Uninstall Razy virus (Uninstall Instructions) - Sep 2016 updated
Razy virus Removal Guide
Description of Razy ransomware virus
Characteristics of Razy ransomware virus
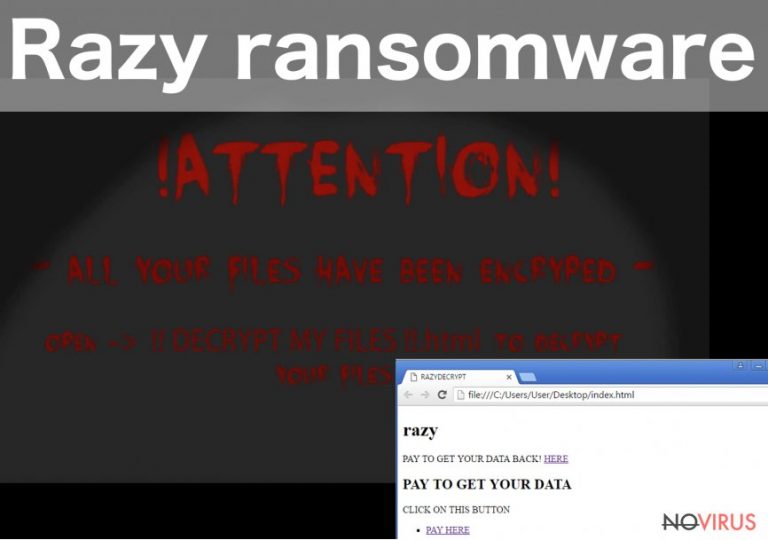
Razy virus is a new member of the ransomware viruses’ family. Once this file encrypting virus manages to get into the computer, it can encode all types of files and even some programs. Unfortunately, it can block antivirus programs too, so, virus elimination might be a tricky task. After successful data encryption, victims will find three new files on their desktops: css.vbs, index.html, and razy.jpg. Ransomware type viruses usually leave a ransom note with explanation what have happened to user’s data and how to pay the ransom. Surprisingly, the creators of Razy ransomware virus just leave corrupted links that are supposed to lead to the payment site, but they actually lead nowhere. It’s a quite strange characteristic because hackers always leave victims one solution to recover their files – paying the ransom. But it seems taking payments is not interesting for the creators. Generally, ransomware viruses are created for money making, but according to Razy developers, the virus was created only for educational purposes. It’s a pretty nice idea to teach people about viruses, but it would be lovely to give people a chance to recover their files too. If you have encountered the virus, you should consider Razy removal. Virus elimination won’t restore your data, but you’ll protect new files from the encryption.
Virus encodes the files with AES encryption. It uses public and private keys. The public key is used for encryption, and the private one is necessary for decryption. Unfortunately, there are no private keys that are required for restoring the files encrypted by Razy virus. One of the options is to recover your data from backups. However, many computer users do not make backup copies regularly. So, the ransomware attack becomes an unpleasant lesson that explains why making copies are important. If you are the unlucky one, who doesn’t have backups, you can try to encrypt your files using tools that are offered by R-Studio or Kaspersky. Don’t forget that before thinking about data recovery you have to remove Razy. FortectIntego might help you to get rid of the virus and protect your PC from further infections.
Unfortunately, Razy malware is not the only threat that is lurking online. Virus researchers found out the new version of this malware – Razy 5.0 ransomware virus. This version of the virus spreads with PDF files. Victims, who have opened the infected file, were delivered a message ‘Error on PDF file.’ Once this warning popped up, the virus has already started encrypting all files located on the computer. This time, the creators of the virus clearly ask to pay the ransom, but we do not recommend spending your money. Nevertheless, it might seem the only way to recover your files. When you realise that your computer was infected with ransomware, you should think about virus removal only. There’s a huge possibility that IT specialists are creating a free decryption tool, and you’ll be able to use it soon. Meanwhile, you can recover your files from backups.
How to protect my PC from ransomware viruses?
If you are one of the lucky computer users, who haven’t encountered Razy ransomware virus yet, you should take some precautions that are necessary for protecting your computer. First of all, we recommend installing a strong antivirus program that will protect your computer. However, you should regularly update it and still be careful with other activities online. For example, avoid file-sharing domains and don’t download programs or their updates from questionable websites. Also, stay away from aggressive and suspicious ads, because they might be a part of malvertising campaign. Lastly, one of the most common ways how ransomware spreads is via malicious email campaigns. The crooks are really creative and persuasive, so they can easily trick even the smartest users into opening the attached file. Once they do it, the virus enters computers’ system, and the problems begin.
Elimination of Razy virus
When victims receive a message that their computer was infected and Razy ransomware encrypted all their files, they usually freak out and start panicking. Of course, ransomware attack is not a pleasant life event, but you shouldn’t let your emotions take control. You have to stay calm and concentrate on virus elimination. First of all, you should try to remove Razy with the help of professional malware programs, such as FortectIntego or SpyHunter 5Combo Cleaner. The virus is capable of blocking antivirus programs, so if this happens to you, follow our manual instructions provided at the end of the article. Do not consider manual Razy removal in any other case. Ransomware viruses are dangerous and hard to remove. It’s better to let professional tools to do this job.
Getting rid of Razy virus. Follow these steps
In-depth guide for the Razy elimination
Important! →
The elimination guide can appear too difficult if you are not tech-savvy. It requires some knowledge of computer processes since it includes system changes that need to be performed correctly. You need to take steps carefully and follow the guide avoiding any issues created due to improper setting changes. Automatic methods might suit you better if you find the guide too difficult.
Step 1. Launch Safe Mode with Networking
Safe Mode environment offers better results of manual virus removal
Windows 7 / Vista / XP
- Go to Start.
- Choose Shutdown, then Restart, and OK.
- When your computer boots, start pressing the F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) a few times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click the Start button and choose Settings.

- Scroll down to find Update & Security.

- On the left, pick Recovery.
- Scroll to find Advanced Startup section.
- Click Restart now.

- Choose Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.

- Choose 5) Enable Safe Mode with Networking.
Step 2. End questionable processes
You can rely on Windows Task Manager that finds all the random processes in the background. When the intruder is triggering any processes, you can shut them down:
- Press Ctrl + Shift + Esc keys to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes.
- Look for anything suspicious.
- Right-click and select Open file location.

- Go back to the Process tab, right-click and pick End Task.
- Delete the contents of the malicious folder.
Step 3. Check the program in Startup
- Press Ctrl + Shift + Esc on your keyboard again.
- Go to the Startup tab.
- Right-click on the suspicious app and pick Disable.

Step 4. Find and eliminate virus files
Data related to the infection can be hidden in various places. Follow the steps and you can find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive (C: is your main drive by default and is likely to be the one that has malicious files in) you want to clean.
- Scroll through the Files to delete and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Eliminate Razy using System Restore
-
Step 1: Restart your computer in Safe Mode with Command Prompt
Windows 7 / Vista / XP- Go to Start → Shutdown → Restart → OK.
- As soon as your computer starts, start pressing F8 key repeatedly before the Windows logo shows up.
-
Choose Command Prompt from the list

Windows 10 / Windows 8- Click on the Power button at the Windows login screen, and then press and hold Shift key on your keyboard. Then click Restart.
- Then select Troubleshoot → Advanced options → Startup Settings and click Restart.
-
Once your computer starts, select Enable Safe Mode with Command Prompt from the list of options in Startup Settings.

-
Step 2: Perform a system restore to recover files and settings
-
When the Command Prompt window appears, type in cd restore and press Enter.

-
Then type rstrui.exe and hit Enter..

-
In a new window that shows up, click the Next button and choose a restore point that was created before the infiltration of Razy and then click on the Next button again.


-
To start system restore, click Yes.

-
When the Command Prompt window appears, type in cd restore and press Enter.
It is strongly recommended to take precautions and secure your computer from malware attacks. To protect your PC from Razy and other dangerous viruses, you should install and keep a powerful malware removal tool, for instance, FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes.
How to prevent from getting ransomware
Prevent the government from spying on you
As there is a growing debate in government about collecting users' data and spying on citizens, you should take a closer look at this issue and find out what shady ways of gathering information can be used to collect information about you. You need to browse anonymously if you want to avoid any government-initiated spying and tracking of information.
You can enjoy secure internet browsing and minimize the risk of intrusion into your system if you use Private Internet Access VPN program. This VPN application creates a virtual private network and provides access to the required data without any content restrictions.
Control government and other third party access to your data and ensure safe web browsing. Even if you do not engage in illegal activities and trust your ISP, we recommend being careful about your security. You should take extra precautions and start using a VPN program.
Recover files damaged by a dangerous malware attack
Despite the fact that there are various circumstances that can cause data to be lost on a system, including accidental deletion, the most common reason people lose photos, documents, videos, and other important data is the infection of malware.
Some malicious programs can delete files and prevent the software from running smoothly. However, there is a greater threat from the dangerous viruses that can encrypt documents, system files, and images. Ransomware-type viruses focus on encrypting data and restricting users’ access to files, so you can permanently lose personal data when you download such a virus to your computer.
The ability to unlock encrypted files is very limited, but some programs have a data recovery feature. In some cases, the Data Recovery Pro program can help recover at least some of the data that has been locked by a virus or other cyber infection.







