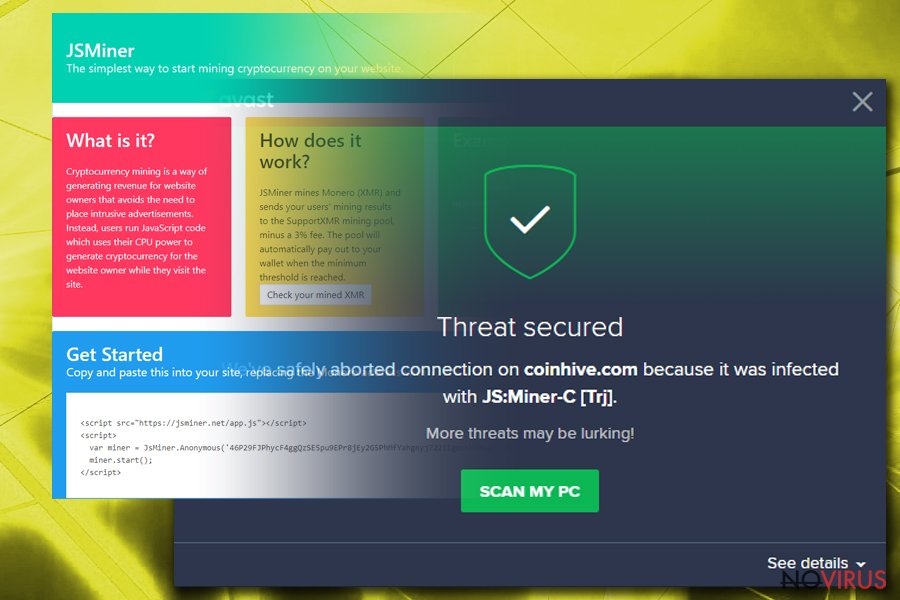
JS miner is a trojan that uses JavaScript code to mine Monero cryptocurrency on the targeted machine. Initially, this application can be used by website creators to monetize on their CPU power – it is a perfect alternative for ads-based sites. However, the website owner needs to inform users about such activity; otherwise it becomes illegal. Unfortunately, cybercriminals learned how to use this legitimate program for their benefit and mine cryptocurrency without users' consent. The malware already has multiple versions, including JS:Miner-C and JS/CoinMiner being the most prominent ones. The mining activity can significantly increase the CPU usage and slow down the performance of the PC, as well as drastically increase the electricity bill.
| Name | JS Miner |
|---|---|
| Type | Trojan Horse |
| Dangers | Can lead to other malware infections |
| Variants |
|
| Distribution | Malicious sites, spam emails |
| Elimination | Install FortectIntego for Js Miner removal |
JS:Miner virus starts running every time the device is booted. Immediately after the malicious payload is executed this program plants various files to Windows, AppData and other folders. The trojan can greatly affect the computer system because it gains admin rights as soon as it is delivered. This allows the threat to run, close down or start various processes.
There is no doubt that the program is malicious and can cause harm to your computer, or even damage the hardware. For this reason, you need to remove JS Miner virus from your device.
JS:Miner Trojan affects the system in the following ways:
- Slows down your computer significantly;
- Highly increases the usage of your PC's CPU;
- Causes software freezes and crashes;
- Leads to unexpected errors and BSoDs.
There are already many variants of JS:Miner detected, and every one of them can perform malicious activities. The purpose of these viruses is to mine cryptocurrency, but most of them have different features also.
These are the JS Miner variants discovered so far:
- JS:MINER-A
- JS:MINER-B
- JS:MINER-C
- JS:MINER-D
- JS:MINER-E
- JS:MINER-F
- JS:MINER-G
- JS:MINER-H
- JS:MINER-I
- JS/CoinMiner
JSMiner-C is the most prominent variant of malware. In addition to the CPU, this version also utilizes GPU power to mine coins. Unfortunately, spotting high graphics card usage is not that easy – third-party software is required to determine how high the GPU usage actually is.
You need to differentiate the symptoms correctly, so you know that this virus is the one that causes issues, not software or driver problems. Scan your PC with anti-malware tool like FortectIntego and make sure to proceed with correct JS miner removal if the application finds it malicious.

Spam email attachments spread malicious files
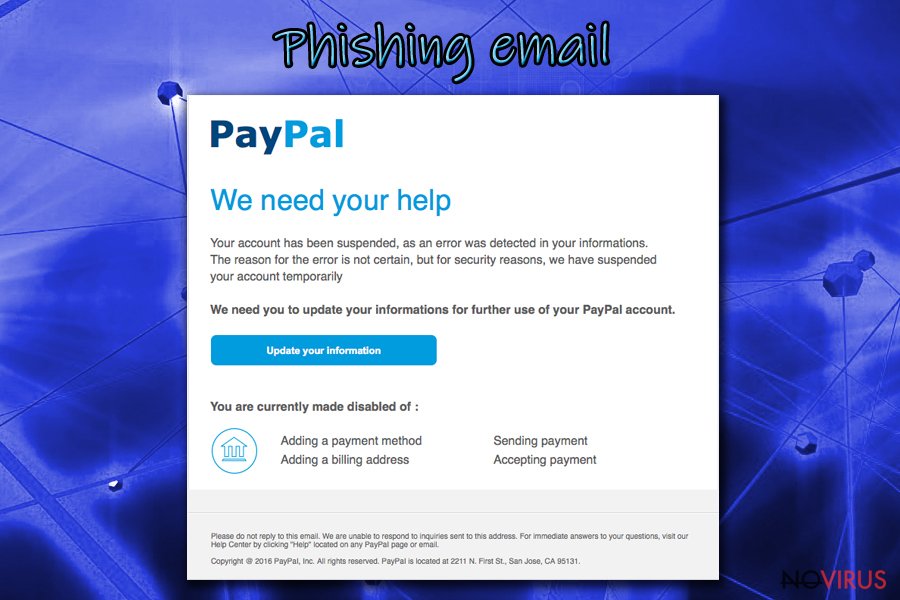
Hackers are in a rush to introduce their malware into as many machines as possible, and they use various techniques for that. The most prominent malware distribution methods are malicious attachments in spam emails or code-infecting into repacked or cracked software.
You need to make sure you are careful when opening emails that you don't recognize. While merely opening a phishing email will not harm your PC in any way, opening attachments or clicking on malicious links will certainly do. Therefore, learn to spot signs of a fake email and avoid terrible consequences.
Malicious websites is another excellent source for malware infestation. Those who like to visit file-sharing or torrent files are more likely to infect their computers with malware. Therefore, assess risks and opt for safe websites and legitimate software only. Besides, cracked programs are illegal to use, and people who use them might be prosecuted for copyright violations.
Terminate JS Miner using certified tools
To remove JS miner, you should rely on anti-malware tools like FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes because the code that is used by a virus is complicated and professional help is needed to repair all the damaged files on the system. Manual JS:Miner removal should be out of the question, as only IT professionals are capable of such a task. Besides, you could damage vital system files which could corrupt your system even further.
Make sure you use legitimate tools for the elimination of malware, as bogus applications will not help you. Keep security software up to date because databases of AV engines are continually updated. Thus, if you fail to update it on time, the outdated database might fail to recognize the virus.
Getting rid of Js Miner. Follow these steps
In-depth guide for the Js Miner elimination
First thing you can do when dealing with Trojan is rebooting your PC in Safe Mode with networking:
Important! →
The elimination guide can appear too difficult if you are not tech-savvy. It requires some knowledge of computer processes since it includes system changes that need to be performed correctly. You need to take steps carefully and follow the guide avoiding any issues created due to improper setting changes. Automatic methods might suit you better if you find the guide too difficult.
Step 1. Launch Safe Mode with Networking
Safe Mode environment offers better results of manual virus removal
Windows 7 / Vista / XP
- Go to Start.
- Choose Shutdown, then Restart, and OK.
- When your computer boots, start pressing the F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) a few times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click the Start button and choose Settings.

- Scroll down to find Update & Security.

- On the left, pick Recovery.
- Scroll to find Advanced Startup section.
- Click Restart now.

- Choose Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.

- Choose 5) Enable Safe Mode with Networking.
Step 2. End questionable processes
You can rely on Windows Task Manager that finds all the random processes in the background. When the intruder is triggering any processes, you can shut them down:
- Press Ctrl + Shift + Esc keys to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes.
- Look for anything suspicious.
- Right-click and select Open file location.

- Go back to the Process tab, right-click and pick End Task.
- Delete the contents of the malicious folder.
Step 3. Check the program in Startup
- Press Ctrl + Shift + Esc on your keyboard again.
- Go to the Startup tab.
- Right-click on the suspicious app and pick Disable.

Step 4. Find and eliminate virus files
Data related to the infection can be hidden in various places. Follow the steps and you can find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive (C: is your main drive by default and is likely to be the one that has malicious files in) you want to clean.
- Scroll through the Files to delete and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Eliminate Js Miner using System Restore
If that is not working well, use System Restore feature:
-
Step 1: Restart your computer in Safe Mode with Command Prompt
Windows 7 / Vista / XP- Go to Start → Shutdown → Restart → OK.
- As soon as your computer starts, start pressing F8 key repeatedly before the Windows logo shows up.
-
Choose Command Prompt from the list

Windows 10 / Windows 8- Click on the Power button at the Windows login screen, and then press and hold Shift key on your keyboard. Then click Restart.
- Then select Troubleshoot → Advanced options → Startup Settings and click Restart.
-
Once your computer starts, select Enable Safe Mode with Command Prompt from the list of options in Startup Settings.

-
Step 2: Perform a system restore to recover files and settings
-
When the Command Prompt window appears, type in cd restore and press Enter.

-
Then type rstrui.exe and hit Enter..

-
In a new window that shows up, click the Next button and choose a restore point that was created before the infiltration of Js Miner and then click on the Next button again.


-
To start system restore, click Yes.

-
When the Command Prompt window appears, type in cd restore and press Enter.
It is strongly recommended to take precautions and secure your computer from malware attacks. To protect your PC from Js Miner and other dangerous viruses, you should install and keep a powerful malware removal tool, for instance, FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes.
How to prevent from getting trojans
Prevent the government from spying on you
As there is a growing debate in government about collecting users' data and spying on citizens, you should take a closer look at this issue and find out what shady ways of gathering information can be used to collect information about you. You need to browse anonymously if you want to avoid any government-initiated spying and tracking of information.
You can enjoy secure internet browsing and minimize the risk of intrusion into your system if you use Private Internet Access VPN program. This VPN application creates a virtual private network and provides access to the required data without any content restrictions.
Control government and other third party access to your data and ensure safe web browsing. Even if you do not engage in illegal activities and trust your ISP, we recommend being careful about your security. You should take extra precautions and start using a VPN program.
Reduce the threat of viruses by backing up your data
Due to their own careless behavior, computer users can suffer various losses caused by cyber infections. Viruses can affect the functionality of the software or directly corrupt data on your system by encrypting it. These problems can disrupt the system and cause you to lose personal data permanently. There is no such threat if you have the latest backups, as you can easily recover lost data and get back to work.
It is recommended to update the backups in parallel each time the system is modified. This way, you will be able to access the latest saved data after an unexpected virus attack or system failure. By having the latest copies of important documents and projects, you will avoid serious inconveniences. File backups are especially useful if malware attacks your system unexpectedly. We recommend using the Data Recovery Pro program to restore the system.







