Uninstall Cerber virus (Uninstall Instructions) - Jun 2018 updated
Cerber virus Removal Guide
Description of Cerber virus
The essential information about Cerber virus
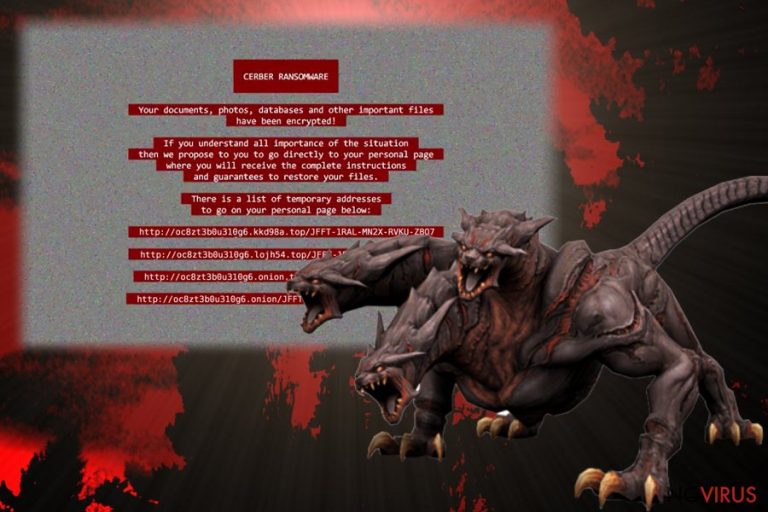
Cerber virus has not built up infanours reputation as it is relatively new ransomware. Like other samples of this category, its primary task is to infect a PC, detect encryptable files and lock them out. Later on, a victim may go spare after finding out that she or he needs to pay more than 343£ in order to retrieve the files.
If this menace has fallen upon you as well, do not foster any hopes to get the data in return even if you remit the payment. Cyber criminals have already wheedled out stunning amounts of money, though reports about the returned data are still few. Thus, paying the ransom is just a waste of money. Instead, you should consider Cerber removal options. One of such options is to use FortectIntego.
How does the virus work?
Cerber ransomware has been launched at the beginning of March after infecting users all over the world. However, one of the distinctive features is that it avoids executing itself in the computers of users, who reside in particular European-Asian countries. These include Armenia, Uzbekistan, Russia, Belarus, Moldova, Ukraine et al.
Moving on, it is crucial to know how it spreads. It is interesting that Cerber has been detected spreading via various channels. Some users have been infected via spam emails. They contain malicious attachments which hide the ransomware within. Hackers have developed quite crafty, deceptive ways to persuade users into opening such emails.
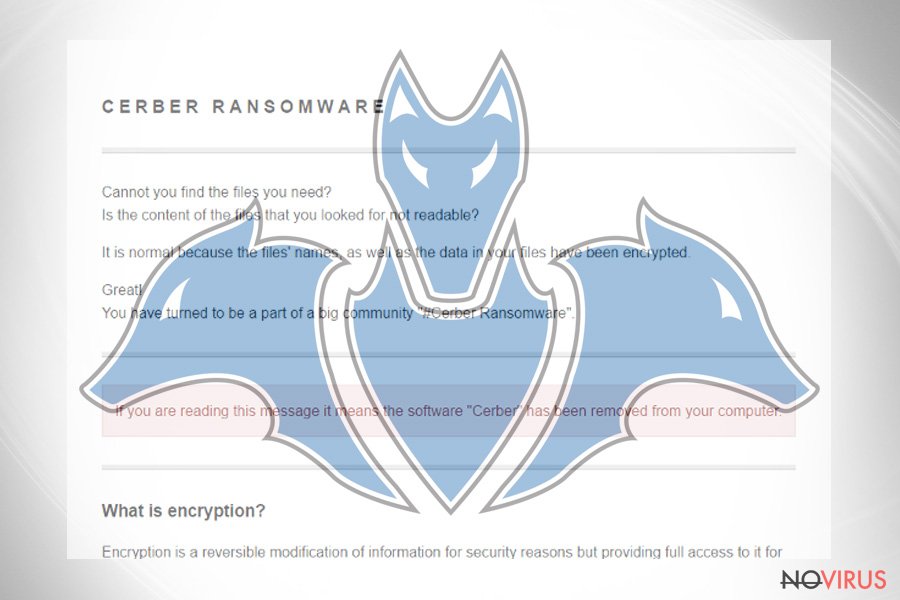
They might look like the emails sent from official institutions. Thus, unsuspecting that treacherous virus awaits to settle on a PC, users open it. Afterward, Cerber malware starts searching for .doc. xls. jpg. and encrypts them. It adds .cerber extension to each locked file. The ransomware also drops the following files: # decrypt my files #.html, # decrypt my files #.txt, and # decrypt my files #.vbs.
Additionally, it has been observed that Cerber virus might slither into a computer via public chat websites as well. Some users reported that the file of ransomware was put in one the forums. Other users claimed that their computers got infected after they connected to a wifi hotspot. After getting redirected to some advertising website and system reboot, a ransom note emerged stating of the misdeed.
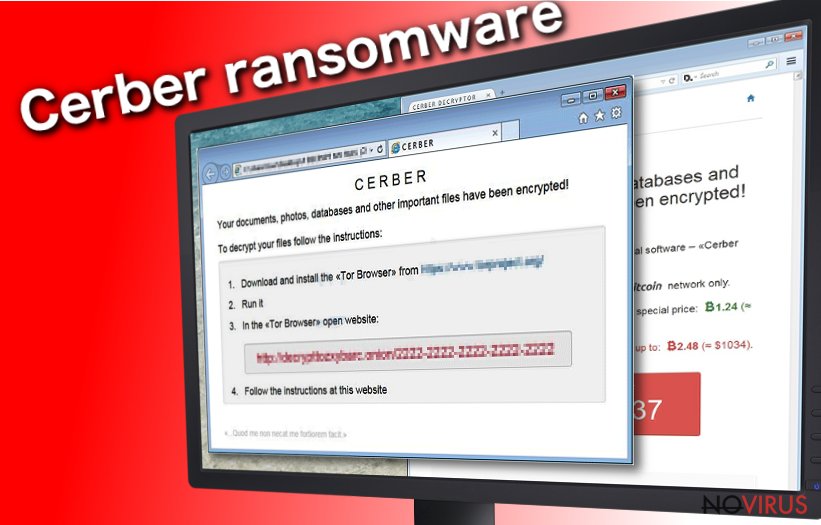
Speaking of the ransom note itself, it provides instructions on how to proceed with the payment using Cerber decryptor. Cyber criminals urge you to buy this program in order to retrieve the files. Needless to say, you might end up getting more infected and with no returned files at all. There are some programs, such as PhotoRec or Data Recovery Pro, which might help you recover the files if you didn’t back the data up. However, there are no guarantees that you might succeed in retrieving the information. That is why it would be wise to remove Cerber rather than hope for hackers’ mercy.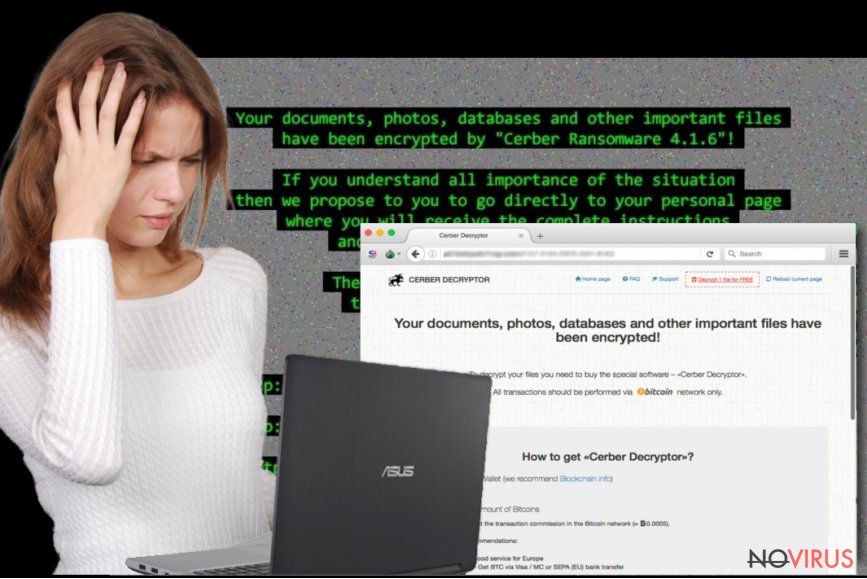
Versions of Cerber ransomware:
Cerber Decryptor. To push their victims into paying ransoms, the developers of Cerber decided to release Cerber Decryptor which promises to decrypt encrypted files. This tool costs a ridiculously huge amount of money – victims can buy this software for 2.480 bitcoins. Should you spend such huge amount of money for this tool? Absolutely not. Cyber security specialists have already released a free decrypter for the first version of this ransomware. Besides, hackers might try to swindle your money and fail to reveal a key which is able to recover your data or try to infect your computer with additional ransomware with its help. So, using this tool might cause further computer-related problems.
Cerber2 ransomware. It is the second version of Cerber virus that was released in August 2016. The most popular ways how this ransomware spreads is malvertising and spam email campaigns. The virus uses a strong algorithm for file encryption and adds .cerber2 file extension to all of corrupted files. The developers of this second Cerber version are trying to convince their victims that the only way to recover their files is to pay the ransom. Unfortunately, spending the money doesn’t guarantee that you will get your data back. Cyber criminals are interested only in collecting ransoms and often forget what they promise to their victims. Of course, there’s always a chance that the decryption tool will restore your encrypted data, but it might come with other malicious files.
Cerber3 virus. It seems that Cerber is not going to leave us so easily. When IT specialists found a flaw and created a Cerber2 decryptor, hackers decided to update their ransomware to the next version. Unfortunately, but it seems that the threat became bigger and more powerful. The newest version of Cerber virus spreads using the same old methods – malicious email campaigns and malvertising. Once it gets into the computer, it starts encrypting files and adds .cerber3 extension to all of them. Then, it leaves a ransom note asking you to pay a ransom. Honestly, the developers have already got lots of money from their victims. So, there is no need to continue sponsoring them. It’s better to remove Cerber3 from your PC immediately.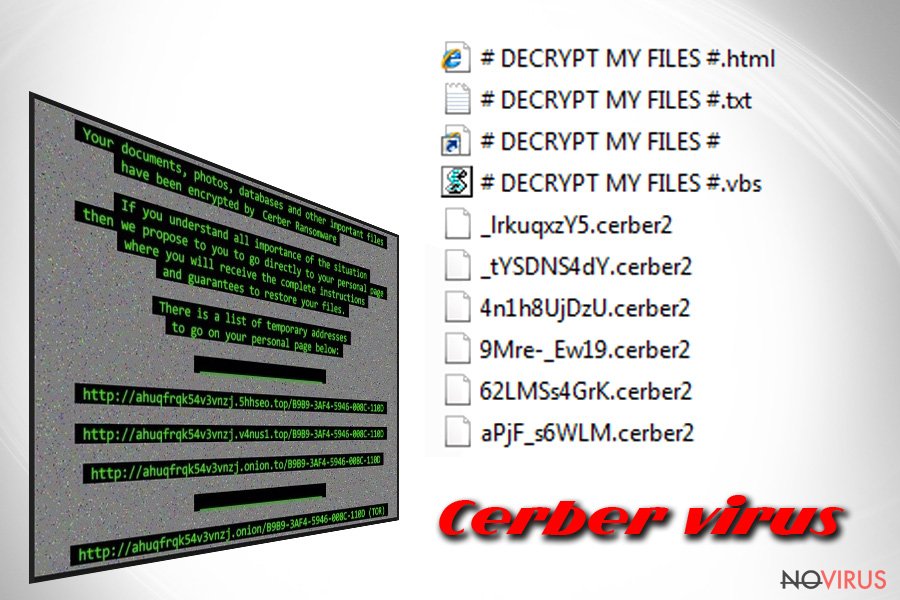
Cerber removal instructions
Practically, there are only two options to get rid of Cerber virus – automatic and manual elimination. We highly recommend you opting for automatic removal since it is time and nerve-saving solution. An anti-spyware program is designed specifically for dealing with aggressive malware, such as trojans, worms and ransomware. Thus, it is able to remove Cerber within a short time.
Moreover, you can be sure that it will not leave any potentially malicious files. There is manual removal option as well. If you feel confident enough, you might try this method. However, keep in mind that it will require utmost precision and patience. After all, when you succeed in eliminating the virus, take care of your data back-up. If you do not intend to keep it on the PC, you might use various data storage domains, such as DVD discs or USB sticks.
Getting rid of Cerber virus. Follow these steps
In-depth guide for the Cerber elimination
Important! →
The elimination guide can appear too difficult if you are not tech-savvy. It requires some knowledge of computer processes since it includes system changes that need to be performed correctly. You need to take steps carefully and follow the guide avoiding any issues created due to improper setting changes. Automatic methods might suit you better if you find the guide too difficult.
Step 1. Launch Safe Mode with Networking
Safe Mode environment offers better results of manual virus removal
Windows 7 / Vista / XP
- Go to Start.
- Choose Shutdown, then Restart, and OK.
- When your computer boots, start pressing the F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) a few times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click the Start button and choose Settings.

- Scroll down to find Update & Security.

- On the left, pick Recovery.
- Scroll to find Advanced Startup section.
- Click Restart now.

- Choose Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.

- Choose 5) Enable Safe Mode with Networking.
Step 2. End questionable processes
You can rely on Windows Task Manager that finds all the random processes in the background. When the intruder is triggering any processes, you can shut them down:
- Press Ctrl + Shift + Esc keys to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes.
- Look for anything suspicious.
- Right-click and select Open file location.

- Go back to the Process tab, right-click and pick End Task.
- Delete the contents of the malicious folder.
Step 3. Check the program in Startup
- Press Ctrl + Shift + Esc on your keyboard again.
- Go to the Startup tab.
- Right-click on the suspicious app and pick Disable.

Step 4. Find and eliminate virus files
Data related to the infection can be hidden in various places. Follow the steps and you can find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive (C: is your main drive by default and is likely to be the one that has malicious files in) you want to clean.
- Scroll through the Files to delete and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Eliminate Cerber using System Restore
-
Step 1: Restart your computer in Safe Mode with Command Prompt
Windows 7 / Vista / XP- Go to Start → Shutdown → Restart → OK.
- As soon as your computer starts, start pressing F8 key repeatedly before the Windows logo shows up.
-
Choose Command Prompt from the list

Windows 10 / Windows 8- Click on the Power button at the Windows login screen, and then press and hold Shift key on your keyboard. Then click Restart.
- Then select Troubleshoot → Advanced options → Startup Settings and click Restart.
-
Once your computer starts, select Enable Safe Mode with Command Prompt from the list of options in Startup Settings.

-
Step 2: Perform a system restore to recover files and settings
-
When the Command Prompt window appears, type in cd restore and press Enter.

-
Then type rstrui.exe and hit Enter..

-
In a new window that shows up, click the Next button and choose a restore point that was created before the infiltration of Cerber and then click on the Next button again.


-
To start system restore, click Yes.

-
When the Command Prompt window appears, type in cd restore and press Enter.
It is strongly recommended to take precautions and secure your computer from malware attacks. To protect your PC from Cerber and other dangerous viruses, you should install and keep a powerful malware removal tool, for instance, FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes.
How to prevent from getting ransomware
Prevent the government from spying on you
As there is a growing debate in government about collecting users' data and spying on citizens, you should take a closer look at this issue and find out what shady ways of gathering information can be used to collect information about you. You need to browse anonymously if you want to avoid any government-initiated spying and tracking of information.
You can enjoy secure internet browsing and minimize the risk of intrusion into your system if you use Private Internet Access VPN program. This VPN application creates a virtual private network and provides access to the required data without any content restrictions.
Control government and other third party access to your data and ensure safe web browsing. Even if you do not engage in illegal activities and trust your ISP, we recommend being careful about your security. You should take extra precautions and start using a VPN program.
Reduce the threat of viruses by backing up your data
Due to their own careless behavior, computer users can suffer various losses caused by cyber infections. Viruses can affect the functionality of the software or directly corrupt data on your system by encrypting it. These problems can disrupt the system and cause you to lose personal data permanently. There is no such threat if you have the latest backups, as you can easily recover lost data and get back to work.
It is recommended to update the backups in parallel each time the system is modified. This way, you will be able to access the latest saved data after an unexpected virus attack or system failure. By having the latest copies of important documents and projects, you will avoid serious inconveniences. File backups are especially useful if malware attacks your system unexpectedly. We recommend using the Data Recovery Pro program to restore the system.







