Remove Chumsearch.com (Uninstall Guide) - Jan 2018 updated
Chumsearch.com Removal Guide
Description of Chumsearch.com
The main reasons why you should eliminate Chumsearch.com virus immediately
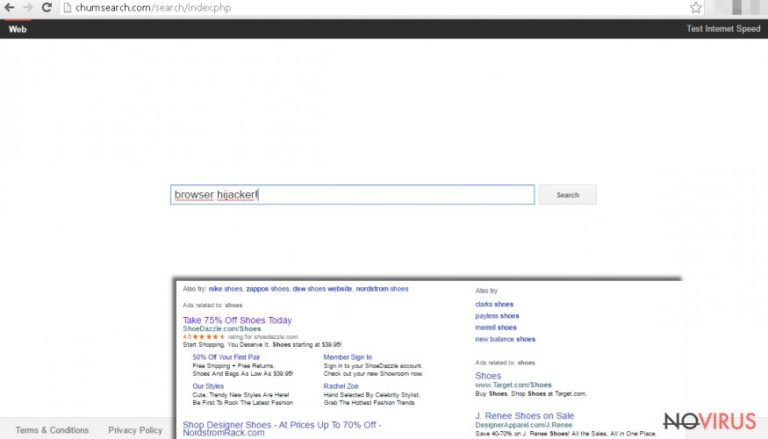
Chumsearch.com virus can hijack all web browsers and modify their settings. Nevertheless, this browser hijacker sneaks into computer’s system silently; users soon notice that they lost control over their browsers. The virus alters browser’s settings and prevents users from resetting them.
After the hijack, virus sets new homepage and default search engine – Chumsearch.com. Browser hijacker is not dangerous itself; however, you should not delay its removal. It can install ‘helper objects,’ various apps or browser extensions, and let dangerous viruses enter computer’s system. So, encountering this browser hijacker might be the start of never-ending computer infections.
It’s better to remove Chumsearch.com as soon as it appears on the screen. We have no doubts that you are willing to get rid of this tool because it causes lots of annoying and potentially dangerous activities. One of the most troubling issues is Chumsearch.com redirect problem.
Browser hijacker initiates constant redirects to various websites. Some of these Internet sites are risky, and you won’t visit them under normal conditions. Users have noticed that virus redirects them to the same websites again and again. This happens, because the creators of the browser hijacker get revenue from generating traffic to sponsored websites.
Delivering sponsored content is the primary purpose of Chumsearch.com virus. It provides different types of advertisements. Unfortunately, most of them are fraudulent and might be a part of a malicious campaign. You will find lots of commercial content in the search results as well. However, the developers claim that Chumsearch.com allows accessing ‘wonderful things’ on the Internet. It’s hard to call suspicious and irrelevant links as ‘wonderful.’ Using this search engine, you can forget about safe browsing.
Talking about safety, we should discuss possible threats to your personal information too. In the Privacy Policy, the developers reveal secrets related to data tracking. Indeed, Chumsearch.com hijacker collects all kinds of information, starting from technical information about your computer and finishing with your browsing habits. This data gathering seems harmless, but the virus might be interested in your private and personal information. So, your email and home address, telephone number, and some passwords might be visible.
Needless to say, they can share the information with third party companies, and they can have some shady purposes. We recommend protecting your personal data by eliminating the virus immediately. Chumsearch.com removal can be completed with a help of FortectIntego.
How does it spread?
The virus sneaks into computer’s system without asking user’s permission directly. The paradox is that users let browser hijacker in when they download and install freeware. Chumsearch.com hijack might have occurred with the latest program that you downloaded from the Internet. You might have installed a program from an unreliable source or used file-sharing services, or you have rushed with the installation process.
The developers add browser hijacker as ‘additional download’ and hide it under ‘Recommended’ or ‘Basic’ installation mode. Indeed, many users make this mistake and accept the offer to install softer using this setup. If you want to avoid potentially unwanted programs, you have to choose ‘Advanced’ or ‘Recommended’ installation mode. Then, you can monitor installation process and stop ‘additional downloads.’
How to remove Chumsearch.com browser hijacker?
Getting rid of the virus might seem like a challenge for many computer users. However, Chum Search is not a real and hazardous virus. It’s just a computer infection which can be removed quickly. The easiest way to remove Chumsearch.com is to use a security program.
If you use reputable and strong anti-malware program, you should update it right now. An outdated version might not be capable of detecting and eliminating virus with all its components from the computer. If you don’t use any program, download one of the programs suggested bellow.
Then, you have to run a full system scan and wait while it completes the task. Additionally, if you want to challenge yourself, you can try manual Chumsearch.com removal. But we have to warn you that this method requires lots of patience and attentiveness because it’s crucial to delete all virus-related components in order to prevent further infections.
You may remove virus damage with a help of FortectIntego. SpyHunter 5Combo Cleaner and Malwarebytes are recommended to detect potentially unwanted programs and viruses with all their files and registry entries that are related to them.
Getting rid of Chumsearch.com. Follow these steps
Uninstall Chumsearch.com in Windows systems
Virus elimination requires finding and eliminating all programs related to this browser hijacker. We recommended looking for these programs: MPlayerX, MessageViewer Toolbar, NicePlayer, SearchProtect, and ValueApps. Delete these programs from your computer without any consideration.
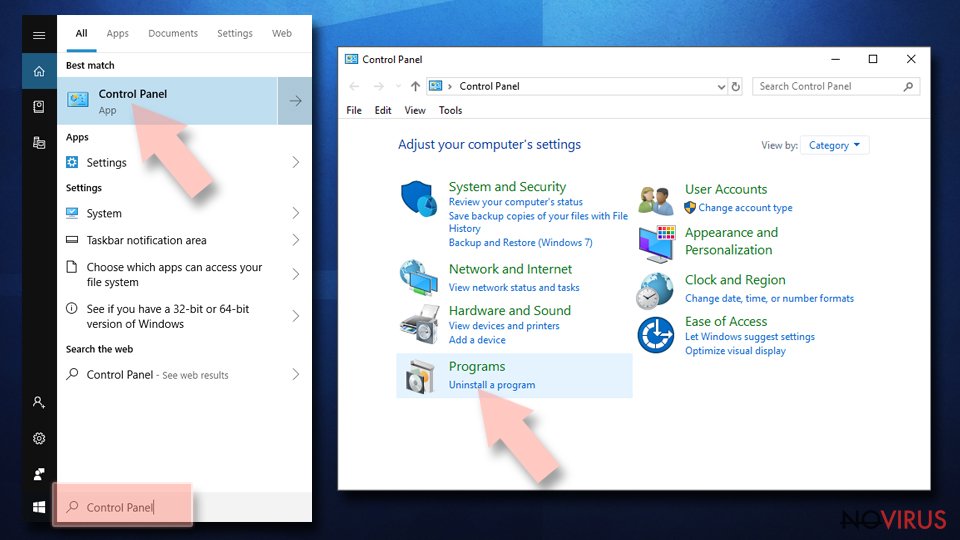
Terminate suspicious programs from Windows 10/8 machines by following these instructions:
- Type Control Panel into Windows search and once the result shows up hit Enter.
- Under Programs, choose Uninstall a program.
- Find components related to suspicious programs.
- Right-click on the application and select Uninstall.
- Click Yes when User Account Control shows up.
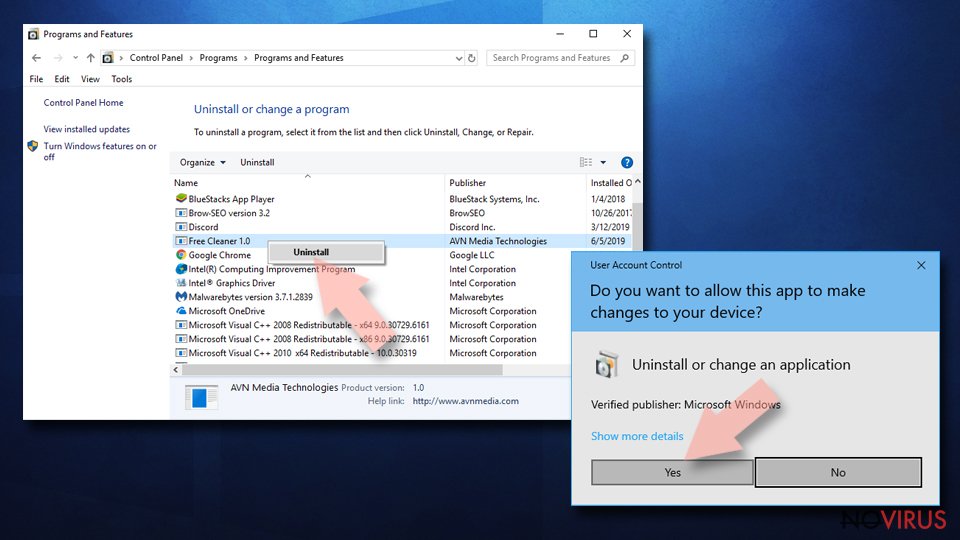
- Wait for the process of uninstallation to be done and click OK.
Windows 7/XP instructions:
- Click on Windows Start and go to Control Panel on the right pane.
- Choose Add/Remove Programs.
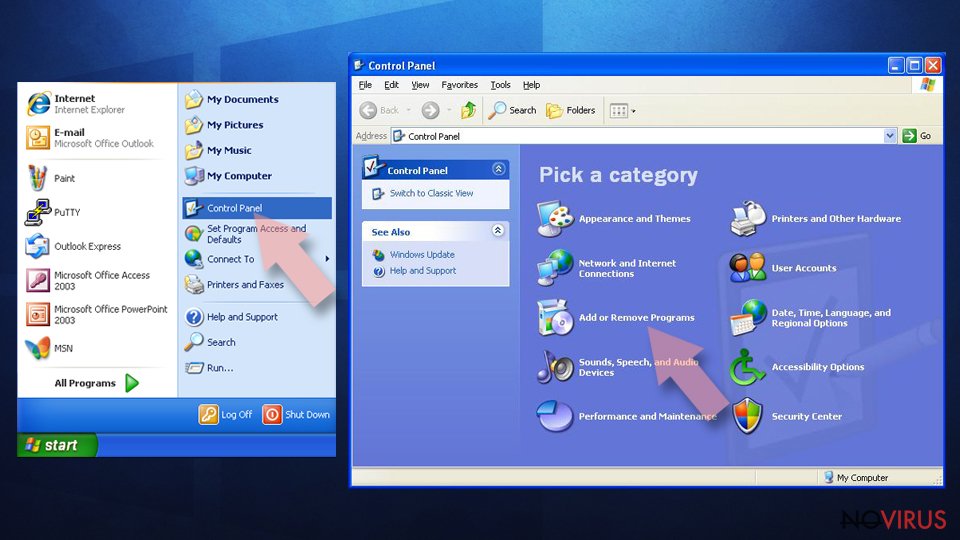
- Select Uninstall a program under Programs in Control Panel.
- Click once on the unwanted application.
- Click Uninstall/Change at the top.
- Confirm with Yes.
- Click OK and finish the removal.
Uninstall Chumsearch.com in Mac OS X system
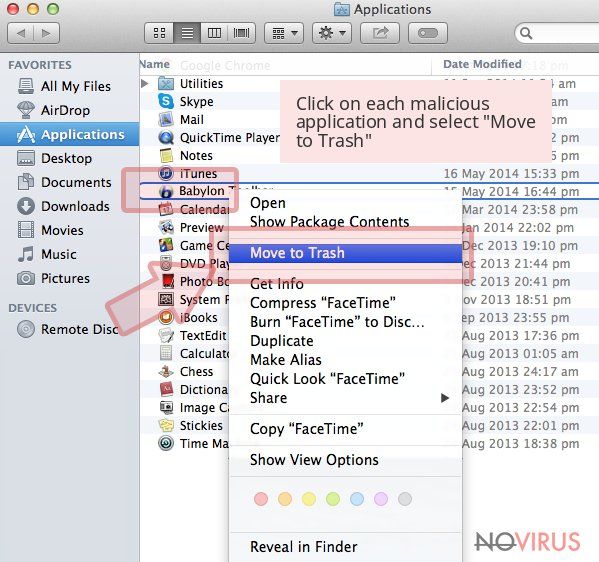
To remove the virus you have to check your Mac OS X for MPlayerX, MessageViewer Toolbar, NicePlayer, SearchProtect, and ValueApps. These programs are related to Chumsearch.com virus. So, you have to uninstall these programs too.
-
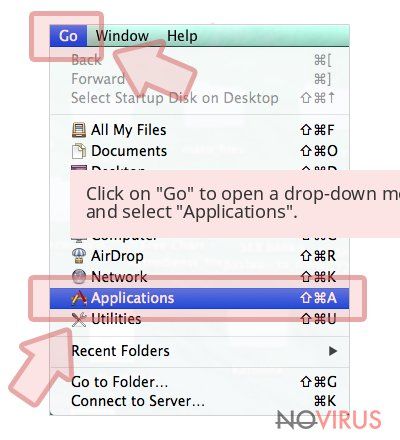
Users who use OS X should click on Go button, which can be found at the top left corner of the screen and select Applications.

-
Wait until you see Applications folder and look for Chumsearch.com or any other suspicious programs on it. Now right click on every of such entries and select Move to Trash.

Delete Chumsearch.com from Mozilla Firefox (FF)
Remove suspicious Firefox extensions:
- Open Mozilla Firefox browser and click on the three horizontal lines at the top-right to open the menu.
- Select Add-ons in the context menu.
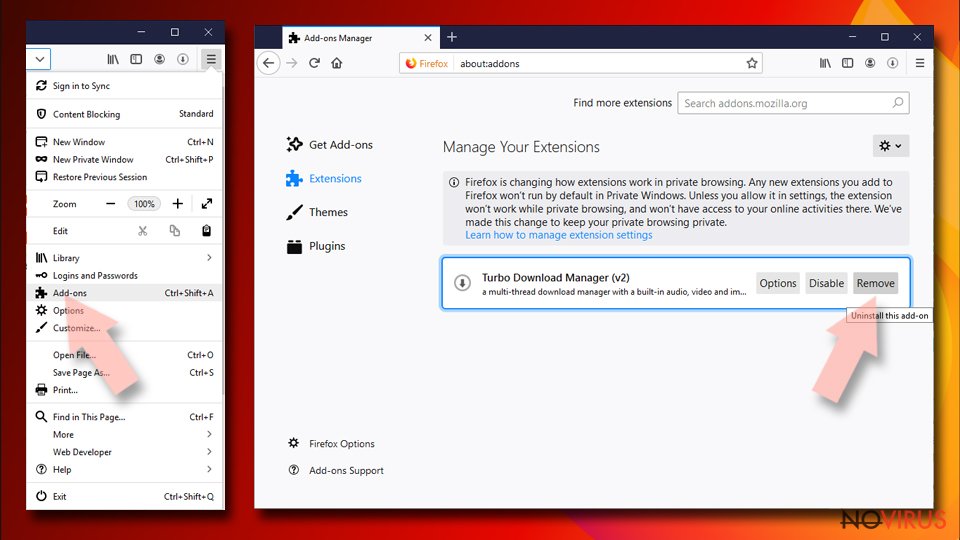
- Choose plugins that are creating issues and select Remove.
Reset the homepage on the browser:
- Click three horizontal lines at the top right corner.
- This time select Options.
- Under Home section, enter your preferred site for the homepage that will open every time you launch Mozilla Firefox.
Clear cookies and site data:
- Click Menu and pick Options.
- Find the Privacy & Security section.
- Scroll down to choose Cookies and Site Data.
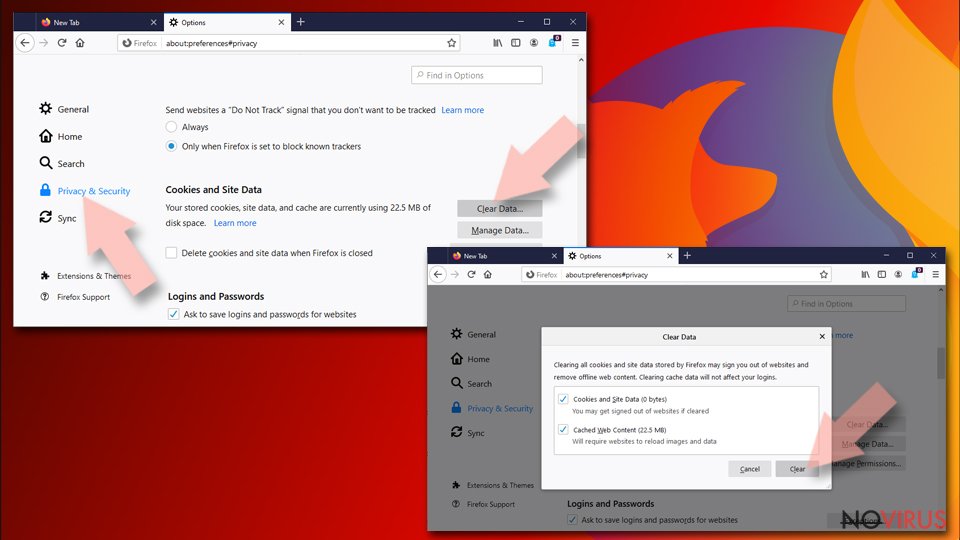
- Click on Clear Data… option.
- Click Cookies and Site Data, Cached Web Content and press Clear.
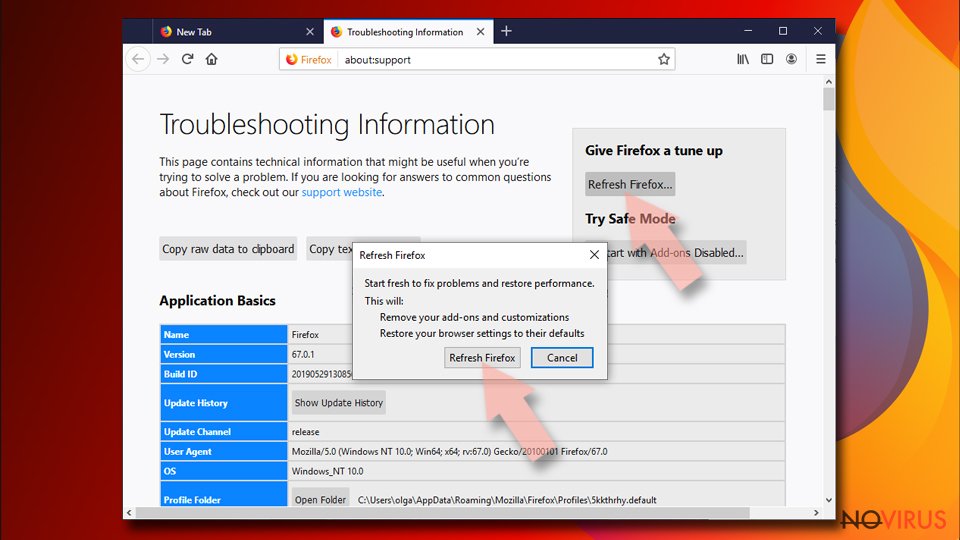
Reset Mozilla Firefox:
If none of the steps above helped you, reset Mozilla Firefox as follows:
- Open Mozilla Firefox and go to the menu.
- Click Help and then choose Troubleshooting Information.
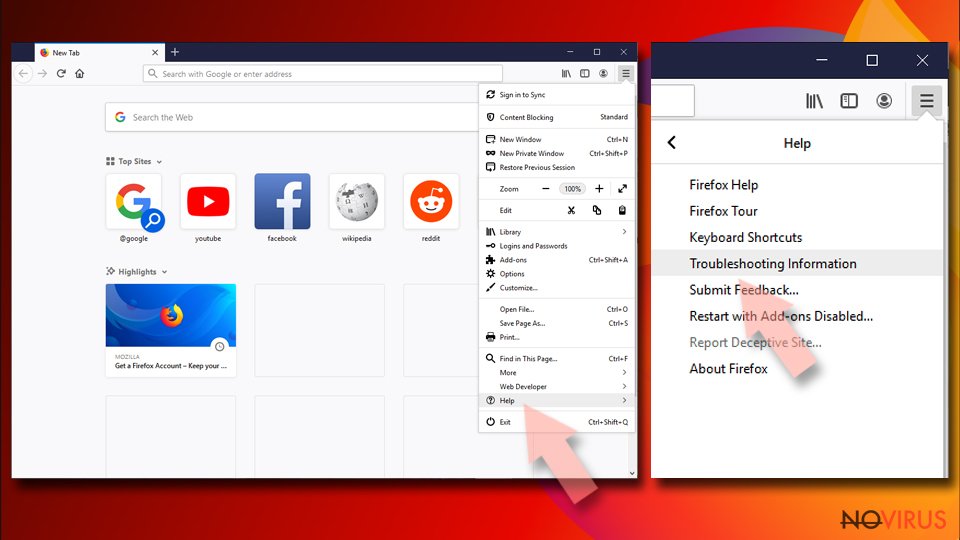
- Locate Give Firefox a tune-up section, click on Refresh Firefox…
- Confirm the action by pressing on Refresh Firefox on the pop-up.
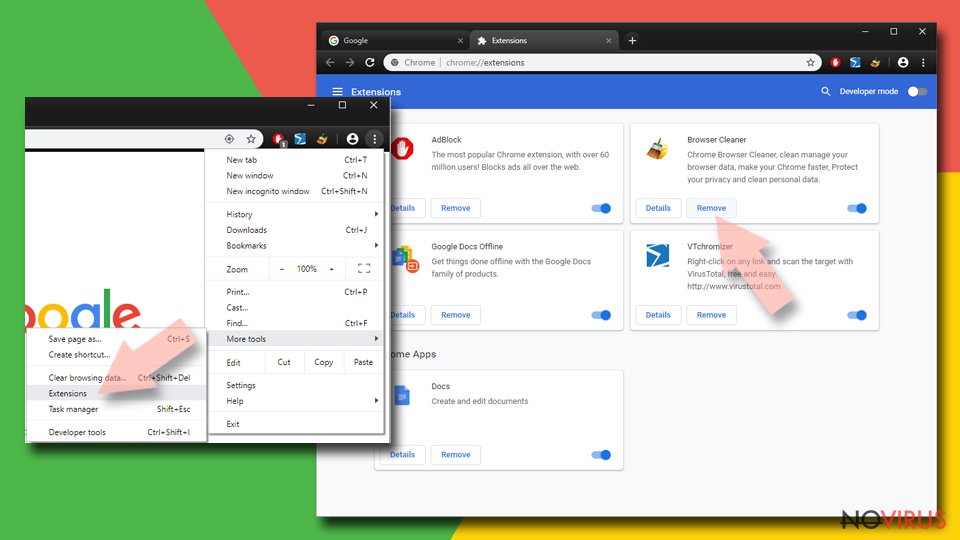
Chrome browser reset
Find and remove suspicious extensions from Google Chrome:
- In Google Chrome, open the Menu by clicking three vertical dots at the top-right corner.
- Select More tools > Extensions.
- Once the window opens, you will see all the installed extensions.
- Find any suspicious add-ons related to any PUP.
- Uninstall them by clicking Remove.
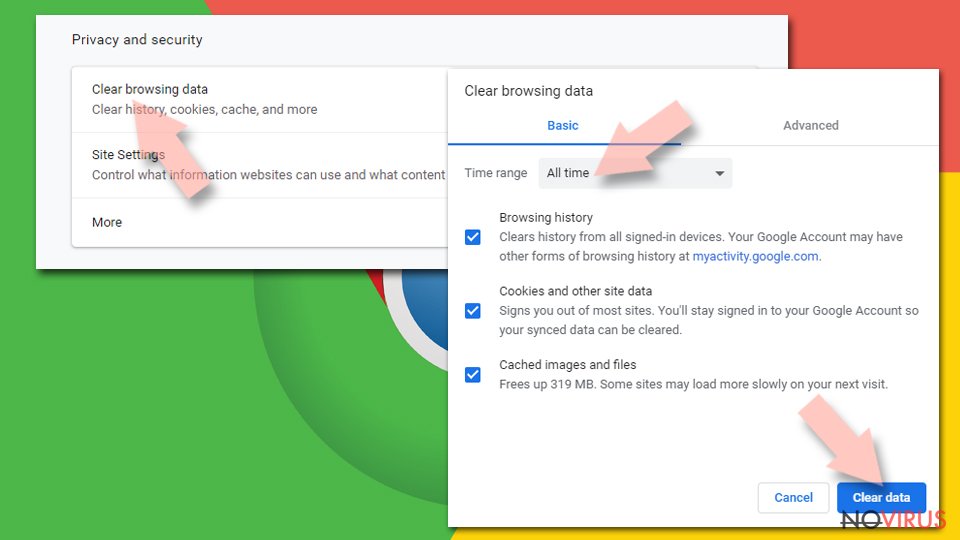
Clear cache and web data from Chrome:
- Click the Menu and select Settings.
- Find Privacy and security section.
- Choose Clear browsing data.
- Select Browsing history.
- Cookies and other site data, also Cached images and files.
- Click Clear data.
Alter settings of the homepage:
- Go to the menu and choose Settings.
- Find odd entries in the On startup section.
- Click on Open a specific or set of pages.
- Then click on three dots and look for the Remove option.
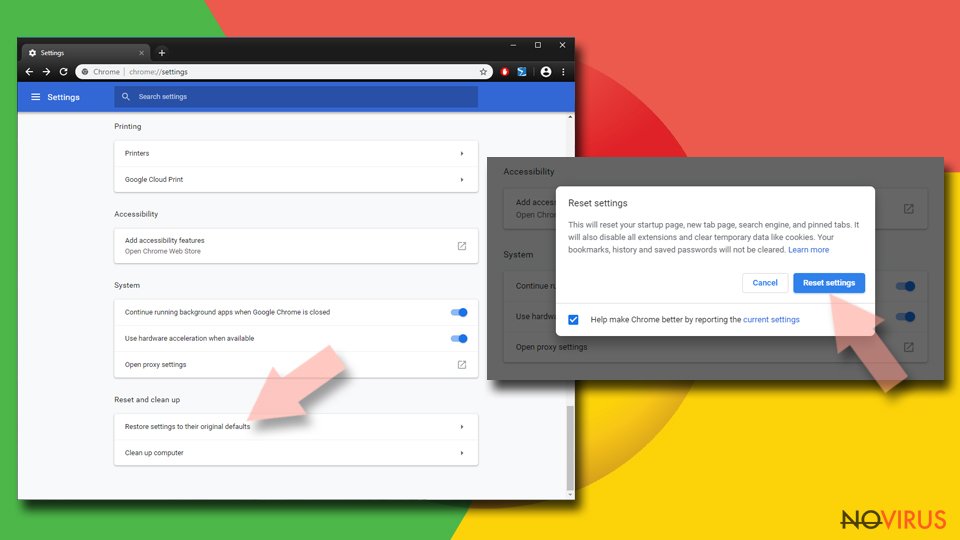
Reset Google Chrome fully:
You might need to reset Google Chrome and properly eliminate all the unwanted components:
- Go to Chrome Settings.
- Once there, scroll down to expand Advanced section.
- Scroll down to choose Reset and clean up.
- Click Restore settings to their original defaults.
- Click Reset settings again.
Delete Chumsearch.com from Safari
Get rid of questionable extensions from Safari:
- Click Safari.
- Then go to Preferences…
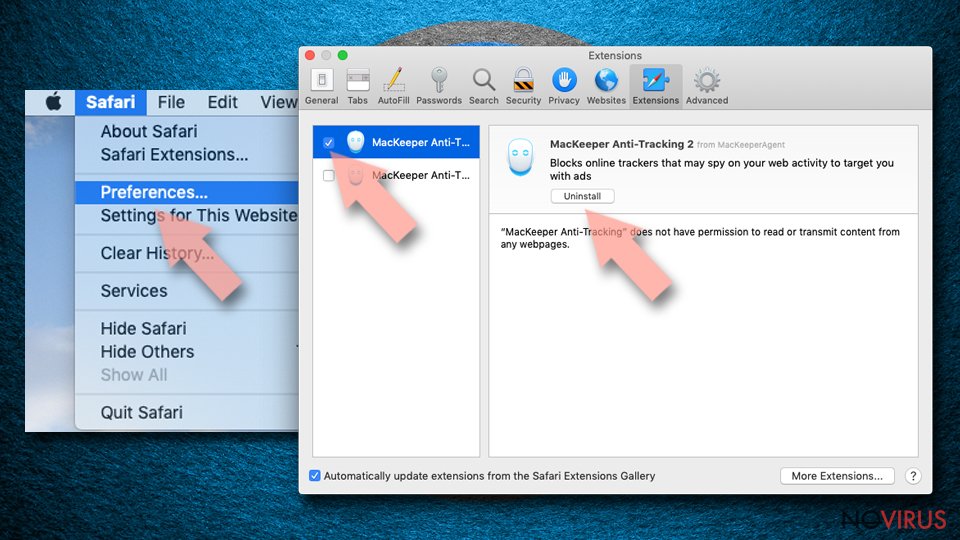
- Choose Extensions on the menu.
- Select the unwanted extension and then pick Uninstall.
Clear cookies from Safari:
- Click Safari.
- Choose Clear History…
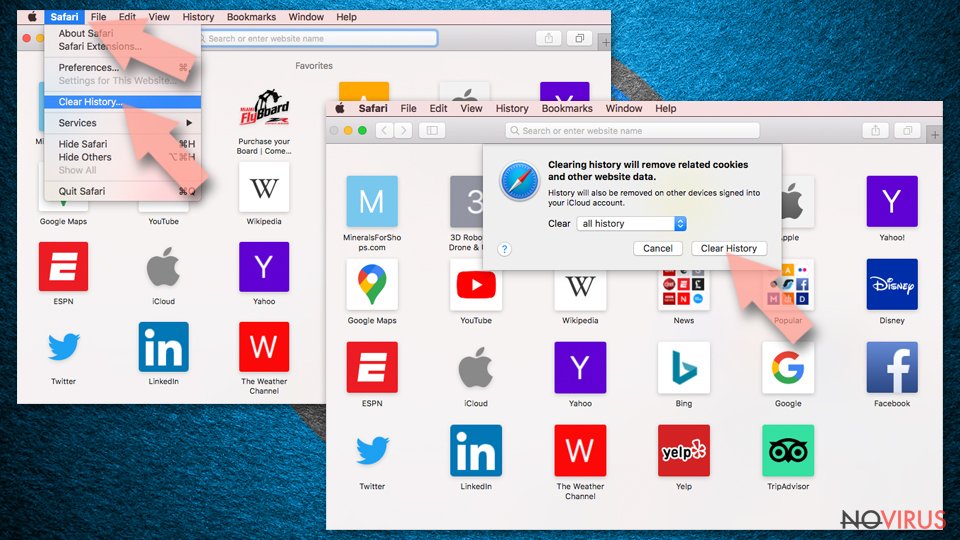
- From the drop-down menu under Clear, find and pick all history.
- Confirm with Clear History.
Reset Safari fully:
- Click Safari and then Preferences…
- Choose the Advanced tab.
- Tick the Show Develop menu in the menu bar.
- From the menu bar, click Develop.
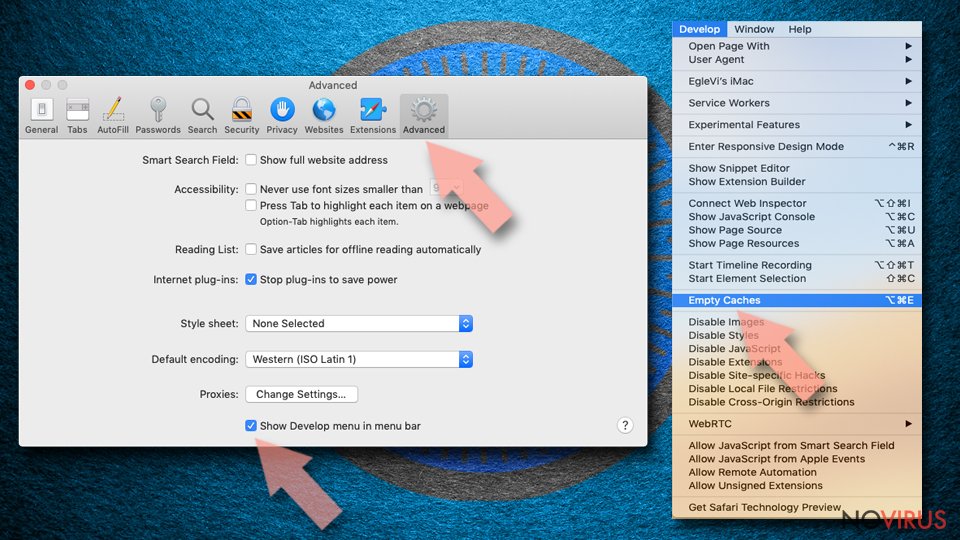
- Then select Empty Caches.
Even if you have completed all the steps above, we still strongly recommend you to scan your computer system with a powerful anti-malware software. It is advisable to do that because an automatic malware removal tool can detect and delete all remains of Chumsearch.com, for instance, its registry keys. The anti-malware program can help you to easily detect and eliminate possibly dangerous software and malicious viruses in an easy way. You can use any of our top-rated malware removal programs: FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes.
How to prevent from getting browser hijacker
Securely connect to your website wherever you are
Sometimes you may need to log in to a content management system or server more often, especially if you are actively working on a blog, website, or different project that needs constant maintenance or that requires frequent content updates or other changes. Avoiding this problem can be easy if you choose a dedicated/fixed IP address. It's a static IP address that only belongs to a specific device and does not change when you are in different locations.
VPN service providers such as Private Internet Access can help you with these settings. This tool can help you control your online reputation and successfully manage your projects wherever you are. It is important to prevent different IP addresses from connecting to your website. With a dedicated/fixed IP address, VPN service, and secure access to a content management system, your project will remain secure.
Recover files damaged by a dangerous malware attack
Despite the fact that there are various circumstances that can cause data to be lost on a system, including accidental deletion, the most common reason people lose photos, documents, videos, and other important data is the infection of malware.
Some malicious programs can delete files and prevent the software from running smoothly. However, there is a greater threat from the dangerous viruses that can encrypt documents, system files, and images. Ransomware-type viruses focus on encrypting data and restricting users’ access to files, so you can permanently lose personal data when you download such a virus to your computer.
The ability to unlock encrypted files is very limited, but some programs have a data recovery feature. In some cases, the Data Recovery Pro program can help recover at least some of the data that has been locked by a virus or other cyber infection.