Uninstall DoubleLocker virus (Free Removal Guide) - Virus Removal Tutorial
DoubleLocker virus Removal Guide
Description of DoubleLocker virus
DoubleLocker is the ransomware for Android: it changes the PIN code and asks for a ransom
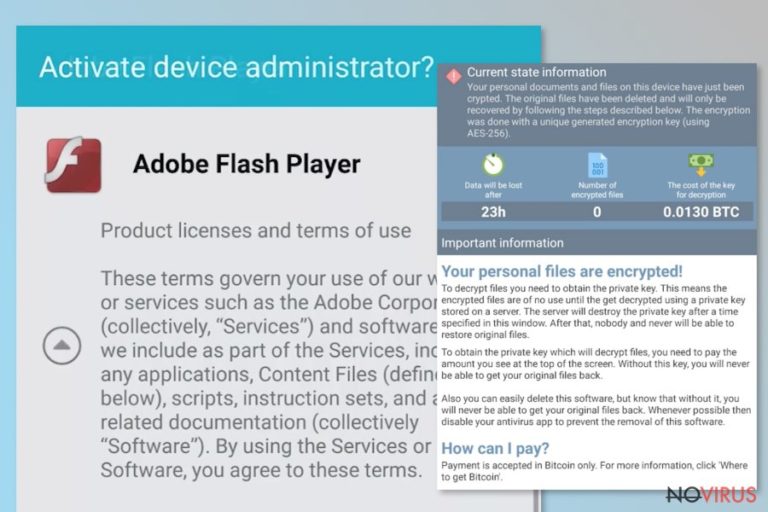
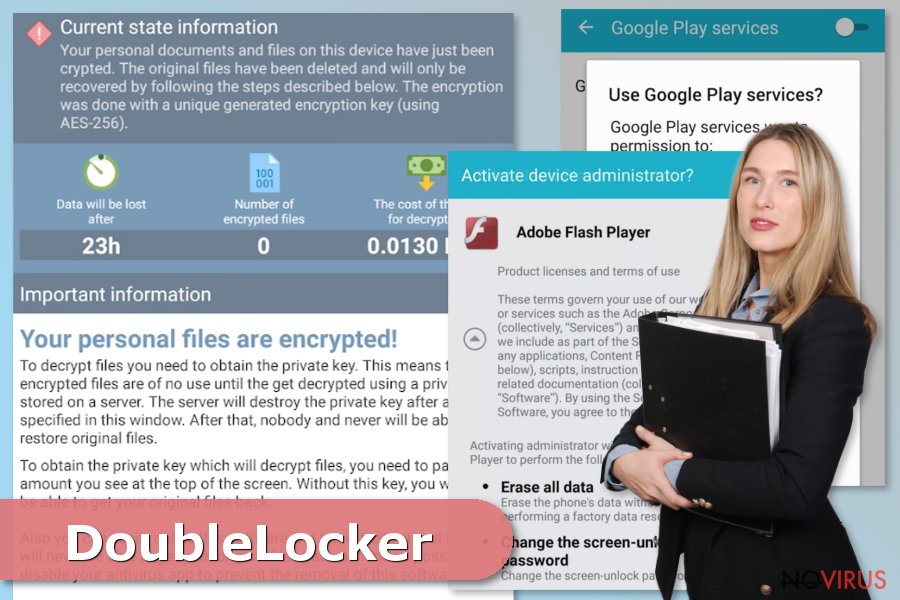
DoubleLocker virus is a ransomware that targets Android device users. Users should be extremely careful when installing Adobe Flash player updates because this Android virus tends to pose as one. The modus operandi of malware consists of two stages: firstly it tries to steal victim’s PayPal as well as bank account login details and later encode all files using cryptography algorithms. During the encryption, the ransomware appends a .cryeye extension to target files.
The deceptive program locks the mobile device and demands to pay the ransom. It clearly functions as a mobile extortion tool that takes victim's device and data stored on it hostage in exchange for a certain sum of money. It is evident that malware has features of the banking trojan and file-encrypting virus, not to mention that it might get complicated to remove DoubleLocker.
Cyber researchers state that it is the first example of Android ransomware that misuses accessibility services on Android OS. As we previously said, the virus spreads in the form of a fake update, which, once launched, requests user's permission to activate an accessibility service under the name 'Google Play Service.'
Such trick easily forces inexperienced computer users to give the malware an approval to launch the malicious payload. Therefore, if you unknowingly allowed this intruder to infect your mobile device, remove DoubleLocker virus using Malwarebytes or another mobile-friendly security software. Below, you can see a brief summary of virus' modus operandi:
- The activity of the ransomware is performed stealthily; thus users who installed fake Adobe Flash update are not aware of it.
- However, each time the victim clicks the home button, crypto-malware gets activated, and the device gets locked again.
- The victims lose access to their mobile phones and valuable data because DoubleLocker virus changes the PIN.
- Additionally, the malicious virus isn't designed to save the new randomly generated PIN or send it fraudsters; therefore it is impossible to find out what it is. The only ones who can access the device and reset the code are the authors of this malicious Android ransomware.
- The virus encrypts valuable data, photos, and information using the same technique used to encrypt military-grade secrets and demands to pay the ransom within 24 hours. Interestingly, just like regular PC ransomware, Double Locker appends .cryeye file extension to corrupted records.
Clearly, authors of the malicious virus want to receive the money transfer as soon as possible, so they promise to trash victim's data after a day in case the victim decides not to pay the ransom. However, trusting fraudsters would be a bad idea.
Therefore, we recommend you to take actions regarding DoubleLocker removal. In case you were using an online data storage service, you can try to recover your files from it. However, we must remind you that any steps regarding data recovery should be taken only after deleting the ransomware from your device.
You can avoid the attack by installing updates only from verified developers
We want to emphasize that Android ransomware spreads as a fake Adobe Flash update on the suspicious websites. Therefore, our IT specialists encourage users to only use Google Play Store for new app installations or upgrades. However, the suggested App Store is known to provide malicious applications from time to time, so we strongly recommend you to read app reviews before installing them. In addition, adding a proper security software to your device is just a must, too.
Finally, to protect your mobile against malware, security experts suggest following safe browsing rules and avoiding shady-looking content online (such as aggressive ads or low-reputation websites)/ Even an accidental click on a corrupted link can trigger the installation of various types of adware, spyware, etc. Thus, do not open suspicious attachments in your email or other social networking platforms and never download unauthorized system tools promoted in pop-ups.
Guidelines to remove DoubleLocker malware from Android
It might be hard to perform DoubleLocker removal if your Android device is non-rooted. In this case, firstly you have to reset the phone to the factory state in order to unlock it. Afterwards, it is possible to get rid of the ransomware using a reliable security software, such as Malwarebytes.
If your mobile has enabled debugging model and is under attack, you can use Android Debug Bridge (ADB) tool. This way you do not have to reset the phone to factory state to unlock it and remove DoubleLocker virus. Shortly after your PIN is reset, you can uninstall the malware using any kind of anti-malware software compatible with the Android operating system.
How to prevent from getting malware
A proper web browser and VPN tool can guarantee better safety
As online spying becomes an increasing problem, people are becoming more interested in how to protect their privacy. One way to increase your online security is to choose the most secure and private web browser. But if you want complete anonymity and security when surfing the web, you need Private Internet Access VPN service. This tool successfully reroutes traffic across different servers, so your IP address and location remain protected. It is also important that this tool is based on a strict no-log policy, so no data is collected and cannot be leaked or made available to first or third parties. If you want to feel safe on the internet, a combination of a secure web browser and a Private Internet Access VPN will help you.
Reduce the threat of viruses by backing up your data
Due to their own careless behavior, computer users can suffer various losses caused by cyber infections. Viruses can affect the functionality of the software or directly corrupt data on your system by encrypting it. These problems can disrupt the system and cause you to lose personal data permanently. There is no such threat if you have the latest backups, as you can easily recover lost data and get back to work.
It is recommended to update the backups in parallel each time the system is modified. This way, you will be able to access the latest saved data after an unexpected virus attack or system failure. By having the latest copies of important documents and projects, you will avoid serious inconveniences. File backups are especially useful if malware attacks your system unexpectedly. We recommend using the Data Recovery Pro program to restore the system.
