Uninstall Gmail virus (Virus Removal Tutorial) - Free Removal Guide
Gmail virus Removal Guide
Description of Gmail virus
Gmail virus emerges in new forms

Gmail virus defines an entire ensemble of adware, malware, trojans, and computer trojans, and online scams associated with the email service. One of the most frequent forms of the online felony is the malware which spreads in the form of email attachments.
It is not surprising that this email service is targetted continuously by cyber fraudsters. Gmail, alternatively known as Gmail Mail, unifies more than 1 billion active users. Furthermore, since there are a number of gullible users, especially the ones which have not enabled two-step verification yet, new opportunities for felons appear.
They tend to target unsuspecting users with corrupted .js, .zip, .doc email attachments. Unfortunately, the malware delivered through this method happens to be no ordinary computer virus, but crypto-malware. Luckily, Google has declared the campaign to ban .js email attachments.
Nonetheless, felons discover new deception strategies. Some of them wrap the .js file with multiple .zip folders. Racketeers tend to employ more cunning and insidious strategies. In May, they launched the Google Docs scam campaign. Gmail users received the invitation supposedly sent by their contacts to review the Google Docs file.
After clicking the link, users were misguided to a fake security page and asked to grant the compromised application access to your email account. Naturally, allowing it would not only compromise the privacy and security of the account but send the invitation with the malicious attachment to your contacts.
As in other click-fraud types, clicking the link activates the malware. At that time, computer worm wreaked havoc. However, malware authors do not limit themselves just to this form of a virus.
Fraudsters also manifest their mastery by disguising the malicious URL. There have been scams when netizens received a sophisticated written message. However, the attachment hid the link to a phishing site. After entering the login details into the hoax Gmail site, malware authors infiltrated the account.
Note that you may look through such phishing sites as they contain or lack key elements of the legitimate Gmail log-in page. Moreover, the font of the letters might be smaller or bigger.
If you suspect that the unauthorised access to the account has occurred or you are getting redirected to an odd log-in page, it is high time you initiated Gmail virus removal. Due to its obscure form, automatic elimination method might be more efficient. FortectIntego or Malwarebytes will come in handy in this situation. 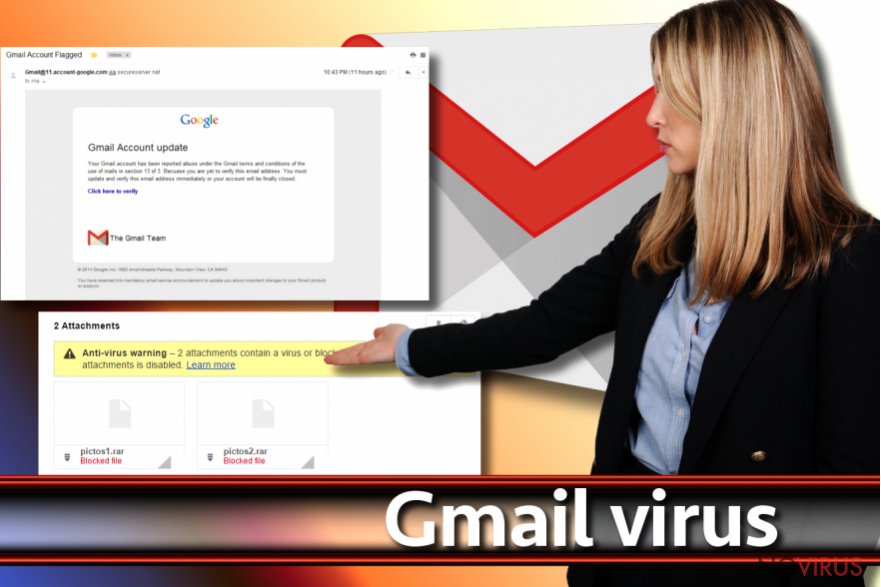
Virus prevention options
While the infiltration techniques are getting more sophisticated, there are still ways how to counterattack them. Surprisingly, some of Gmail scams might be technically sophisticated, but they work in significantly weak factor – human curiosity. Besides the guide elaborating how to determine an email virus, take note of the below advice:
- inspect the URL domain name when logging in. It should be https://accounts.google.com(..) and not some random URL.
- do not upgrade or take any action suggested by pop-up alerts emerging in new tabs while browsing the Web
- restrain from opening any email, let along email attachments, which is supposedly sent by the official institution. Expect for the surge in Gmail scams during the year holidays, Black Friday and similar occasions.
- Double-check the sender of the message with the attachment. Even it is sent by one of your contacts, inquire them directly. They may not be aware that their account is sending messages compromised with a computer worm.
FAQ about Gmail malware
Below you will find a couple of popular questions which might answer your questions and dispel the suspicions.
Question 1. I believe my account is hacked as my contact people are getting messages which I have not sent. How can I stop the virus from the further activity?
Answer: Indeed, it is one of the key indicators which imply the compromised account. Another factor suggesting such conclusion is the absence of the Sent messages record. In order banish the perpetrator from your account, you should perform Gmail Security Checkup and run the system scan.
Question 2. I can no longer sign in to my account. Is there any way to recover my account?
Answer. First of all, you might attempt to recover the account by resetting the password. It is a much easier option if you have enabled two-step verification.
In case the perpetrator has managed to change the recovery phone number and other account recovery details, fill Google Account Recovery form. Google Customer service will be able to recover the account for you.
In addition, the unauthorised access might have occurred as a result of remote access. In order to detect any keylogger, trojan or rootkit activity, you may use anti-rootkit programs. For instance, Malwarebytes offers such program.
Question 3. I extracted the Gmail attachment which turned out to hide ransomware. All my files are encrypted. After all, do Gmail virus filters really work?
Answer. As mentioned before, felons have found ways how to bypass security measures. Thus, placing the .js file in a .zip folder will allow the infection escape the detection.
In order to remove ransomware and recover encoded files, you should run the scan with anti-malware utilities. Our above-suggested tools are able to deal with such infection as well. More information about ransomware and their prevention methods is delivered in the Viruses section.
As for data recovery, there are decrypters released for some of crypto-malware threats. In their absence, Data Recovery Pro or Shadow Explorer might be of assistance.
Ways to distribute malware
Fraudsters discover new techniques to entrap users in their deception. Unfortunately, some of them are indeed elaborate and persuasive. You should treat every message received from an official institution, be it Serious Organized Crime Agency or CCT.
By employing the authority of these institutions, cyber criminals may convince victims to open the files with embedded macro scripts. Luckily, latest Windows versions disable macro settings by default. Thus, such files might ask you to enable them. In the case, such message is genuine, note that the institutions do not attach hidden or zipped files.
Alternatively, do not rush to reset the password if you receive the message about your account being compromised. Inspect the notification and look for typos, grammar and style mistakes. Verify the sender is necessary. Clicking such redirect link may only divert you to a phishing site.
Furthermore, treat every Google Docs invitation with cautiousness as well. A computer worm or trojan might disguise within it. Now let us move on the section which discusses ways to remove Gmail virus.
Eliminate Gmail virus
Depending on what form of Gmail malware you are dealing with, elimination methods differ as well. If you receive a suspicious email, do not open any attachments or click on links without verifying the identity of a sender. You can also report the issue to Google Customer Service.
You can also reset the browser to remove Gmail virus web scripts, especially if you are constantly redirected to a fake site. In case you are dealing with the ransomware version of the virus, perform Gmail virus removal. Use anti-spyware tools to speed up the process. In case the malware forcefully shuts down security applications, reboot the system in Safe Mode.
Getting rid of Gmail virus. Follow these steps
In-depth guide for the Gmail elimination
This functionality will grant you partial access to the operating system. Then, you will be able to bypass Gmail malware activity and launch a virus-fighting utility.
Important! →
The elimination guide can appear too difficult if you are not tech-savvy. It requires some knowledge of computer processes since it includes system changes that need to be performed correctly. You need to take steps carefully and follow the guide avoiding any issues created due to improper setting changes. Automatic methods might suit you better if you find the guide too difficult.
Step 1. Launch Safe Mode with Networking
Safe Mode environment offers better results of manual virus removal
Windows 7 / Vista / XP
- Go to Start.
- Choose Shutdown, then Restart, and OK.
- When your computer boots, start pressing the F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) a few times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click the Start button and choose Settings.

- Scroll down to find Update & Security.

- On the left, pick Recovery.
- Scroll to find Advanced Startup section.
- Click Restart now.

- Choose Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.

- Choose 5) Enable Safe Mode with Networking.
Step 2. End questionable processes
You can rely on Windows Task Manager that finds all the random processes in the background. When the intruder is triggering any processes, you can shut them down:
- Press Ctrl + Shift + Esc keys to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes.
- Look for anything suspicious.
- Right-click and select Open file location.

- Go back to the Process tab, right-click and pick End Task.
- Delete the contents of the malicious folder.
Step 3. Check the program in Startup
- Press Ctrl + Shift + Esc on your keyboard again.
- Go to the Startup tab.
- Right-click on the suspicious app and pick Disable.

Step 4. Find and eliminate virus files
Data related to the infection can be hidden in various places. Follow the steps and you can find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive (C: is your main drive by default and is likely to be the one that has malicious files in) you want to clean.
- Scroll through the Files to delete and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Eliminate Gmail using System Restore
-
Step 1: Restart your computer in Safe Mode with Command Prompt
Windows 7 / Vista / XP- Go to Start → Shutdown → Restart → OK.
- As soon as your computer starts, start pressing F8 key repeatedly before the Windows logo shows up.
-
Choose Command Prompt from the list

Windows 10 / Windows 8- Click on the Power button at the Windows login screen, and then press and hold Shift key on your keyboard. Then click Restart.
- Then select Troubleshoot → Advanced options → Startup Settings and click Restart.
-
Once your computer starts, select Enable Safe Mode with Command Prompt from the list of options in Startup Settings.

-
Step 2: Perform a system restore to recover files and settings
-
When the Command Prompt window appears, type in cd restore and press Enter.

-
Then type rstrui.exe and hit Enter..

-
In a new window that shows up, click the Next button and choose a restore point that was created before the infiltration of Gmail and then click on the Next button again.


-
To start system restore, click Yes.

-
When the Command Prompt window appears, type in cd restore and press Enter.
It is strongly recommended to take precautions and secure your computer from malware attacks. To protect your PC from Gmail and other dangerous viruses, you should install and keep a powerful malware removal tool, for instance, FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes.
How to prevent from getting malware
Prevent the government from spying on you
As there is a growing debate in government about collecting users' data and spying on citizens, you should take a closer look at this issue and find out what shady ways of gathering information can be used to collect information about you. You need to browse anonymously if you want to avoid any government-initiated spying and tracking of information.
You can enjoy secure internet browsing and minimize the risk of intrusion into your system if you use Private Internet Access VPN program. This VPN application creates a virtual private network and provides access to the required data without any content restrictions.
Control government and other third party access to your data and ensure safe web browsing. Even if you do not engage in illegal activities and trust your ISP, we recommend being careful about your security. You should take extra precautions and start using a VPN program.
Recover files damaged by a dangerous malware attack
Despite the fact that there are various circumstances that can cause data to be lost on a system, including accidental deletion, the most common reason people lose photos, documents, videos, and other important data is the infection of malware.
Some malicious programs can delete files and prevent the software from running smoothly. However, there is a greater threat from the dangerous viruses that can encrypt documents, system files, and images. Ransomware-type viruses focus on encrypting data and restricting users’ access to files, so you can permanently lose personal data when you download such a virus to your computer.
The ability to unlock encrypted files is very limited, but some programs have a data recovery feature. In some cases, the Data Recovery Pro program can help recover at least some of the data that has been locked by a virus or other cyber infection.







