Uninstall CryptoWall 2.0 virus (Uninstall Guide) - 2016 updated
CryptoWall 2.0 virus Removal Guide
Description of CryptoWall 2.0 virus
The essential facts about CryptoWall 2.0 virus
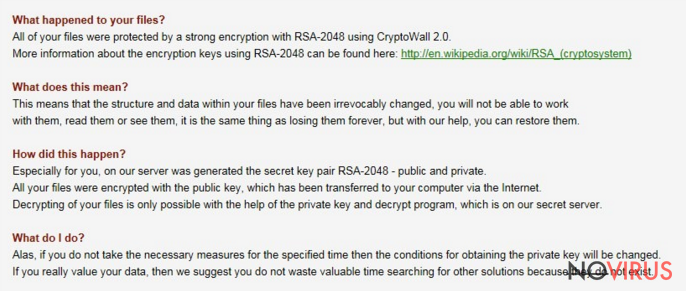
CryptoWall 2.0 virus is a treacherous ransomware which infects PCs and then locks out the valuable confidential information. However, this is only the beginning of major problems. The virus presents you a ‘solution’ – pay the required ransom in order to return the data. We highly discourage you to do make the transaction. You will pay the money, but you may never see the encrypted data again. Thus, brush away naïve hopes and face the reality. Consider of CryptoWall 2.0 removal before the virus paralyses your system completely. You can confront the virus by installing a reliable anti-spyware program, such as FortectIntego.
CryptoWall 2.0 has come into daylight after its predecessor CryptoWall has struck the virtual world. The original version targeted corporations and companies as well as individual users all around the world. The victims went spare after finding out that highly important data had been blocked. Desperate to retrieve the data, corporations had paid millions of pounds to the developers of the virus. Overall, the cyber criminals have managed to collect stunning amounts of money. Thus, it didn’t take too long for them to release the update version – 2.0.
The new version includes main updates:
• eliminating original files. While the original version encrypted the existing files, the latter deletes the original ones. In other words, in case you manage to retrieve the data, you receive the copies of the encrypted data.
• using Tor gateway. When a virus delivers a message informing of the deed, it instructs the victim to download a Tor browser and then to make the transaction. Likewise, such peculiarity burdens the detection of malware source.
• creating unique bitcoin payment address. In previous version, you could exploit the payment numbers of other users in order to retrieve the data, but now CryptoWall 2.0 malware creates unique wallet ID, thus forcing you to pay the money.
Though IT security specialists have almost managed to terminate the older version, cyber criminals pose new challenges by releasing more ransomware. If you got infected with the virus, it is necessary to remove CryptoWall 2.0 as soon as possible. Before terminating it, it is vital to know how the virus spreads.
How does the ransomware infect computers?
Like previous version, CryptoWall 2.0 ransomware mainly attacks users via spam attachments. Beware of the attached email with this file — ATTN: Invoice J-98223146. It seems like the message is sent from a tax company: ‘Please see the attached invoice (Microsoft Word Document) and remit payment according to the terms listed at the bottom of the invoice.’ If you notice any similar characteristics, do not open it! In any case, if you get a similar message with an added invoice, stay alert, as it may be a trap. If you have doubts whether the company sent you the invoice, you can always inquire them directly. Thus, the risk of getting infected with a ransomware decreases.
Can I remove CryptoWall 2.0?
Terminating CryptoWall 2.0 virus might not be an easy task if you opt for manual removal. If you do not specialise in programming, then automatic removal might be the right choice. After you install a powerful anti-spyware program it completes CryptoWall 2.0 removal. After it finishes the elimination, turn on your anti-virus program and scan the system anew. Make sure you update the anti-virus and anti-spyware programs daily. This time, the personal data might have been lost, but now you can back-up your data in order to prepare for possible future ransomware attacks.
Getting rid of CryptoWall 2.0 virus. Follow these steps
In-depth guide for the CryptoWall 2.0 elimination
Important! →
The elimination guide can appear too difficult if you are not tech-savvy. It requires some knowledge of computer processes since it includes system changes that need to be performed correctly. You need to take steps carefully and follow the guide avoiding any issues created due to improper setting changes. Automatic methods might suit you better if you find the guide too difficult.
Step 1. Launch Safe Mode with Networking
Safe Mode environment offers better results of manual virus removal
Windows 7 / Vista / XP
- Go to Start.
- Choose Shutdown, then Restart, and OK.
- When your computer boots, start pressing the F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) a few times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click the Start button and choose Settings.

- Scroll down to find Update & Security.

- On the left, pick Recovery.
- Scroll to find Advanced Startup section.
- Click Restart now.

- Choose Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.

- Choose 5) Enable Safe Mode with Networking.
Step 2. End questionable processes
You can rely on Windows Task Manager that finds all the random processes in the background. When the intruder is triggering any processes, you can shut them down:
- Press Ctrl + Shift + Esc keys to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes.
- Look for anything suspicious.
- Right-click and select Open file location.

- Go back to the Process tab, right-click and pick End Task.
- Delete the contents of the malicious folder.
Step 3. Check the program in Startup
- Press Ctrl + Shift + Esc on your keyboard again.
- Go to the Startup tab.
- Right-click on the suspicious app and pick Disable.

Step 4. Find and eliminate virus files
Data related to the infection can be hidden in various places. Follow the steps and you can find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive (C: is your main drive by default and is likely to be the one that has malicious files in) you want to clean.
- Scroll through the Files to delete and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Eliminate CryptoWall 2.0 using System Restore
-
Step 1: Restart your computer in Safe Mode with Command Prompt
Windows 7 / Vista / XP- Go to Start → Shutdown → Restart → OK.
- As soon as your computer starts, start pressing F8 key repeatedly before the Windows logo shows up.
-
Choose Command Prompt from the list

Windows 10 / Windows 8- Click on the Power button at the Windows login screen, and then press and hold Shift key on your keyboard. Then click Restart.
- Then select Troubleshoot → Advanced options → Startup Settings and click Restart.
-
Once your computer starts, select Enable Safe Mode with Command Prompt from the list of options in Startup Settings.

-
Step 2: Perform a system restore to recover files and settings
-
When the Command Prompt window appears, type in cd restore and press Enter.

-
Then type rstrui.exe and hit Enter..

-
In a new window that shows up, click the Next button and choose a restore point that was created before the infiltration of CryptoWall 2.0 and then click on the Next button again.


-
To start system restore, click Yes.

-
When the Command Prompt window appears, type in cd restore and press Enter.
It is strongly recommended to take precautions and secure your computer from malware attacks. To protect your PC from CryptoWall 2.0 and other dangerous viruses, you should install and keep a powerful malware removal tool, for instance, FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes.
How to prevent from getting ransomware
A proper web browser and VPN tool can guarantee better safety
As online spying becomes an increasing problem, people are becoming more interested in how to protect their privacy. One way to increase your online security is to choose the most secure and private web browser. But if you want complete anonymity and security when surfing the web, you need Private Internet Access VPN service. This tool successfully reroutes traffic across different servers, so your IP address and location remain protected. It is also important that this tool is based on a strict no-log policy, so no data is collected and cannot be leaked or made available to first or third parties. If you want to feel safe on the internet, a combination of a secure web browser and a Private Internet Access VPN will help you.
Reduce the threat of viruses by backing up your data
Due to their own careless behavior, computer users can suffer various losses caused by cyber infections. Viruses can affect the functionality of the software or directly corrupt data on your system by encrypting it. These problems can disrupt the system and cause you to lose personal data permanently. There is no such threat if you have the latest backups, as you can easily recover lost data and get back to work.
It is recommended to update the backups in parallel each time the system is modified. This way, you will be able to access the latest saved data after an unexpected virus attack or system failure. By having the latest copies of important documents and projects, you will avoid serious inconveniences. File backups are especially useful if malware attacks your system unexpectedly. We recommend using the Data Recovery Pro program to restore the system.







